Quick Verdict
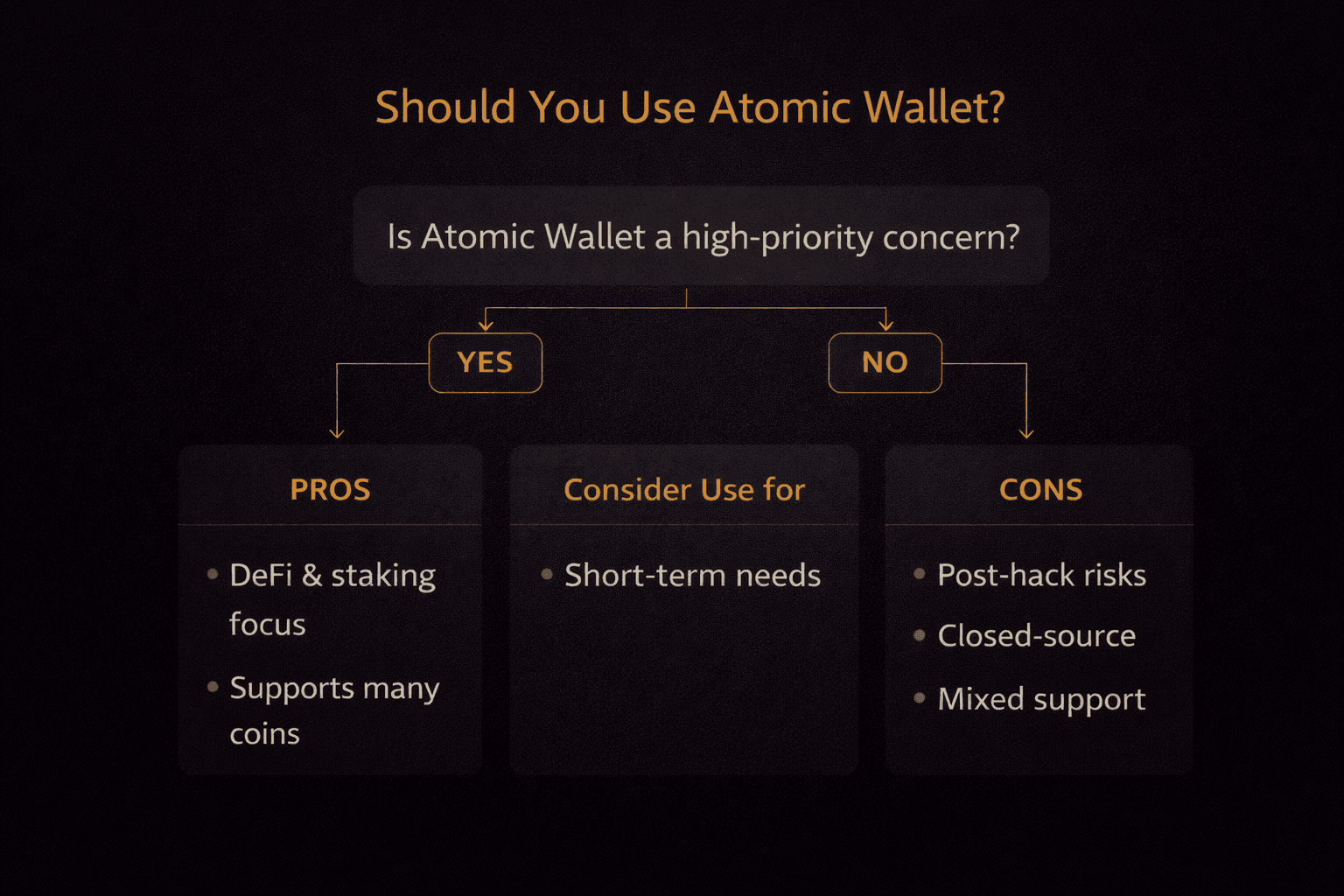
Atomic Wallet is best treated as a convenience hot wallet for small balances. It is not a strong fit for long-term storage or serious holdings, especially if you prioritize maximum transparency and auditability.
Non-custodial (keys stored locally)
Supports 1,000+ assets
Desktop + mobile + Linux support
Built-in swaps (no exchange hop)
In-app staking for select coins
Simple “all-in-one” interface
Non-custodial (keys stored locally)
Supports 1,000+ assets
Desktop + mobile + Linux support
Built-in swaps (no exchange hop)
In-app staking for select coins
Simple “all-in-one” interface
2023 hack still a major trust hit
Partially closed-source (harder to verify)
Not great for heavy DeFi / DApp power users
2023 hack still a major trust hit
Partially closed-source (harder to verify)
Not great for heavy DeFi / DApp power users
In crypto, the most dangerous word isn’t “hack.” It’s “convenient.” Convenience lowers friction, and lower friction almost always expands the attack surface. Atomic Wallet built its reputation on removing friction, multi-asset support, in-app swaps, staking from one dashboard, desktop, and mobile parity.
For many users, that simplicity felt like control. But after the events of 2023, the conversation shifted. Control without verifiability became the real question.
This review does not approach Atomic Wallet from a marketing lens. It approaches it from a risk lens. We examine how its architecture works, what the breach revealed, how transparent the response has been, and whether its tradeoffs make sense in 2026’s security environment. The goal is to determine where Atomic fits in a modern crypto setup and where it clearly does not.
Editor’s Note (Feb. 27, 2026): We fully updated this Atomic Wallet review in February 2026 to reflect the wallet’s current feature set, fee structure, platform support, and real-world risk considerations in today’s security landscape. This revision also expands and clarifies the June 2023 incident and its ongoing trust implications, updates reputation signals (including recent user-review snapshots), and reframes our verdict using a risk-first lens.
Atomic Wallet is best treated as a convenience hot wallet for small balances. It is not a strong fit for long-term storage or serious holdings, especially if you prioritize maximum transparency and auditability.
Overall safety stance (post-hack reality): Atomic Wallet is acceptable as a convenience hot wallet, but not suitable for serious or long-term holdings.
Trustpilot rating: ★★★☆☆ 3.2/5 (checked February 2026)
Major concern: 2023 breach involving significant user losses, plus a partially closed-source architecture that increases the trust burden.
If you frame it by amount at risk, the decision becomes clearer.
Atomic Wallet is a non-custodial, multi-asset software wallet that allows users to store, swap, and stake cryptocurrencies while retaining control of their private keys. It is not an exchange, not a custodial service, and not a hardware device. Its core proposition is simple: you hold the keys, and therefore you hold the assets.
Before evaluating features, yields, or integrations, custody must be clarified. In crypto, the defining question is always the same: who controls the private key? Everything else flows from that answer.
Atomic positions itself firmly in the self-custody category. That means it does not hold user funds, does not manage accounts centrally, and does not operate a recoverable login system like a traditional fintech app. The wallet software acts as a client-side interface for generating and managing private keys tied to blockchain addresses.
 Understanding Atomic Wallet Self Custody Model
Understanding Atomic Wallet Self Custody ModelAtomic Wallet operates under a non-custodial custody model, meaning private keys are generated and stored locally on the user’s device rather than on company servers. During initial setup, the application creates a 12-word recovery phrase that represents the master key to the wallet.
According to Atomic’s official documentation, both the private keys and the recovery phrase are generated client-side. They are not transmitted to or stored on Atomic’s infrastructure. This aligns with the broader industry definition of self-custody: control of the private key equals control of the assets.
In practical terms, here is how that structure works:
If the seed phrase is lost, access to funds is permanently lost. There is no support ticket, no identity verification fallback, and no internal override. That is the tradeoff embedded in self-custody.
To make sure your private keys stay safe offline and online, this guide on securing your seed phrase is worth reading.
Atomic states that wallet data stored on the device is encrypted locally. This encryption protects wallet files against basic device-level access attempts, such as someone browsing local directories. However, encryption at rest does not replace proper key management. If a device is compromised by malware or if a seed phrase is exposed, encryption does not create insurance or custodial safeguards. It reduces certain risks; it does not eliminate them.
The custody structure is therefore clear and binary: full user control paired with full user responsibility.
With the custody model defined, the next question becomes practical rather than theoretical. Where can you actually use the wallet?
Atomic Wallet is available across Windows, macOS, Linux, iOS, and Android. This cross-platform coverage makes it accessible to users who prefer managing assets on a desktop while retaining mobile visibility and control.
The desktop application remains a core component of the experience. Unlike extension-first wallets such as MetaMask or Rabby, Atomic is not primarily built around injected browser Web3 functionality. Its architecture centers on a standalone app environment rather than deep browser-level smart contract interaction.
That distinction affects how it feels in daily use.
Atomic also has a browser-based Web3 option, including a Chrome extension listing and an official “Web3 wallet” page. In practice, this is best treated as a basic dApp connector: it can help you connect and sign for supported networks, but it’s typically less feature-complete than extension-first wallets like MetaMask or Rabby for day-to-day DeFi
For storage, portfolio tracking, built-in swaps, and supported staking assets, the desktop and mobile apps are sufficient. Users who want a consolidated interface for holding multiple coins across chains often appreciate this design.
For heavy DeFi usage, however, the limitations become clearer. Atomic does not offer the same native browser-extension integration depth as wallets designed specifically for Web3 contract interaction. Direct connection to emerging dApps, advanced contract permissions, and rapid switching between networks can feel less seamless compared to extension-native alternatives.
In simple terms:
With custody and platform coverage established, it helps to compress everything into a high-level functional snapshot.
Atomic Wallet combines self-custody storage, in-app token swaps, and staking inside a single interface, designed to reduce friction for everyday crypto management.
Here is the structural overview:
| Feature | Snapshot |
| Storage | Non-custodial storage (keys generated and kept on your device). |
| Swaps | In-app swaps via third-party liquidity providers/aggregators (priced into the quote). |
| Staking | In-app staking for select PoS assets (yields/lockups depend on the chain). |
| Fiat on-ramps | Buy crypto via integrated third-party payment providers (KYC may apply at provider level). |
| Extension | Browser-based Web3 option exists, but typically less DeFi-native than extension-first wallets (e.g., MetaMask/Rabby). |
| Token support | Markets support for 1000+ coins and tokens (feature availability varies by asset/network). |
The swap functionality operates through external exchange partners rather than a centralized exchange operated by Atomic itself. When a user executes a swap, liquidity is sourced through third-party providers, and pricing may include provider spreads.
Fiat purchases are also handled through integrated third-party payment processors. Depending on the jurisdiction, card purchases or bank transfers may require KYC at the provider level. Atomic facilitates the interface, but it does not directly act as the regulated on-ramp entity.
The value proposition, then, is convenience through aggregation: multiple blockchains, token management, staking access, and exchange routing consolidated into one application. The tradeoff is that deeper Web3 tooling and full open-source transparency are not its core strengths.
Understanding that balance is essential before deciding whether Atomic fits into your personal wallet architecture.
 Atomic Wallet Comes with Multi Asset Storage Swaps And Staking
Atomic Wallet Comes with Multi Asset Storage Swaps And StakingOnce custody and platform access are clear, the real question becomes functional value. A wallet earns its place not by what it claims to support, but by how smoothly it lets you manage, move, and grow assets without constant workarounds.
Atomic Wallet’s strength lies in consolidation. It brings multi-chain storage, in-app swaps, staking, and fiat access into a single environment. That approach favors convenience and simplicity over modular specialization.
Let’s examine where it performs well, and where trade-offs quietly exist.
Atomic Wallet supports over 1,000 coins and tokens. In practice, that includes major Layer 1 networks such as BTC, ETH, BNB, SOL, ADA, XRP, TRX, and ATOM, alongside a broad range of ERC-20 tokens.
The asset count matters less than the structure behind it.
Atomic generates native addresses for supported blockchains rather than simply tracking balances. That means users can actively send, receive, and manage funds across multiple chains within a single interface. For Ethereum-based assets, custom tokens can be manually added using contract addresses in line with the ERC-20 standard, allowing visibility even for tokens that aren’t preloaded by default.
The practical outcome is portfolio consolidation. Instead of splitting assets across separate chain-specific wallets, users can:
Store Bitcoin and altcoins together
Track Ethereum tokens without switching wallets
Add niche ERC-20 tokens manually
View balances across chains in one dashboard
This does not eliminate network risk or smart contract risk. What it reduces is operational fragmentation. For long-term holders or diversified portfolios, that consolidation is genuinely useful.
Asset storage solves one problem. Asset movement introduces another.
Atomic Wallet integrates an in-app exchange mechanism that operates through third-party liquidity providers. It does not run its own centralized exchange, nor does it custody funds during the swap process.
When a user initiates a swap, the wallet routes the request through an external partner. The quoted rate typically includes both the market spread and the provider’s fee, bundled into a single displayed conversion rate.
What this model prioritizes is convenience.
You do not need to deposit assets into an exchange. You do not need to wait for confirmations before trading. You do not need to withdraw back into self-custody afterward. The transaction completes within the wallet interface.
However, convenience and optimal execution are not the same thing. Aggregator-based swaps are rarely the cheapest route available, especially for larger trades where spread differences become meaningful. Professional traders seeking tight pricing or advanced order types will still prefer centralized exchanges or on-chain DEX routing tools.
Looking for decentralized platforms with high volume and low fees? Read this overview of top DEX protocols for up-to-date insights.
Atomic’s swap function is best understood as a friction-reduction layer. It streamlines simple portfolio adjustments rather than competing with dedicated trading platforms.
Crypto-to-crypto movement is covered. The next logical layer is fiat entry.
Atomic Wallet integrates fiat purchases through external payment processors. The wallet itself does not directly handle card payments or bank transfers.
When users buy crypto with fiat inside the app, identity verification may be required depending on jurisdiction and provider policy. KYC obligations apply at the payment partner level rather than the wallet level.
Fee transparency can be less obvious here. The total cost generally reflects:
Card processing charges
Provider markup
Embedded spread between market price and quoted rate
Unlike centralized exchanges that itemize trading fees, on-ramp providers often present a single conversion figure. The effective cost can therefore appear higher than direct exchange funding routes.
That said, the appeal is clear. Users can purchase crypto and have it delivered directly into self-custody without needing to withdraw from an exchange afterward. For beginners or those prioritizing simplicity, that streamlined flow has value.
Once assets are inside the wallet, yield becomes the next consideration.
Atomic Wallet supports staking for selected proof-of-stake networks, including major examples like ADA, SOL, ATOM, XTZ, and TRX.
Before choosing a network for long-term staking or mining, read this explainer on PoW versus PoS frameworks.
Staking operates through delegated validator models native to each blockchain. Users delegate tokens to validators and receive rewards based on network participation and validator performance.
Two structural realities are important here.
First, validator commissions apply. Rewards shown inside the wallet represent network-level yield before commission adjustments are factored in. Second, unbonding periods are defined by the underlying blockchain protocol, not by Atomic Wallet.
For example:
Cosmos (ATOM) typically requires around 21 days to unbond
Solana (SOL) unbonding generally spans 2–3 days
Tezos (XTZ) operates on multi-cycle reward delays
Cardano (ADA) follows epoch-based staking without a strict token lock
During unbonding, tokens cannot be transferred or sold. Liquidity constraints are a protocol rule, not a wallet limitation.
Atomic simplifies the delegation process by embedding it directly inside the interface. It does not modify network economics or override lockup mechanics. Users still carry validator risk and network-level volatility.
Staking adds passive yield. But Web3 interaction goes deeper than delegation.
Atomic Wallet was not designed as a browser-extension-first wallet. Its Web3 capabilities exist, but they are not as extensive as extension-native competitors.
Users can sign transactions, manage assets, and interact with supported staking modules. However, deep integration with browser-based decentralized applications is more limited compared to wallets like MetaMask that inject directly into Web3 environments.
This distinction becomes noticeable for users who frequently:
Mint NFTs
Interact with DeFi lending protocols
Adjust liquidity positions
Configure custom RPC endpoints
For long-term holders and moderate users, this limitation may never become relevant. For advanced DeFi participants who rely on daily contract interactions, extension-native wallets typically offer smoother interoperability.
Atomic’s identity is clear: it is a consolidated asset management wallet with integrated convenience features. It is not optimized as a power-user DeFi terminal.
Fees are where convenience either proves its value or quietly becomes expensive. Atomic Wallet does not charge users for simply holding assets, but the moment you transact, swap, or buy crypto with fiat, costs appear. The key is understanding which layer is charging you and why.
Instead of treating fees as a single number, it helps to separate them into structural buckets. Once you do that, the math becomes clearer.
 Real World Swap Costs Inside Atomic Wallet
Real World Swap Costs Inside Atomic WalletEvery transaction inside Atomic Wallet falls into one of three categories: network fees, swap fees, or fiat processing fees.
Whenever you send assets on-chain, you’re paying the blockchain itself (e.g., Ethereum gas, Bitcoin miner fees). Atomic says it doesn’t add extra send/receive charges beyond the chain fee in its explanation of transaction fees.
These fees fluctuate with congestion. Ethereum gas during high-demand periods can spike dramatically, while quieter windows may reduce costs significantly.
In short: if you’re moving crypto across a blockchain, you’re paying that network directly.
Atomic’s built-in swap routes orders through third-party providers. Atomic states swaps include a 0.5% Atomic fee plus the swap partner’s commission in its breakdown of swap fees. Atomic also notes it doesn’t offer fixed-rate swaps, meaning the quote can change with market movement while the swap is processing.
You won’t always see a clean percentage breakdown. In practice, the “cost” often shows up as a mix of the explicit fee plus the spread embedded in the quote.
For example, if ETH is trading at $3,000 and you swap $1,000 worth of another asset into ETH, the quote might effectively price ETH closer to $2,940–$2,970 once routing and spread are baked in. The larger the swap, the more noticeable that gap becomes.
Fiat purchases inside Atomic are handled by external payment processors, and identity checks can apply at the provider level under Atomic’s AML/KYC policy.
Atomic states crypto purchases can carry a flat 5% fee with a $10 minimum in its article on fees to buy cryptocurrencies. Atomic’s help center also describes a 7% commission with a $10 minimum in its exchange fee explainer, suggesting costs can vary depending on route, provider, and transaction type.
Small purchases are disproportionately affected because fixed minimums get compressed into the total amount. A $100 card purchase can become expensive quickly if a $10 minimum applies before any bank charges.
Understanding these three buckets transforms fees from “mysterious wallet cost” into predictable trade-offs.
Atomic swaps bundle costs into the quote (plus the explicit 0.5% fee + partner commission), while exchanges usually show explicit spot trading fees.
| Scenario | Atomic swap fee structure | Exchange spot fee baseline (official pages) | What this usually means |
| $200 swap | 0.5% Atomic fee ($1) + partner commission + spread (quote varies) | Binance spot fees often start around 0.10% (~$0.20). Bybit’s fees overview describes base spot fees in its docs. Coinbase Exchange fee schedule varies by tier and can be higher than 0.10%. | Exchanges can be cheaper on trading fees, but you add deposit/withdraw steps. |
| $1,000 swap | 0.5% Atomic fee ($5) + partner commission + spread (larger size can amplify spread) | Binance spot fees around 0.10% (~$1) at base tier; Bybit fee docs similar; Coinbase Exchange fees can be meaningfully higher depending on tier. | The “convenience premium” is usually spread + partner commission on top of the explicit fee. |
The trade-off is simple: Atomic can save steps (no exchange deposit, no trading UI, no withdrawal back to self-custody), but you typically pay for that convenience through spread and routing costs.
Cost control inside Atomic is mostly about strategic usage rather than hidden settings.
Avoid frequent small fiat purchases. Minimums like the $10 floor described in Atomic’s buy fee article can make small purchases expensive in percentage terms.
Compare swap quotes before confirming. Because Atomic doesn’t offer fixed-rate swaps, checking the in-app quote against a live market price helps you understand what spread you’re paying.
Separate functions: Use exchanges for trading and wallets for storage. Executing trades on a low-fee exchange and withdrawing to Atomic for holding can reduce fee drag (but remember withdrawals add their own costs).
Time your network transactions. On congested networks, waiting can materially reduce gas costs.
Marketing language around wallet security tends to blur into slogans: “encrypted,” “military-grade,” “fully secure.” None of that tells you how risk actually behaves.
Security in a non-custodial wallet like Atomic is not about corporate guarantees. It is about architecture, device hygiene, and user behavior. If you understand those layers clearly, you understand the real risk profile.
Let’s break it down without hype.
Atomic Wallet follows a standard non-custodial model built around a 12-word recovery phrase generated during wallet creation. That phrase is the root of control. Everything else, the interface, the password, the device, is secondary.
When you create a wallet, the private keys are generated locally on your device and encrypted. The 12-word seed phrase is shown once and must be stored offline. That phrase is not stored on Atomic’s servers, and there is no cloud recovery mechanism tied to your email.
The password you set inside the app is different from the seed phrase. It encrypts access to the wallet interface on that specific device. It does not replace the seed phrase, and it cannot recover funds independently.
The restore flow works like this:
Once the phrase is validated, the wallet regenerates all associated addresses and balances by deriving keys from the seed.
This is standard hierarchical deterministic wallet behavior. It means your funds are never tied to a specific device. They are tied to the seed phrase.
Now consider the uncomfortable question: what happens if your device is compromised?
If malware accesses your unlocked wallet while it is open, it may initiate transactions. If a keylogger captures your seed phrase during setup or restoration, funds can be drained from anywhere in the world. If your computer is infected and the clipboard content is manipulated, outgoing addresses can be altered without you noticing.
Atomic encrypts local wallet data. That protects against someone casually browsing files. It does not protect against an actively compromised operating system.
Device security becomes part of wallet security. And that leads directly into threat modeling.
Non-custodial wallets shift responsibility to the user. That increases sovereignty, and increases attack surface.
The most common real-world risks are not exotic protocol hacks. They are endpoint attacks.
Malware and keyloggers remain one of the largest risks. If malicious software monitors keystrokes or clipboard data, it can capture seed phrases or redirect transactions. Clipboard hijacking, in particular, has been widely documented in crypto-targeted malware strains that automatically replace copied wallet addresses with attacker-controlled ones.
Fake apps and phishing clones are another persistent issue. Attackers frequently publish counterfeit wallet downloads or browser extensions that mimic legitimate interfaces. Installing a malicious build and entering a seed phrase effectively hands control to the attacker instantly.
Social engineering continues to evolve. Users are tricked into “verifying” seed phrases via email, Telegram, Discord, or fake support portals. No legitimate wallet provider will ever ask for your recovery phrase. Entering it anywhere outside the restore flow is effectively surrendering control.
Unlike centralized exchanges, there is no fraud desk or insurance claim once funds leave your wallet via a signed transaction.
This is not unique to Atomic. It is inherent to self-custody.
Understanding that difference is critical: the biggest risks sit outside the wallet software itself.
Security discussions become clearer when we define boundaries.
Atomic Wallet is not a hardware wallet. Your private keys live on an internet-connected device. That inherently carries more exposure risk than signing transactions offline with a dedicated hardware device.
Atomic Wallet is not insured custody. There is no institutional backstop covering user losses from compromised devices or exposed seed phrases.
Atomic Wallet does not provide guaranteed recovery. If you lose your 12-word phrase, there is no company override. If someone else obtains it, they control your funds permanently.
Those constraints are not flaws. They are properties of self-custody.
The trade-off is simple: you eliminate exchange counterparty risk, but you assume personal operational risk.
In 2026, with phishing sophistication increasing and malware kits targeting crypto users becoming more automated, this distinction matters more than ever. Wallet security is no longer just about encryption strength. It is about user discipline, device hygiene, and clear threat awareness.
Atomic provides the structure for self-custody. It does not provide immunity from user error.
 Inside The 2023 Atomic Wallet Breach
Inside The 2023 Atomic Wallet BreachThis is the section that determines whether Atomic Wallet is viewed as a recoverable incident story or a structural red flag.
Security architecture matters in theory. A live breach is where theory meets reality. What happened in early June 2023 is still the single most important reputational event in Atomic’s history, and it continues to influence how users evaluate the wallet in 2026.
Let’s walk through it carefully, separating verified facts from narrative drift.
In early June 2023, multiple Atomic Wallet users began reporting unauthorized withdrawals from their wallets. Funds were drained without users initiating transactions, and in many cases, without signs of phishing or obvious seed phrase exposure.
The earliest public reports surfaced around June 3–4, 2023. Over the following days, on-chain investigators began aggregating affected addresses and estimating losses.
Public estimates varied. Blockchain analysis firms and independent researchers tracked losses in the range of approximately $35 million to over $200 million, depending on attribution scope and token valuation at the time. The number fluctuated because not all compromised addresses were immediately linked, and not all assets were equally traceable.
Atomic acknowledged the incident publicly and stated that fewer than 1% of its users were affected. However, because Atomic does not publish detailed user metrics or a full forensic report, the exact scope remains partly opaque.
Why do users still care in 2026?
Because this was not a centralized exchange hack. It was a non-custodial wallet breach affecting end-user funds. That raises a more uncomfortable question: how were private keys exposed in a model that claims local generation and encryption?
The answer is still not conclusively settled in public documentation.
The timeline is important because response speed and clarity matter during incidents.
June 3, 2023: Atomic says its support team began receiving reports of unauthorized transactions and it warned users via social channels, while halting downloads/updates as a precaution.
June 4–5, 2023: Public reporting and on-chain tracking accelerated as more users reported drained wallets and investigators began clustering affected addresses.
June 13, 2023: Elliptic reported losses exceeding $100M and thousands of wallets believed compromised; Reuters also reported analysts’ assessment of >$100M stolen.
September 12, 2023: Atomic published its longer-form “June 3rd Event Statement,” describing immediate response steps and external outreach during the investigation.
Following Days
Atomic did not publish a comprehensive technical postmortem comparable to the level of detail sometimes seen from open-source projects. That absence became part of the controversy.
The lack of a definitive root-cause disclosure created space for competing narratives.
Because Atomic Wallet is not fully open-source, independent code-level verification of its internal architecture is limited. That complicates external forensic certainty.
Let’s separate the landscape into two categories.
Blockchain analytics firms traced portions of the stolen funds through laundering routes consistent with prior North Korean-linked operations, including flows through mixers such as Sinbad. The U.S. Treasury later sanctioned Sinbad for facilitating laundering linked to Lazarus Group activity in late 2023, adding geopolitical context to laundering patterns more broadly.
Attribution in crypto incidents is typically based on transaction clustering, timing patterns, and laundering infrastructure similarity — not on public confessions. While some security researchers associated the flow patterns with Lazarus-linked tactics, definitive public attribution tying Atomic’s incident to a specific actor has not been confirmed by a final court ruling.
The most debated theory is a possible supply-chain or update mechanism compromise, meaning malicious code could have been injected into the distributed application build rather than individual users being phished.
Some independent security write-ups raised this as a plausible category of risk, particularly because Atomic Wallet uses Electron for its desktop application. Electron apps bundle web technologies with native code, and supply-chain risks in such ecosystems have been discussed widely in the broader security community.
However, Atomic did not publicly confirm a supply-chain breach. No formal independent forensic report has been released that conclusively identifies the attack vector.
That ambiguity is the core issue.
When the root cause is not publicly documented, users are left evaluating probability rather than certainty.
Several months before the breach, cybersecurity firm Least Authority had published an audit discussing various implementation and best-practice concerns in Atomic Wallet’s architecture. Among those discussions were broader points about cryptographic handling, documentation clarity, and Electron-related considerations.
It is important to be precise here: audits often list improvement areas. They do not automatically predict exploits. Least Authority did not publicly state that a hack was imminent. However, after the breach, portions of the audit were revisited and interpreted in hindsight as potential warning signals.
This became a credibility lever for critics. When a prior audit highlights areas needing improvement, and a breach later occurs without a transparent root cause disclosure, users draw connections.
Whether those connections are technically causal remains unproven publicly.
But perception influences trust.
In crypto, attribution is probabilistic. Analysts examine transaction patterns, laundering routes, and mixer usage.
Following the Atomic incident, on-chain tracking showed funds moving through mixing services and cross-chain bridges before consolidation. Some analysts observed patterns similar to those previously associated with the Lazarus Group, a North Korean-linked threat actor known for targeting crypto infrastructure.
Later in 2023, the U.S. Treasury sanctioned the Sinbad mixer for facilitating laundering tied to Lazarus-linked hacks. While this sanction did not exclusively reference Atomic, it strengthened the broader context of how stolen funds from multiple incidents were being processed.
What matters here is discipline in language.
There is no final judicial determination publicly concluding that Lazarus definitively executed the Atomic Wallet breach. There is pattern similarity and investigative reporting suggesting links. Those are different levels of certainty.
In security reporting, overstatement damages credibility. It is accurate to say that analysts traced flows through laundering infrastructure consistent with North Korean-linked tactics. It is not accurate to present that as a legally adjudicated fact.
After the breach, a class action lawsuit was filed in the United States alleging security failures and negligence.
Court records from the District of Colorado reflect that the complaint challenged Atomic’s security posture and representations. In 2024, the case was dismissed on jurisdictional grounds, with the court determining that the foreign-based entity did not have sufficient ties for U.S. jurisdiction under the claims presented.
A dismissal does not equal exoneration on technical grounds. It means the case did not proceed in that jurisdiction under that filing structure.
For affected users, that distinction matters. It does not retroactively recover funds, nor does it produce a judicial finding on root cause.
Atomic stated that it enhanced monitoring systems, improved security practices, and cooperated with law enforcement following the incident. Updates were rolled out in subsequent application versions.
However, because Atomic Wallet is not fully open-source and has not published a comprehensive independent forensic report, certain elements remain unverifiable from outside the company.
Users cannot independently audit:
That opacity is not unusual for closed-source wallets. But in a post-breach environment, transparency becomes a trust variable.
As of 2026, Atomic Wallet continues to operate, and there has been no repeat incident of comparable scale publicly reported. That stability is relevant. So is the unresolved root-cause ambiguity.
 Transparency Debate Around Atomic Wallet Code
Transparency Debate Around Atomic Wallet CodeIn crypto, especially, users do not just ask whether a wallet works; they ask whether it can be independently verified.
Atomic Wallet sits in an uncomfortable middle ground here. It is not fully closed in the sense of zero public code. It is also not fully open in the way many security-conscious users expect.
That nuance matters.
Atomic Wallet has historically positioned itself as “partially open-source.” What that means in practice is that some components and libraries used by the wallet are publicly viewable, while the full core application, including critical implementation details, is not completely open for independent audit.
In simple terms:
This distinction is often misunderstood. Using open-source cryptographic libraries does not automatically make a wallet open-source. The integration layer, how keys are handled, how updates are delivered, and how encryption is implemented in context, is just as important as the underlying primitives.
For a non-custodial wallet, the trust question becomes sharper after an incident. If the full codebase is not independently auditable, users must rely on vendor statements rather than third-party verification when something goes wrong.
That does not automatically imply insecurity. Many reputable wallets operate with partially closed components. But it shifts the burden of proof.
And that shift becomes visible when we look at how trust functions post-breach.
When a wallet is fully open-source, independent researchers can:
In a partially closed model, those steps become limited or impossible externally. After the 2023 incident, this dynamic became central. Because the full internal codebase was not publicly reviewable, independent researchers could not conclusively validate remediation measures.
This increases what can be called “trust load.” Instead of verifying, users must believe.
That trust load manifests in three ways:
Tie this back to the earlier Least Authority discussion. Audits that identify potential improvement areas become more sensitive in hindsight if subsequent events occur and users cannot independently confirm architectural corrections.
In crypto, transparency is not just a technical feature. It is a credibility amplifier.
That brings us to a more structured way of evaluating transparency.
Instead of debating labels like “open” or “closed,” it helps to evaluate concrete transparency markers.
Below is a practical checklist reflecting what security-conscious users typically look for in 2026:
| Transparency Signal | Status (Publicly Clear?) |
| Public security audits | Partial; historical audits exist, not continuous disclosure |
| Detailed public postmortem (2023 hack) | No full independent technical report publicly released |
| Fully open-source core code | No; partially open components |
| Reproducible builds | Not clearly disclosed |
| Public bug bounty program | Not prominently disclosed at scale |
| Clear, versioned security changelog | Not fully detailed publicly |
Where information is not explicitly published, the most accurate phrasing is “not clearly disclosed,” rather than assuming absence.
This scorecard does not render a verdict. It frames risk exposure. Fully open-source wallets distribute trust across the community. Closed or partially closed wallets centralize it with the vendor.
For some users, that trade-off is acceptable if usability and convenience outweigh auditability concerns. For others, particularly those holding significant capital, the inability to independently verify post-incident architecture changes becomes a deciding factor.
In the end, the open-source question is not ideological. It is about how much trust you are comfortable with outsourcing.
 Post Hack Reputation And Support Signals
Post Hack Reputation And Support SignalsSecurity architecture tells you how a wallet is designed. Customer support tells you how it behaves when something goes wrong.
For a non-custodial wallet, this distinction is critical. Support teams cannot reverse transactions or freeze stolen funds. What they can do is guide, clarify, and communicate. The quality and speed of that communication often shape user perception more than the underlying technology.
Let’s look at the operational side of Atomic Wallet.
Atomic Wallet provides support primarily through:
There is no 24/7 phone line. There is no guaranteed Service Level Agreement publicly disclosed for response times. Live chat functionality has historically been limited or event-dependent rather than enterprise-grade continuous support.
That structure is typical for many self-custodial wallets. The difference lies in expectations.
What should users realistically expect?
During normal operating periods, support responses typically come via email within a reasonable timeframe, depending on ticket volume. During high-traffic periods, especially after incidents, delays have been widely reported.
And this is where user psychology matters.
When funds are stuck in a pending swap or a transaction fails, users expect exchange-style intervention. But Atomic, as a non-custodial wallet, does not control blockchain confirmation. If a transaction is broadcast and confirmed on-chain, support cannot reverse it.
In short:
This gap between expectation and capability often fuels negative reviews.
The 2023 breach amplified this perception. During that period, affected users reported difficulty obtaining individualized remediation, which compounded frustration. Whether or not support performance was technically inadequate, the absence of transactional recourse created reputational pressure.
In non-custodial models, support is informational, not corrective. That difference is often underappreciated until something breaks.
Public reviews across app stores and crypto discussion forums fluctuate quickly. Sentiment shifts after major updates or incidents. The snapshot below reflects recurring themes observed up to early 2026.
Reviews change fast. Always verify current ratings before making decisions.
These themes center around usability rather than advanced DeFi tooling.
It is important to contextualize complaint volume. Crypto users are more likely to post reviews when something goes wrong than when everything works. Negative skew is common across wallet categories.
That said, trust erosion after a security incident tends to persist longer in public sentiment than in raw user counts.
As of early 2026, Atomic Wallet continues operating without a repeat breach of a similar scale publicly reported. Ratings remain mixed rather than catastrophic. That suggests reputational impact was significant but not terminal.
Customer support quality rarely defines a wallet in isolation. But after a breach, it becomes a multiplier.
A wallet that cannot reverse transactions must compensate with clarity, speed, and transparency. Where communication feels thin, trust load increases. Where documentation is clear and expectations are set early, user friction drops.
Reputation signals do not give binary answers. They provide directional context
 How Atomic Wallet Compares To Rivals
How Atomic Wallet Compares To RivalsNo wallet exists in isolation. The right question is not “Is Atomic good?” but “Compared to what — and for whom?”
Atomic sits in the convenience-first, multi-asset desktop/mobile category. It competes less with hardware wallets directly and more with software wallets like MetaMask, Trust Wallet, and Exodus.
To make this concrete, here is a structured comparison across the criteria that actually matter in 2026: transparency, hardware integration, DeFi depth, and post-incident trust signals.
| Wallet | Best For | Platforms | Open-Source Status | Hardware Support | Web3 / DApp Depth | Staking | Post-Incident Trust Notes |
| Atomic Wallet | Multi-asset desktop + staking convenience | Windows, macOS, Linux, iOS, Android | Partially open-source | No native hardware integration | Limited; no deep extension-based DeFi layer | Built-in staking for select assets | 2023 breach; no full public technical postmortem |
| MetaMask | Active DeFi users | Browser extension, iOS, Android | Core components open-source | Yes (Ledger, Trezor) | Deep DeFi integration; industry standard | Limited native staking; ecosystem-based | No comparable wallet-level mass compromise |
| Trust Wallet | Mobile-first multi-chain users | iOS, Android | Largely closed-source client; some components open | Limited hardware pairing | Strong mobile Web3 browser | Built-in staking for supported chains | No major global breach event comparable to Atomic |
| Exodus | Desktop UX + hardware pairing | Windows, macOS, Linux, iOS, Android | Partially open-source | Native Trezor integration | Moderate; less DeFi-native than MetaMask | Built-in staking | No wallet-wide breach event of Atomic scale |
| Ledger (with Ledger Live) | Maximum cold storage security | Desktop + hardware device | Firmware closed; apps partially open | Hardware-first | Limited direct DeFi without third-party connection | Limited staking via Ledger Live | Hardware model isolates keys offline |
This table highlights a pattern.
Atomic competes on ease of use and multi-asset convenience. It does not compete on hardware security depth. It does not compete on extension-native DeFi tooling. And after 2023, it competes under a heavier trust load than its peers without comparable incidents.
That does not eliminate it from consideration. It defines its lane.
Rather than framing this as a winner-versus-loser debate, it helps to match wallet design to user behavior.
Best for Mobile DeFi: MetaMask or Trust Wallet. Both provide integrated Web3 browser or extension-level connectivity that Atomic does not deeply replicate.
Best for Desktop UX + Hardware Pairing: Exodus, combined with Trezor, offers a smoother desktop experience while enabling cold storage signing.
Best for Maximum Security: Hardware-first approach. Ledger or Trezor used with a reputable software interface. Keys remain offline. Software wallet convenience is secondary.
Best for Multi-Asset Desktop Simplicity Without Hardware: This is where Atomic still fits. If the goal is to hold multiple assets, stake supported coins, and avoid complex DeFi routing, Atomic provides convenience.
For a snapshot of leading networks and their staking rewards, read the Best Coins to Stake Now overview.
The key distinction is this:
Atomic is a convenience wallet with staking features.
MetaMask is a DeFi gateway.
Exodus is a polished desktop wallet with hardware synergy.
Ledger and Trezor are security devices first.
Choosing between them depends on what risk you are optimizing for: usability friction or attack surface reduction.
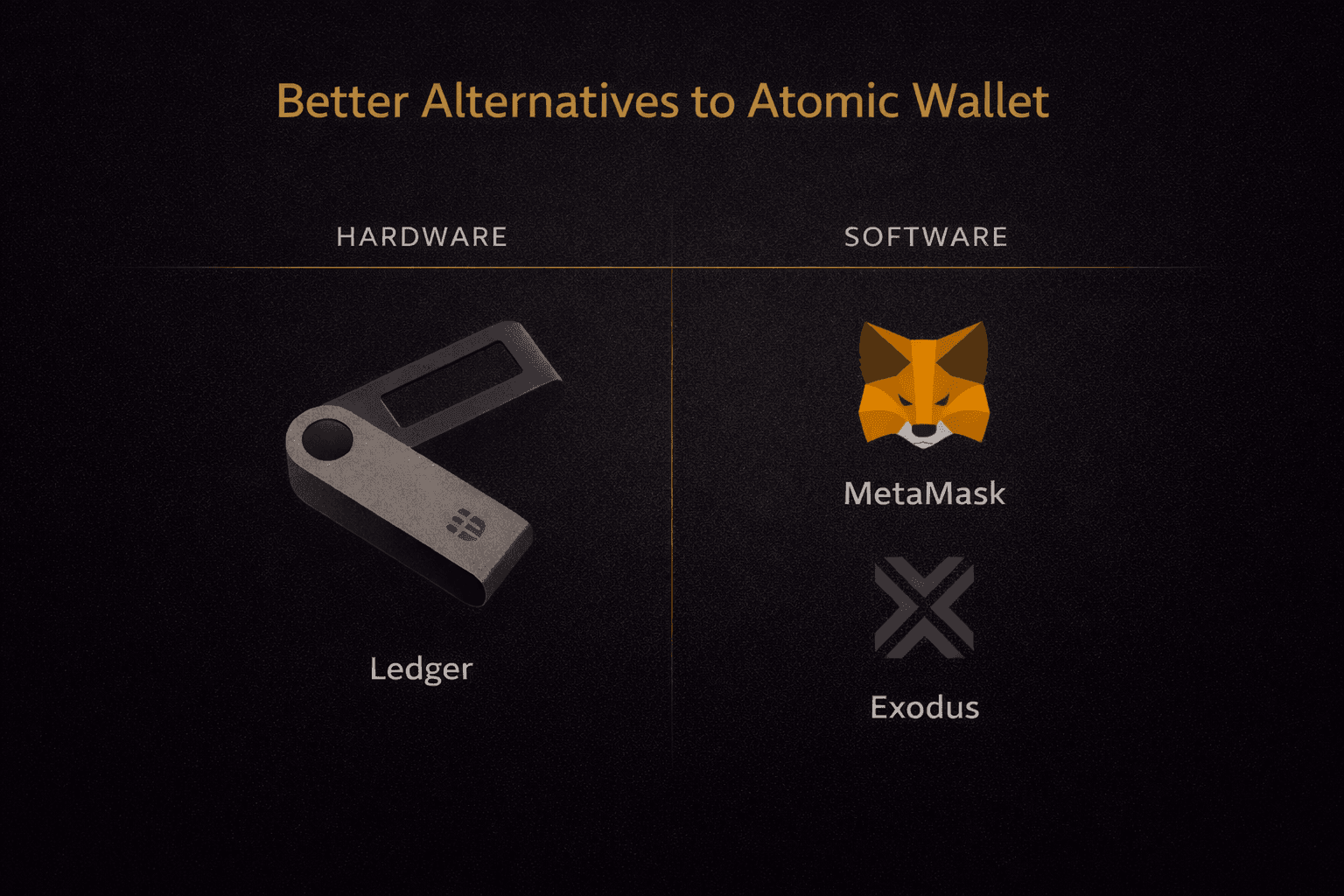 Stronger Wallet Options After Atomic Hack
Stronger Wallet Options After Atomic HackAfter a security incident, comparison stops being theoretical. It becomes personal. Users are no longer asking, “What features does this wallet have?” They are asking, “Where should my keys live?”
The answer depends on what you prioritize: maximum isolation, open verification, or everyday convenience.
Let’s separate the options clearly.
If your primary concern is minimizing remote attack surface, hardware wallets still sit at the top of the hierarchy.
Devices like the Ledger Nano line and the Trezor line are built around a simple principle: private keys never leave the hardware device. Transactions are signed inside a secure element (Ledger) or secure microcontroller environment (Trezor), and only the signed transaction, not the key, is broadcast to the network.
Why does hardware win in pure security terms?
Because your keys never reside on an internet-connected operating system. Malware can compromise a laptop. It cannot extract keys from a properly configured hardware device without physical access and PIN protection.
That isolation changes the threat model dramatically.
Instead of defending against:
Keyloggers
Clipboard hijacking
Remote malware
You primarily defend against:
Physical theft
Seed phrase exposure
Supply-chain tampering
Hardware wallets are not invincible. They still depend on a correct setup and safe seed storage. But the attack surface shrinks materially compared to hot wallets installed on general-purpose computers.
If you are holding high-five-figure or six-figure crypto allocations in 2026, hardware-first is still the default recommendation across the industry. Convenience decreases slightly, but on the other hand, risk reduction increases meaningfully. That is the trade.
Not everyone wants to manage a hardware device. For active DeFi users or smaller balances, software wallets remain practical.
In that category, two names dominate:
MetaMask and Trust Wallet.
MetaMask’s advantage lies in ecosystem integration. It functions as a browser extension and mobile wallet with deep Web3 compatibility. It is widely integrated into DeFi platforms, NFT marketplaces, and Layer 2 ecosystems. Core components are open-source, which allows independent researchers to inspect and review much of their logic.
Trust Wallet leans mobile-first and supports a broad range of assets with built-in Web3 browsing. It is more closed in its client architecture but benefits from scale and Binance's backing.
The tradeoffs here are different:
MetaMask has faced telemetry scrutiny in the past, particularly around default RPC routing through Infura, though configurations can be customized.
Trust Wallet prioritizes mobile convenience over extension-based desktop DeFi depth.
Neither wallet is perfect. But neither has faced a wallet-wide breach event comparable to Atomic’s 2023 incident.
For users who want open-source leaning code visibility and strong DeFi connectivity, MetaMask remains the reference standard in 2026.
For users who prioritize mobile asset management and integrated browsing, Trust Wallet offers a smoother UX.
Both remain hot wallets. The keys live on your device. Risk profile is lower than centralized exchanges, but higher than hardware.
It would be intellectually lazy to frame Atomic as unusable post-incident. That is not accurate.
Atomic still makes sense in specific contexts, provided expectations are calibrated.
It can be a reasonable choice if:
You are holding smaller balances where catastrophic loss would not be life-altering.
You value built-in staking convenience across multiple assets without managing external validators manually.
You need multi-platform access across desktop and mobile with a consistent interface.
You accept the transparency tradeoff of a partially open-source architecture.
This is not a “vault wallet” positioning. It is a convenient wallet positioning.
If you treat it as a hot wallet for moderate holdings rather than a cold-storage solution for long-term treasury-level assets, the risk profile becomes more proportionate.
The mistake is not using Atomic. The mistake is using it for a purpose it was never optimized for.
 When Atomic Wallet Makes Practical Sense
When Atomic Wallet Makes Practical SenseBy this point, the picture should be clear: Atomic Wallet is neither a scam nor a fortress. It is a convenience-first hot wallet operating under heavier trust scrutiny after 2023.
So the real question is not “Is it safe?” The real question is whether it matches your risk profile.
Instead of a vague yes-or-no answer, here is a practical decision framework.
Start with the most important variable: exposure.
1. How much are you storing?
High value demands isolation. Convenience is not a substitute for cold storage.
2. Do you use DeFi daily?
Atomic does not function as a deep DeFi gateway. If you farm, bridge, and sign contracts daily, you will outgrow it quickly.
3. Do you require open-source transparency?
After 2023, this question matters more. If auditability is a non-negotiable value, Atomic’s architecture may not align with you.
4. Do you already own a hardware wallet?
The cleanest setup in 2026 remains hybrid:
Hardware for storage.
Software wallet for limited interaction.
Atomic can play the interaction role. It should not be the vault.
If you decide that Atomic fits your use case, risk management becomes your responsibility. A few structural rules dramatically reduce exposure.
First, treat it as a spending wallet. Do not park long-term treasury-level assets in a hot environment. Keep only what you actively use.
Second, maintain strict device hygiene:
Third, verify downloads carefully. Always install directly from the official website. Avoid search-engine ads, impersonation domains, or “support” links shared via social media.
Fourth, never click wallet support links sent via direct messages. Legitimate support will not initiate contact asking for your seed phrase. Any request for recovery words is an attempt to drain your wallet.
Fifth, consider using a separate device profile or even a dedicated machine for crypto activity. Segmentation reduces cross-contamination risk.
The biggest threat to hot wallets in 2026 is not cryptographic weakness. It is endpoint compromise and social engineering.
If you operate with that in mind, Atomic becomes a calculated risk rather than a blind one.
Atomic Wallet still serves a segment of users who want multi-asset simplicity and built-in staking without hardware friction.
It does not serve users who:
Your decision should be driven by exposure size, workflow, and tolerance for trust load, not by marketing or fear alone.
Installing and setting up a non-custodial wallet is not a casual task. This is the moment where you either establish a secure foundation or introduce long-term risk. Atomic Wallet’s official guidance covers the mechanical steps, but the difference between safe and sloppy execution comes down to how seriously you treat the process.
Think of this section as operational discipline, not onboarding fluff.
Before you even create a wallet, the biggest risk is downloading the wrong software. Phishing campaigns targeting wallet users remain one of the most common attack vectors in 2026, and impersonation sites frequently appear above legitimate results through sponsored search ads.
Atomic Wallet’s official website is: https://atomicwallet.io
Once the application is installed from a verified source, proceed with wallet creation. Atomic generates a 12-word recovery phrase locally on your device. That phrase is the master key. Whoever controls it controls the funds.
The seed phrase must never exist digitally outside the wallet interface during setup.
Screenshots are especially risky because many devices automatically sync media to cloud services. A compromised cloud account can become a compromised wallet.
After recording the phrase, Atomic typically asks you to re-enter selected words. Do this slowly and deliberately. A single incorrect word can make recovery impossible. Then set a local password. This password encrypts wallet access on that specific device, but it does not replace the recovery phrase. If you forget the password yet still have the seed phrase, you can restore the wallet. If you lose the seed phrase, no password will save you.
Most users skip this step. That is a mistake. Before storing meaningful funds, perform a controlled restore test so you are not learning recovery during a crisis.
This process confirms three things:
Restoration failures are usually transcription errors, not wallet malfunction. Catching that early costs minutes. Discovering it after losing device access can cost everything.
Atomic Wallet, like any non-custodial wallet, does not hold your funds. The blockchain does. The wallet simply holds the keys. That distinction becomes real during setup and recovery.
The difference between a secure user and a compromised one is rarely technical knowledge. It is procedural consistency.
After reviewing architecture, the 2023 breach, transparency limits, support patterns, and competitive positioning, the conclusion is structural. Atomic Wallet is neither irredeemable nor top-tier. It occupies a middle ground that demands conscious risk calibration from the user.
The question is not whether it works. It does. The question is whether it is aligned with the level of capital and security assurance you require.
Atomic Wallet is not recommended for serious, long-term holdings, particularly if you are storing amounts that would materially impact your financial position if lost. The 2023 breach, combined with partial open-source transparency and the absence of a comprehensive public technical postmortem, means it carries a higher trust load than some competitors. That said, it remains acceptable as a convenience hot wallet for small to moderate balances, especially if you value multi-asset support and built-in staking across desktop and mobile.
For meaningful capital or long-term storage, a hardware wallet should be the default choice, ideally paired with a reputable software interface for transaction signing and DeFi access. In practical terms, Atomic can function as a utility wallet; it should not be your vault.
Get exclusive access to premium content, member-only tools, and the inside track on everything crypto.