MetaMask hardly needs an introduction. It is one of the wallets most people run into early, especially on Ethereum. But familiarity should not be confused with safety. Users still need to ask whether it is legitimate, whether it is secure enough, and whether it is still a sensible non-custodial wallet for Web3.
For most users, the answer is yes. MetaMask is a self-custody wallet made by ConsenSys, and it remains one of the main ways people access Ethereum-based DApps, tokens, NFTs, and other on-chain services through its browser extension and mobile app. But it is also a hot wallet, so ease of use comes with risk. In most cases, the danger is not MetaMask suddenly failing or turning out to be fake. It is users getting caught by phishing sites, fake downloads, malicious DApps, risky token approvals, wallet drainers, or infected devices.
That is an important difference. A lot of people still think their crypto sits inside the wallet app itself. It does not. MetaMask is really a tool for managing your keys, signing transactions, and connecting to Web3. Used properly, it can be a safe and legitimate way into Ethereum and other EVM networks. Used carelessly, it can also put you right in the middle of crypto’s scam-ridden side.
Editor's Note (March 27, 2026): We fully updated this article in March 2026 with the latest MetaMask security context, including phishing threats, fake app risks, malicious approvals, wallet drainer scams, hardware wallet integration, and MetaMask’s role across Ethereum and EVM-based Web3. We also restructured the piece to more directly answer whether MetaMask is safe, whether it is legit, and which users should treat it as an access wallet rather than a long-term storage solution.
Quick Verdict
MetaMask is a legitimate wallet, and it is generally safe for its intended purpose. But because it is a non-custodial hot wallet, the biggest risks usually come from user-side mistakes, scams, and unsafe approvals rather than from the wallet software itself.
MetaMask Safety Verdict
Who MetaMask Is Best For
MetaMask is best for beginners exploring Web3, active DeFi users, NFT traders, and people who mainly use EVM networks such as Ethereum, Arbitrum, Optimism, Base, and BNB Chain.
It is less ideal for long-term storage of meaningful balances unless it is paired with a hardware wallet, because a hot wallet is built for convenience and interaction, not maximum isolation.
MetaMask is a good fit for:
- Beginners who want a simple gateway into Web3 and EVM apps.
- Users who actively swap, bridge, stake, trade NFTs, or use DeFi protocols.
- People who want direct control over their keys while staying highly connected to the Ethereum ecosystem.
MetaMask is usually a poor fit for:
- Anyone storing large balances long term without a hardware wallet.
- Users who are not comfortable identifying phishing sites, fake apps, and suspicious signature requests.
- People who want maximum cold-storage style security without extra setup.
Disclosure and Methodology
Some links in this MetaMask safety guide may be affiliate links. If you choose to use a service through these links, we may earn a commission at no additional cost to you. That does not change how we assess MetaMask’s security model, hot wallet trade-offs, phishing exposure, approval risks, hardware wallet compatibility, or overall suitability for beginners and active Web3 users.
For this article, we evaluated MetaMask as a non-custodial hot wallet built for Ethereum and EVM-based Web3 activity rather than as a cold-storage solution. We focused on how MetaMask handles private-key control, transaction approvals, wallet security features, browser and mobile usage, scam exposure, and hardware wallet integration in real-world use. We also considered where MetaMask remains one of the strongest choices, where its limits become clearer, and which types of users should treat it as an access wallet rather than a long-term vault.
What Is MetaMask?
MetaMask is a non-custodial wallet that lets users manage private keys, approve blockchain actions, and interact with Ethereum and other EVM-compatible networks. The wallet does not hold coins “inside the app” the way a bank app holds money in an account. Your assets stay on-chain, while MetaMask gives you the interface needed to control addresses, sign transactions, manage tokens and NFTs, and connect to dApps.
MetaMask’s own onboarding material describes it as a wallet client that helps users manage private keys and interact with decentralized applications, while keeping no copy of your email, password, or Secret Recovery Phrase on MetaMask’s side. That is the core definition readers need to understand before anything else.
Nothing matters more than the seed phras. If that phrase falls into the wrong hands, the wallet can usually be taken over. That is what makes self-custody both appealing and brutal. You are in charge, but there is no safety net.
Our full MetaMask review covers all that and much more.
For readers focused specifically on Ethereum wallet choices, our guide to the best Ethereum wallets shows how MetaMask compares with other Ethereum-first options.
Browser Extension vs Mobile App
MetaMask is available both as a browser extension and as a mobile app, and that is more than just a difference in format. On desktop, the extension is what allows it to work directly with DApps inside the browser. That is a big reason MetaMask became such a common way to use Web3 in the first place.
That convenience also creates risk. A browser extension sits closer to browser-based phishing, fake connection prompts, and conflicts with other wallet tools or suspicious add-ons. On desktop, that matters more than many beginners realize.
The mobile app’s built-in browser removes some desktop friction and can reduce dependence on a cluttered browser extension environment, but it does not remove phishing or approval risk. A bad link is still a bad link, and a malicious signature is still dangerous whether it appears on a laptop or a phone.
Neither version is a cold wallet. Both are hot-wallet interfaces meant for active use.
Is MetaMask Safe?
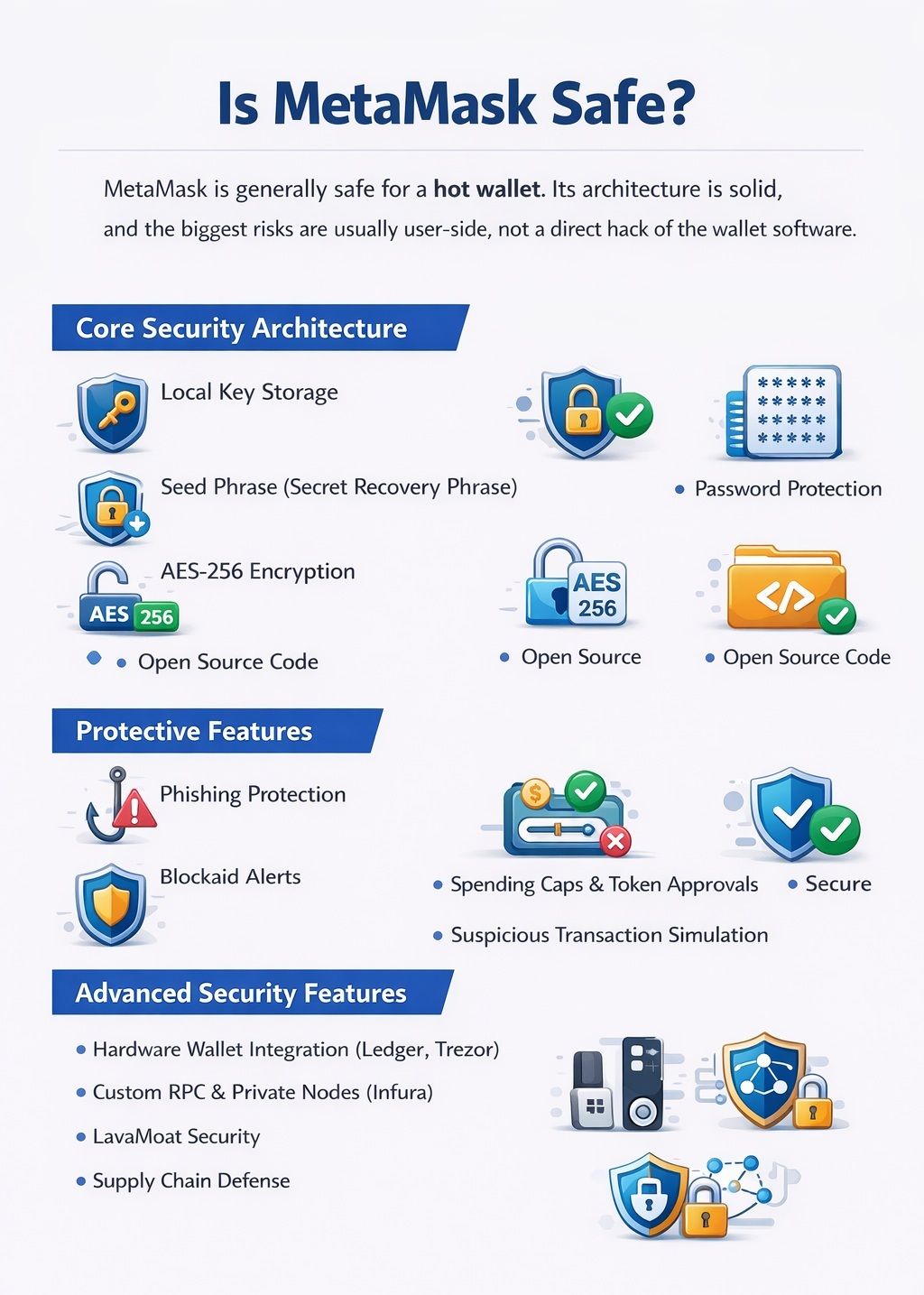
For a hot wallet, MetaMask is generally safe. Its basic architecture is credible, its code is transparent, and its security tooling has improved meaningfully over time. But the correct way to judge MetaMask is not to ask whether it is perfectly safe. No hot wallet is. The better question is whether its design is solid and whether the main risks are understood.
In MetaMask’s case, the answer is mostly yes. The wallet itself has a mature security model for self-custody, but users are operating in an environment where scams, fake interfaces, malicious signatures, and approval abuse are common. That is why MetaMask can be both “safe for a hot wallet” and “still dangerous if used badly” without contradiction.
For a deeper dive on hot wallets, take a look at our guide on top hot wallets.
 Metamask is a Transparent, Credible Hot Wallet With Solid Security
Metamask is a Transparent, Credible Hot Wallet With Solid SecurityCore Security Architecture
At the core, MetaMask keeps private keys in local storage on the user’s device instead of in a company-controlled account database. That matters because the wallet is not a custodial service pretending to be self-custody. You are the one holding access, and recovery depends on your Secret Recovery Phrase rather than a password reset email from the company.
Local wallet access is protected by a password, recovery is tied to the recovery phrase, and the wallet’s local vault is encrypted, commonly described in MetaMask discussions as using AES-256 encryption for sensitive payload protection. The extension codebase is also publicly visible on the official MetaMask GitHub repository, which supports the claim that the wallet is open source in a meaningful sense. Transparency is not the same thing as perfection, but it is better than asking users to trust a completely closed black box.
This is also why MetaMask feels different from an exchange wallet. An exchange can often reset access because the exchange controls the account system. A non-custodial wallet cannot do that without defeating the whole point of self-custody.
Protective Features
MetaMask has added several meaningful safeguards to reduce common user mistakes. One of the most important is security alerts built with Blockaid, which are enabled by default on supported transactions in Extension and Mobile. These alerts are designed to flag suspicious activity before a user confirms it, helping with phishing protection, suspicious transaction alerts, and some kinds of malicious transaction analysis.
Another key area is token approvals. Many users focus on swaps, mints, or deposits while paying too little attention to permissions. MetaMask’s explainer on what a token approval is makes the point clearly: an approval is permission for a DApp or smart contract to move a token from your wallet. In the wrong context, that is much more dangerous than a one-time send.
MetaMask also supports custom spending caps for token approvals, which is one of the simplest practical improvements users can make. Instead of granting a contract unlimited access, a user can cap the amount. That will not fix every scam, but it can sharply reduce the damage from a single bad approval.
Users who are unsure how dangerous a signature request can be should also read our explainer on crypto blind signing, because many wallet losses begin with approvals that do not look obviously malicious.
Each action still requires user-side transaction confirmations, and MetaMask’s estimated balance changes feature adds a form of transaction simulation on supported Ethereum transactions so users can preview likely account changes before they submit. That is useful context, but it should be treated as a speed bump, not a guarantee. A clear warning can save users. It cannot replace attention.
Advanced Security Features
For larger balances, the biggest upgrade is still hardware wallet integration. MetaMask officially supports connecting Ledger and Trezor devices, which lets users keep MetaMask’s familiar interface while moving the actual signing authority to a hardware device. That setup matters because the wallet interface stays online, but the most sensitive key operations no longer live in a plain hot-wallet environment.
MetaMask gives more control here than many users realize. It supports manual RPC configuration, so people are not locked into the default setup if they want different node options, access to specific networks, or a bit more say over the infrastructure they are using. For many users, that infrastructure is Infura, which powers a lot of MetaMask’s default connections. That is convenient and usually fine, but privacy-conscious users may prefer a different RPC provider or even their own node where that is practical. It is not something every user needs to worry about, but it does matter for anyone thinking about metadata exposure, provider concentration, or relying too heavily on a single service.
MetaMask has also invested in supply chain security through LavaMoat, a named architectural security layer designed to reduce risk from malicious or compromised software dependencies. That is one of those details most beginners never look for, but it adds technical credibility because it shows MetaMask is hardening not only the wallet surface but also the software ecosystem underneath it.
Has MetaMask Ever Been Hacked?
No, MetaMask itself has never been asked.
It's important to note, however, that this question gets asked constantly, but it is often framed badly. When users say MetaMask was “hacked,” they usually do not mean a direct compromise of the wallet software in the way that phrase sounds. More often, they mean a loss that happened through phishing, a fake MetaMask app, malicious smart contracts, a compromised device, or a third-party exploit tied to a protocol they used.
That distinction matters because it changes the lesson. If the problem were mainly a direct wallet-software failure, the response would be “don’t use MetaMask.” In reality, the more common lesson is “understand the attack path.” A self-custody wallet can be legitimate and still be the place where losses are noticed, because the wallet is where the signature, approval, or drain finally shows up.
MetaMask’s own material on malicious token approvals makes this clearer. In many cases, the wallet is not “broken.” The user granted dangerous permissions to a bad contract, interacted with a malicious interface, or trusted a fake support or app flow.
Most so-called MetaMask hacks are really user-environment attacks, approval abuse, fake installs, malware, or downstream protocol failures.
The Real Risks of Using MetaMask
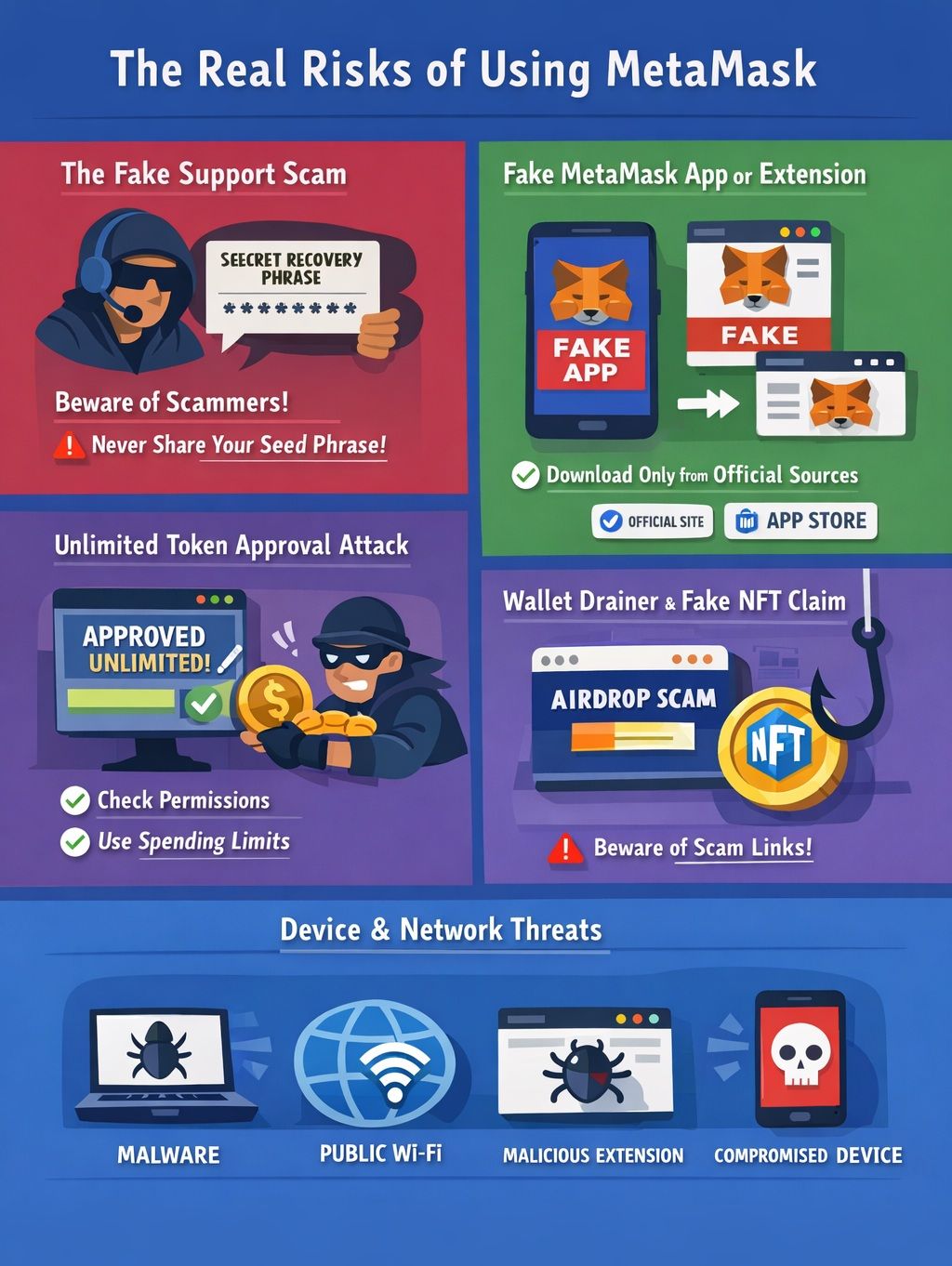
The best way to understand MetaMask risk is to stop thinking in slogans and start thinking in scenarios. Most losses happen through a handful of recurring patterns, and those patterns are much more useful than a vague idea that “crypto is risky.”
 Understand Metamask Risk by Identifying Recurring Loss Patterns Rather Than Slogans
Understand Metamask Risk by Identifying Recurring Loss Patterns Rather Than SlogansThe Fake Support Scam
The support scam is still one of the most common attacks because it is simple and often works. A scammer pretends to be a support rep, moderator, or recovery expert and then asks for your seed phrase or Secret Recovery Phrase. MetaMask is very clear on this point in its official support materials. It will never ask for that phrase, and users should rely on official support channels rather than unsolicited DMs.
This attack often works because it uses urgency. A user has a stuck transaction or a scary pop-up, posts publicly, and an impersonator arrives first. MetaMask’s guidance on spoofing scams is worth taking seriously here, because impersonation is not a side issue. It is one of the standard ways beginners lose wallets.
The Fake MetaMask App or Extension
The fake MetaMask app problem is a major beginner risk. Counterfeit downloads and cloned extensions are designed to catch users at the first possible moment, usually by stealing credentials during setup or import. MetaMask even has a dedicated guide on how to recognize the real MetaMask wallet because counterfeit extension and fake-install attacks are common enough to deserve their own defensive education.
The simple rule is to use the official website and properly moderated or verified app-store paths, not search ads, random blog posts, or private messages. A fake installation can compromise a wallet before the user even makes a first transaction.
The Unlimited Token Approval Attack
The unlimited approval problem is one of the most underappreciated MetaMask risks. Users often click through a token approval prompt without understanding that they may be giving a contract continuing power over their assets. If the contract or front-end turns out to be malicious, the result can be catastrophic.
MetaMask has a dedicated explanation of why some flows use unlimited approvals in MetaMask Swaps, and that page is useful precisely because it forces users to see approvals as permissions, not as harmless confirmations. With a malicious dApp, an unlimited approval can be enough to drain approved tokens later. This is why users should revoke approvals they no longer need and use spending caps whenever possible.
The Wallet Drainer or Fake NFT Claim
A classic wallet drainer attack often arrives disguised as a free reward. It may be a fake NFT claim, a “special mint,” a surprise token page, or an airdrop scam. The bait is designed to feel low-risk because the user is not “sending” funds. But a malicious signature can be just as dangerous as a transfer if it grants control or triggers a hidden action.
MetaMask’s warning about signature phishing is useful here because many drainers do not look like obvious theft. They look like routine Web3 interaction. That is why users should not connect a wallet to random claim pages, surprise mint links, or unverified airdrop sites.
Device, Browser, and Network Risks
Not every wallet compromise starts with a fake DApp. Sometimes the real problem is everything around the wallet. A device can already be compromised. Malware can be running in the background. A bad browser setup, an unpatched vulnerability, or a malicious extension can all turn a normal wallet session into a risky one.
MetaMask’s own note about extension conflicts and multiple browser wallets is a useful reminder that messy browser setups can create confusion fast. Add public Wi-Fi, clipboard hijacking, or weak device security habits, and the number of ways things can go wrong increases quickly.
For a broader look at the scams that keep showing up across the industry, see our guide to crypto scams to avoid in 2026.
How to Use MetaMask Safely
The good news is that safer MetaMask use does not require a full cybersecurity background. Most of it comes down to clean setup, slower signing habits, and separating storage from experimentation.
 Safer Metamask Use Requires Clean Setup, Slow Signing, and Separating Storage
Safer Metamask Use Requires Clean Setup, Slow Signing, and Separating StorageEssential Safety Setup
Start with basics that are easy to understand and hard to regret. Use a strong password, keep an offline seed phrase backup, enable auto-lock, use the official download path only, and stay current on app updates.
MetaMask’s new-wallet setup guide stresses the importance of creating the wallet carefully and backing up the Secret Recovery Phrase properly. Its auto-lock and secure locking guide is equally practical because an idle unlocked wallet is an unnecessary risk. Its update guidance also explains why official store installs matter: store-based versions receive automatic updates, security patches, and signature checks that reduce tampering risk.
These are not glamorous steps, but they prevent some of the most common avoidable losses.
Safer Transaction Habits
The next layer is not the wallet itself, but how it is used. Good habits go a long way here: double-checking URLs, reviewing token approvals carefully, avoiding random links, reading signature requests properly, and treating any unexpected prompt as a warning sign until it is clear what is happening.
MetaMask’s guide to checking whether a smart contract is safe to interact with is useful for exactly that reason. It encourages basic due diligence instead of blind trust. If you do not understand what you are being asked to sign, what a contract address is doing, or what an approval would allow, the safest move is not to assume it is fine. It is to stop and figure it out first.
Best Setup for Large Amounts
The safest answer for large holdings is simple: do not leave serious money in a plain hot wallet unless you are comfortable with hot-wallet risk. MetaMask is best thought of as an access layer for active use, not as your only vault.
For larger balances, the better setup is MetaMask plus a hardware wallet, ideally with wallet segmentation. In practice that means one vault wallet for long-term holdings, one active DeFi wallet for regular onchain use, and one experimental wallet for higher-risk mints, new dApps, and random testing.
This structure is boring, which is exactly why it works. If your experimental wallet gets hit, your vault is not part of the blast radius.
The Coin Bureau’s breakdown of hardware wallets vs software wallets is useful for readers who want a deeper explanation of why this separation matters.
Advanced Privacy and Control
Some users want more than basic safety. They want better privacy, tighter infrastructure control, or less default reliance on centralized service providers. That is where custom RPC settings and own node options become relevant.
For users who take privacy seriously, the setup can go further. That might mean choosing a different RPC provider, relying less on Infura, using a cleaner browser environment, and being more aware of tracking and metadata exposure. Those steps are not necessary for everyone, but they are valid upgrades for people who care about control.
MetaMask vs Other Wallets
| Wallet | Wallet Type | Best For | Security Profile | Main Trade-Off |
|---|---|---|---|---|
| MetaMask | Non-custodial browser wallet / mobile wallet | Ethereum and EVM-based Web3 access | Strong for a hot wallet | High scam exposure if used carelessly |
| Trust Wallet | Non-custodial mobile-first wallet | Broad multi-chain mobile use | Good general self-custody security | Less synonymous with deep desktop EVM workflows |
| Phantom | Non-custodial browser/mobile wallet | Solana-first users and cleaner consumer UX | Strong built-in scam detection | Less native to Ethereum-first culture |
| Coinbase Wallet | Non-custodial browser/mobile wallet | Mainstream self-custody onboarding | Familiar security framing and easy entry | Less favored by some power users |
| Ledger | Hardware wallet | Larger holdings and cold-storage security | Offline private-key protection | Less convenient for rapid daily dApp use |
When MetaMask Is the Better Choice
MetaMask is usually the better choice when your focus is Ethereum, the broader EVM ecosystem, strong dApp support, and broad Web3 access. That is still MetaMask’s home turf.
This is also where MetaMask’s network effect matters. Tutorials, wallet prompts, DeFi dashboards, NFT marketplaces, and Ethereum-native communities still tend to assume MetaMask first. For readers who want ecosystem context around that role, Coin Bureau’s pieces on the best DeFi wallets and the MetaMask beginner experience are worth reviewing.
When Another Wallet May Be Better
MetaMask is strong in its lane, but other wallets can make more sense when the user’s needs are different. Trust Wallet is often a better fit for mobile-first self-custody. Phantom is the natural choice for Solana users and has made scam detection an important part of the experience. Coinbase Wallet can feel more familiar for people coming from exchange-based crypto use and only beginning to move into self-custody. For bigger long-term holdings, Ledger is often the more sensible choice, while Trezor continues to appeal to users who want open security design and offline control over their keys.
Wallets like Exodus and Brave Wallet are part of the wider conversation too. Still, when the use case is Ethereum DApps, DeFi, and EVM-based Web3, MetaMask is usually the wallet people come back to first.
Readers can also read our piece on best crypto wallets for better understanding.
Is MetaMask Safe for Beginners?
Yes, MetaMask is easy enough for beginners to start with, and that is a big part of why so many people use it first. It is everywhere across Ethereum, there are plenty of tutorials for it, and most new users will run into it early anyway. That makes the first few steps into Web3 a lot less confusing.
The catch is that beginners are also the easiest to scam. They do not always know what a normal wallet prompt looks like yet. They may not spot a fake site, a bad approval request, or a download link that looks right but is not. Sometimes one fake support message or one cloned page is all it takes.
That is why MetaMask is better described as beginner-friendly than beginner-proof. It can be a good first wallet, but only if users stick to the official download source, double-check the sites they are using, ignore support DMs, and keep the recovery phrase offline and private. Simple habits like avoiding random social links and reading transaction prompts properly can remove a lot of the risk.
Where beginners should be more cautious is with storage. MetaMask is useful for learning, trying apps, and managing smaller amounts, but it is not the best place to keep serious money in a normal hot wallet setup. Once the amount starts to matter, using MetaMask with a hardware wallet makes far more sense.
Beginners who want a wider shortlist before choosing can compare MetaMask with other easy-entry options in our guide to the best beginner friendly crypto wallets.
Conclusion
MetaMask is real, widely used, and generally safe when people use it properly. The main risks are not about the wallet suddenly failing or turning out to be illegitimate. They are the same risks that show up across crypto all the time: phishing, fake apps, malicious approvals, compromised devices, and too much exposure in active Web3 environments.
For Ethereum and EVM-based activity, MetaMask is still one of the most practical wallets out there. It handles DeFi well, works across a huge range of DApps, and remains a common choice for NFT users too. But like any hot wallet, it is better for access than deep storage.
For larger amounts, a hardware wallet is the better answer. Used together, a hardware wallet and MetaMask give users the convenience of the interface without leaving the whole portfolio exposed to one bad interaction.





