As crypto ownership moved beyond exchanges, users needed a safer way to hold their own keys without leaving everything exposed on an internet-connected app or browser. That is where hardware wallets became important: they were built to keep private keys in a more isolated environment, reducing exposure to online attacks. At the same time, hot wallets remained useful because they are faster, easier to access, and better suited to smaller balances or frequent transactions.
In practice, many users end up using both, keeping spending funds in a hot wallet and longer-term holdings in cold storage. For anyone managing meaningful amounts of crypto, security quickly becomes the deciding factor. That is exactly what this article is about: comparing the most secure crypto wallets in 2026, how their security models differ, and which type of wallet makes the most sense for your needs.
Editor's Note (April 16, 2026): We fully updated this article in April 2026 to reflect the latest wallet lineup, revised security positioning, and a sharper breakdown of how different wallet models fit different users. This refresh also improves the comparison table, updates our recommendations across hardware, air-gapped, seedless, and Bitcoin-only wallets, and clarifies the tradeoffs that matter most when choosing a secure wallet in 2026.
Comparison Table: Best Secure Wallets at a Glance
Here is a quick side-by-side view of the wallets covered in this guide, focused on the security model, recovery approach, connectivity, and the kind of user each one suits best.
Wallet | Type | Security model | Recovery method | Connectivity | Best for | Main tradeoff |
|---|
ELLIPAL Titan | Hardware wallet | Air-gapped design, QR signing, secure element | Seed phrase backup | QR only for signing | Users who want fully isolated cold storage | Slower and less convenient than connected wallets |
Ledger Flex | Hardware wallet | Secure Element, on-device verification | Recovery phrase | USB-C, Bluetooth, NFC | Most users who want a secure all-rounder | Expensive and not air-gapped |
Trezor Safe 5 | Hardware wallet | Open-source design, Secure Element, PIN/passphrase | Standard wallet backup | USB-C | Users who value transparency | Less flexible for mobile-first use |
SafePal S1 | Hardware wallet | Air-gapped QR signing, Secure Element | 12, 18, or 24-word seed phrase | QR scans, USB-C for charging | Budget-conscious users who want air-gapped security | Less premium overall experience |
Tangem | Seedless hardware wallet | Private keys stored in card, app-based access | Backup cards | NFC | Beginners who want simplicity | No built-in screen for transaction review |
Zengo | Seedless hot wallet | MPC-based signing | Email, 3FA, 3D FaceLock, recovery file | Mobile app | Users who want seedless mobile security | Not offline like a hardware wallet |
Coinbase Wallet | Hot wallet | User-controlled keys, app security locks | 12-word recovery phrase | Mobile app, browser extension | Beginners starting with self-custody | Higher exposure than hardware wallets |
OneKey Pro | Hardware wallet | 4× EAL 6+ secure chips, clear signing preview, multi-sig support | 24-word recovery phrase, optional passphrase | USB-C, Bluetooth, QR signing | Multi-chain users who want premium features | Expensive and more complex |
COLDCARD | Bitcoin-only hardware wallet | Dual Secure Elements, offline workflows, air-gap support | 24-word seed phrase, optional passphrase | USB-C, NFC, microSD | Experienced Bitcoin-only users | Not suitable for altcoins, NFTs, or DeFi |
The Best Secure Crypto Wallets in 2026
The safest wallet depends on what you are trying to protect against. Some users want broad asset support with a polished hardware experience, some care most about open-source transparency, some want a cheaper air-gapped setup, and some want to avoid seed-phrase handling altogether.
Our picks cover those different needs without losing sight of the basics: secure key storage, clear transaction verification, and a recovery method you can realistically manage.
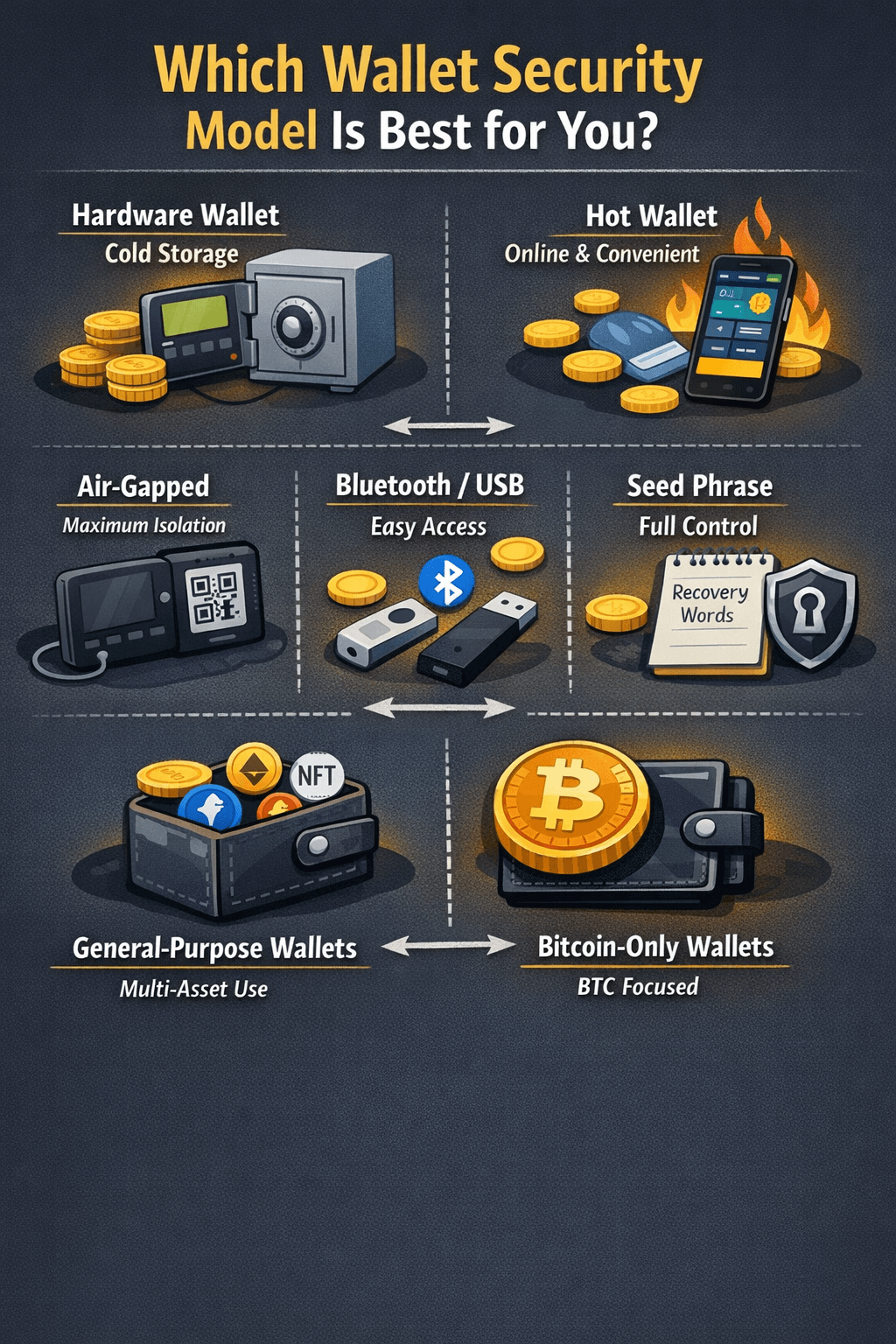
Which Wallet Security Model Is Best for You?
The best wallet security model depends less on marketing labels and more on your threat model: what you are protecting, how often you transact, and how much complexity you can realistically handle.
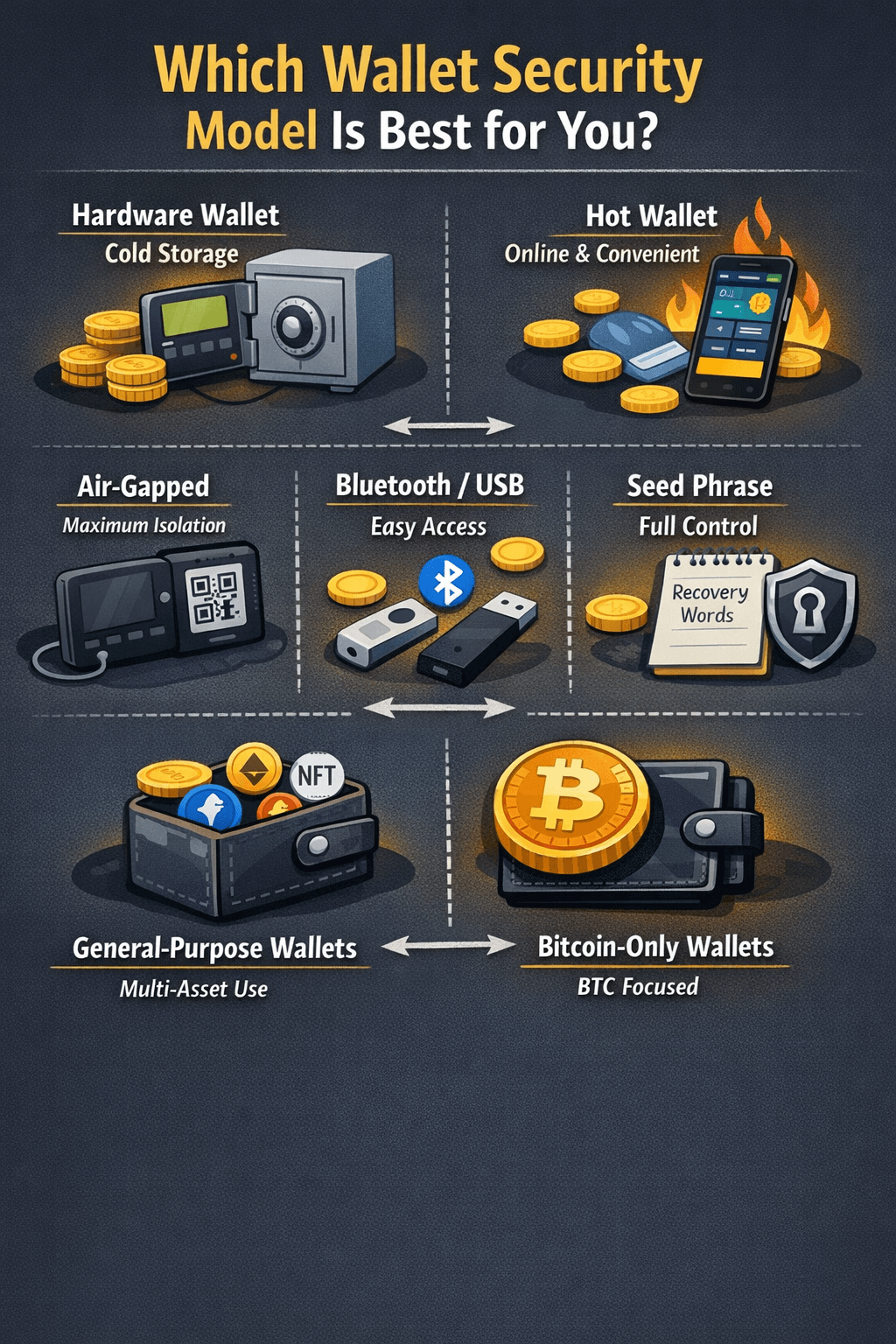
For most, a Hot Wallet is Fine for Smaller Working Balances, while a Hardware Wallet is the Better Fit for Serious Savings
Hardware vs Hot Wallets
The longstanding debate on software wallets vs hardware wallets, also referred to as hot and cold wallets, depends basically on the trading volume, frequency, and holding strategy. A hardware wallet keeps your private keys in an offline signing environment, which generally makes it the better choice for larger holdings and long-term storage. A hot wallet, by contrast, is easier to use and often free, but it lives on an internet-connected device, so convenience comes with more exposure.
For most beginners, a hot wallet is fine for smaller working balances, while a hardware wallet is the better fit for serious savings.
Also Read
Air-Gapped vs Bluetooth vs USB
This is really a tradeoff between isolation and convenience. An air-gapped wallet removes standard data connections and usually signs through QR codes, which reduces remote attack paths. That is why wallets like ELLIPAL Titan appeal to users who want strong offline separation for broader crypto holdings. Bluetooth and USB-based wallets can still be very secure, but they are built for smoother everyday use rather than maximum isolation.
Seed Phrase vs Seedless Recovery
Traditional wallets rely on a seed phrase, which gives you full control but also full responsibility. Lose it, and recovery may be impossible. Seedless models try to reduce that single point of failure. For example, Zengo’s MPC approach and 3-factor recovery (3FA) are designed for users who want self-custody without handling a written backup phrase.
General-Purpose Security vs Bitcoin-Only Security
Some wallets aim to secure many assets well, while others narrow the focus. COLDCARD is built specifically for Bitcoin users who want tighter controls and a smaller attack surface. That makes it a stronger fit for experienced BTC holders, while a general-purpose wallet is usually better for users holding altcoins, NFTs, or using DeFi.
How We Chose These Wallets
We selected these wallets based on the security features and design choices described in their official documentation, focusing on how well each option fits different user needs rather than trying to force a single winner.
What we looked at
- Security architecture: how the wallet stores keys and protects signing
- Recovery method: whether it uses a seed phrase, seedless recovery, or another backup model
- Transaction verification: how clearly users can review and approve transactions
- Firmware and update model: how the wallet handles updates and ongoing security maintenance
- Connectivity design: whether it relies on air-gapped QR signing, USB, Bluetooth, NFC, or a mix
- Asset scope: whether it is built for broad multi-chain use or a narrower use case like Bitcoin-only storage
Why that matters
We also considered how well each wallet matches different threat models.
- Some users will prefer the stronger offline isolation of an air-gapped wallet
- Others may value the transparency of open-source development
- Some may prioritize the simplicity of a seedless recovery model
- Bitcoin-first users may prefer the narrower attack surface of a Bitcoin-only wallet
The goal was not to reward the wallet with the most features, but to identify the options that make the most sense for different security priorities.
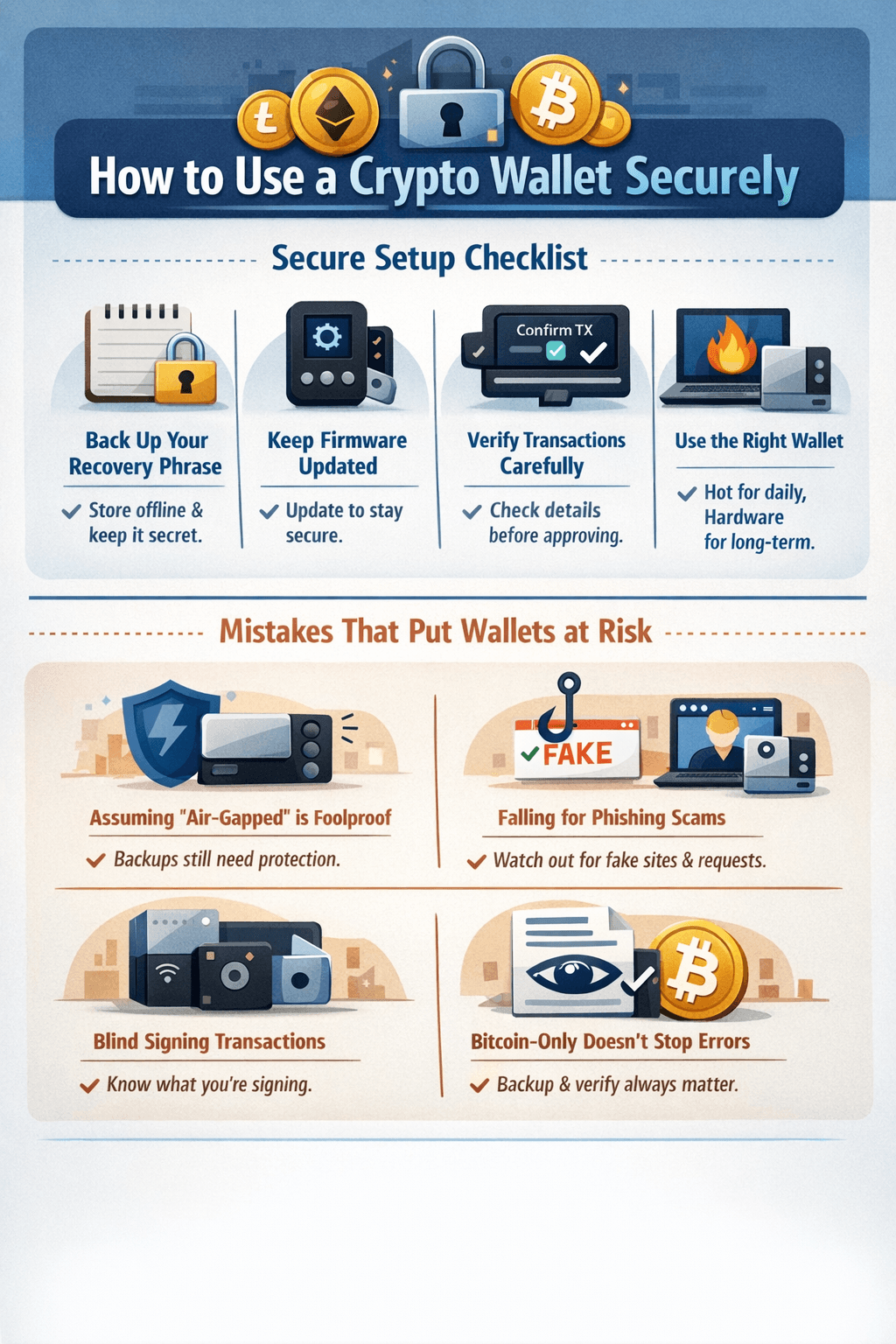
How to Use a Crypto Wallet Securely
Even the most secure wallet can be undermined by poor setup or careless signing. In practice, wallet security is a mix of the device, the recovery method, and the habits of the person using it.
Even the most Secure Wallet can be Undermined by Poor Setup or Careless Signing
Secure Setup Checklist
- Back up your recovery phrase properly: If your wallet uses a recovery phrase, store it offline and never share it. Whoever has the phrase can access the wallet, and losing it can mean losing access permanently.
- Keep firmware updated: Firmware updates are important for long-term security, and you should have your wallet backup available before updating in case the device needs to be restored.
- Verify transactions carefully: A hardware wallet is most useful when you actually read what appears on the device before approving it, rather than treating confirmation like clicking “accept” on a pop-up.
- Use the right wallet for the job: Hot wallets are usually better for smaller working balances, while hardware wallets are generally the safer home for long-term holdings.
Mistakes That Put Wallets at Risk
- Treating air-gapped as foolproof: An air-gapped wallet reduces some attack paths, but it does not protect a badly stored backup or careless transaction approval.
- Ignoring phishing: Scams often involve fake websites, fake support, or requests for your recovery phrase. No legitimate provider should ask for it. Stay vigilant and be sure you trust the source before proceeding.
- Blind signing without understanding it: Blind signing is approving a transaction without seeing clear human-readable details, which can expose users to malicious smart-contract interactions. You must understand it and its application to minimize risk.
- Assuming Bitcoin-only wallets remove human error: Even a narrow security model still depends on proper backup hygiene and careful verification.
On top of this, we suggest that you go through our guides on crypto scams and mitigating risk in trading.
Final Verdict: Which Secure Wallet Should You Choose?
There is no single “most secure” wallet for everyone, because the right choice depends on the balance you want between isolation, convenience, recovery design, and asset support.
- Choose Ledger Flex if you want the best all-round secure hardware wallet for everyday use.
- Choose Trezor Safe 5 if open-source transparency and a more reviewable security model matter most to you.
- Choose ELLIPAL Titan if you want an air-gapped cold wallet for broader crypto holdings.
- Choose COLDCARD if you are Bitcoin-only and want tighter controls with a more minimal attack surface.
- Choose SafePal S1 if you want cheaper air-gapped security.
- Choose Tangem or Zengo if you want a seedless experience that reduces backup friction.
- Choose Coinbase Wallet if you want a simple hot wallet to get started with self-custody.
For most people, the real goal is not finding the wallet with the most features. It is finding the one whose security model you will actually understand and use properly. A strong wallet setup, careful transaction verification, and safe backup habits usually matter more than chasing the most extreme option on paper.

 For most, a Hot Wallet is Fine for Smaller Working Balances, while a Hardware Wallet is the Better Fit for Serious Savings
For most, a Hot Wallet is Fine for Smaller Working Balances, while a Hardware Wallet is the Better Fit for Serious Savings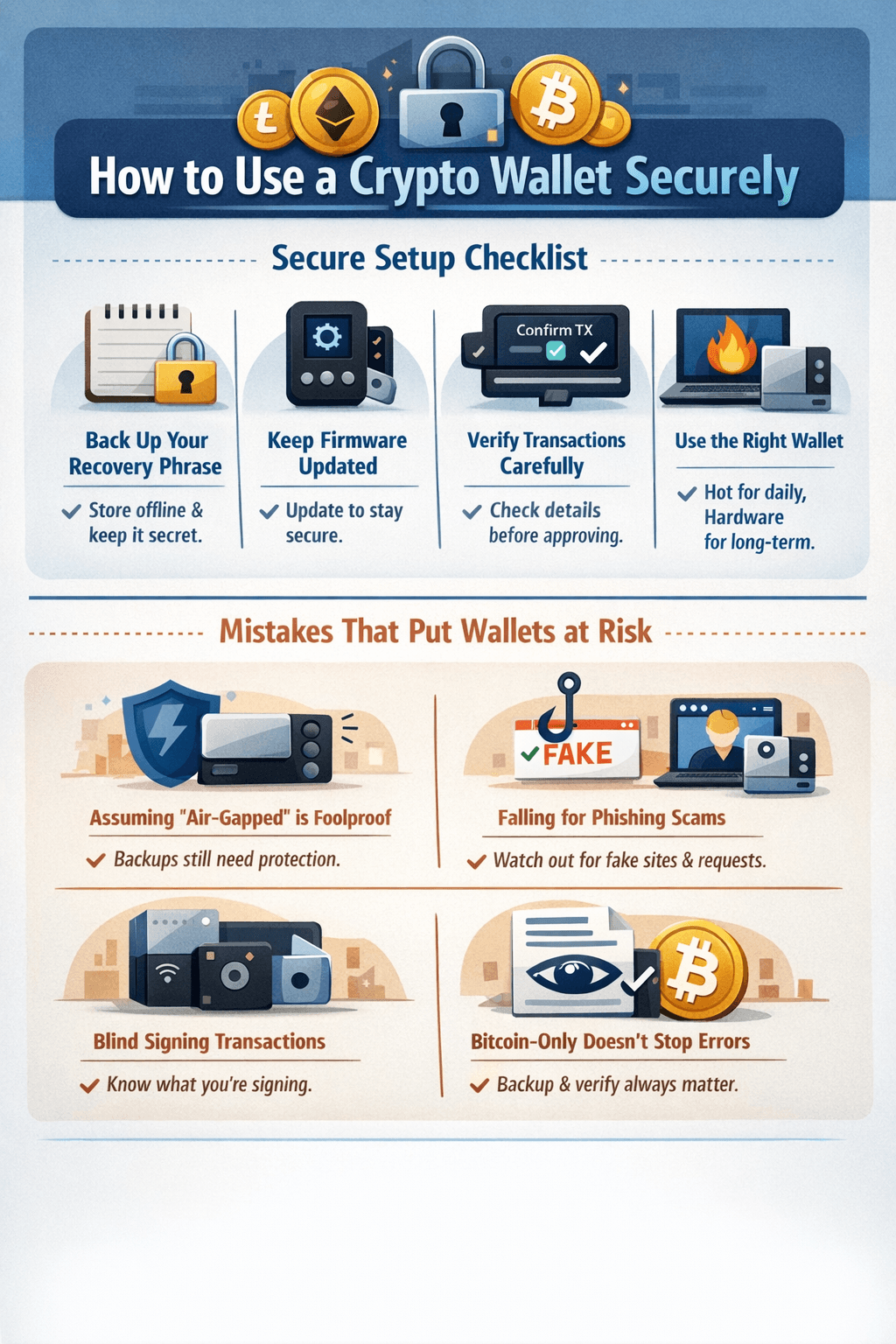 Even the most Secure Wallet can be Undermined by Poor Setup or Careless Signing
Even the most Secure Wallet can be Undermined by Poor Setup or Careless Signing



