What Is Coldcard?

Coldcard Focuses On Bitcoin-Only Security And Sovereign Self-Custody. Image via
ColdcardColdcard is a Bitcoin-only hardware wallet designed to store private keys offline and sign transactions securely. The device is produced by Coinkite, a Canadian company known for building security-focused Bitcoin infrastructure and tools.
Hardware wallets in general exist to isolate private keys from internet-connected devices. When users keep private keys on a phone or computer, malware can potentially access those keys and steal funds. Hardware wallets reduce that risk by storing keys in a dedicated device and allowing transactions to be signed without exposing sensitive data.
Before choosing a hardware device, compare the leading cold storage wallets designed for long-term crypto protection and understand the difference between private and public keys in crypto wallets.
Coldcard takes this concept further than many mainstream wallets. Instead of focusing on convenience or supporting dozens of cryptocurrencies, the device follows a strict Bitcoin-only philosophy. This design approach allows the wallet’s firmware to remain smaller and easier to audit while focusing entirely on Bitcoin’s transaction structure.
For some users, this is a limitation. Many investors hold multiple cryptocurrencies and want a single wallet that supports them all. For others, however, the Bitcoin-only model is a strength because it simplifies the codebase and reduces potential attack vectors.
Most current discussions of Coldcard focus on the Coldcard Mk4, which is the latest widely distributed version of the device. The Mk4 introduced improvements in secure chip architecture, transaction verification, and microSD workflows compared with earlier models.
Understanding what Coldcard does at a high level is helpful, but the real differentiation lies in how the device approaches self-custody security.
What Makes Coldcard Different?
Coldcard stands apart from many hardware wallets because it was designed from the beginning for advanced Bitcoin self-custody rather than mainstream consumer convenience.
One of the defining features is its support for air-gapped transactions. Instead of connecting the device directly to a computer through USB, users can move unsigned and signed transaction files using a microSD card. This keeps the signing process isolated from internet-connected devices.
Another important element is the device’s use of PSBT workflows, short for Partially Signed Bitcoin Transactions. PSBT allows transactions to be prepared on one machine and then signed securely on another device. Hardware wallets use this format to ensure private keys never leave the secure device.
Coldcard also supports microSD backups, allowing encrypted wallet backups to be stored separately from the device. This adds an additional recovery mechanism beyond the traditional seed phrase.
The device includes multiple defensive features as well, including anti-phishing protections, duress PINs, and other mechanisms designed to protect users if the device falls into the wrong hands.
Together, these features reflect a philosophy focused on sovereignty and operational security, rather than ease of use.
Coldcard’s Core Value Proposition
Coldcard’s core promise is simple: keep private keys offline while giving users full control over how transactions are signed and verified.
By minimizing the interaction between private keys and internet-connected systems, the wallet significantly reduces the attack surface available to malware or phishing attempts.
The device is also designed to support advanced self-custody practices. Users who run their own Bitcoin nodes, maintain multisignature wallets, or manage large long-term holdings often need tools that allow granular control over transaction signing.
Coldcard fits naturally into those workflows. It integrates well with desktop wallets such as Electrum and Sparrow Wallet, allowing users to build watch-only wallets that interact with the blockchain without exposing private keys.
For disciplined users who prioritize long-term Bitcoin storage, this model offers a level of security that many mainstream wallets struggle to match.
With a clear understanding of what Coldcard is and how it differs from typical hardware wallets, the next question becomes more practical: who should actually consider buying one?
Hardware wallets are not one-size-fits-all tools. The best choice often depends on how a person stores Bitcoin, their level of technical comfort, and the amount of responsibility they are willing to take for self-custody.
Coldcard is built for a specific category of user, and understanding that distinction helps avoid frustration later.
Who Should Buy Coldcard?
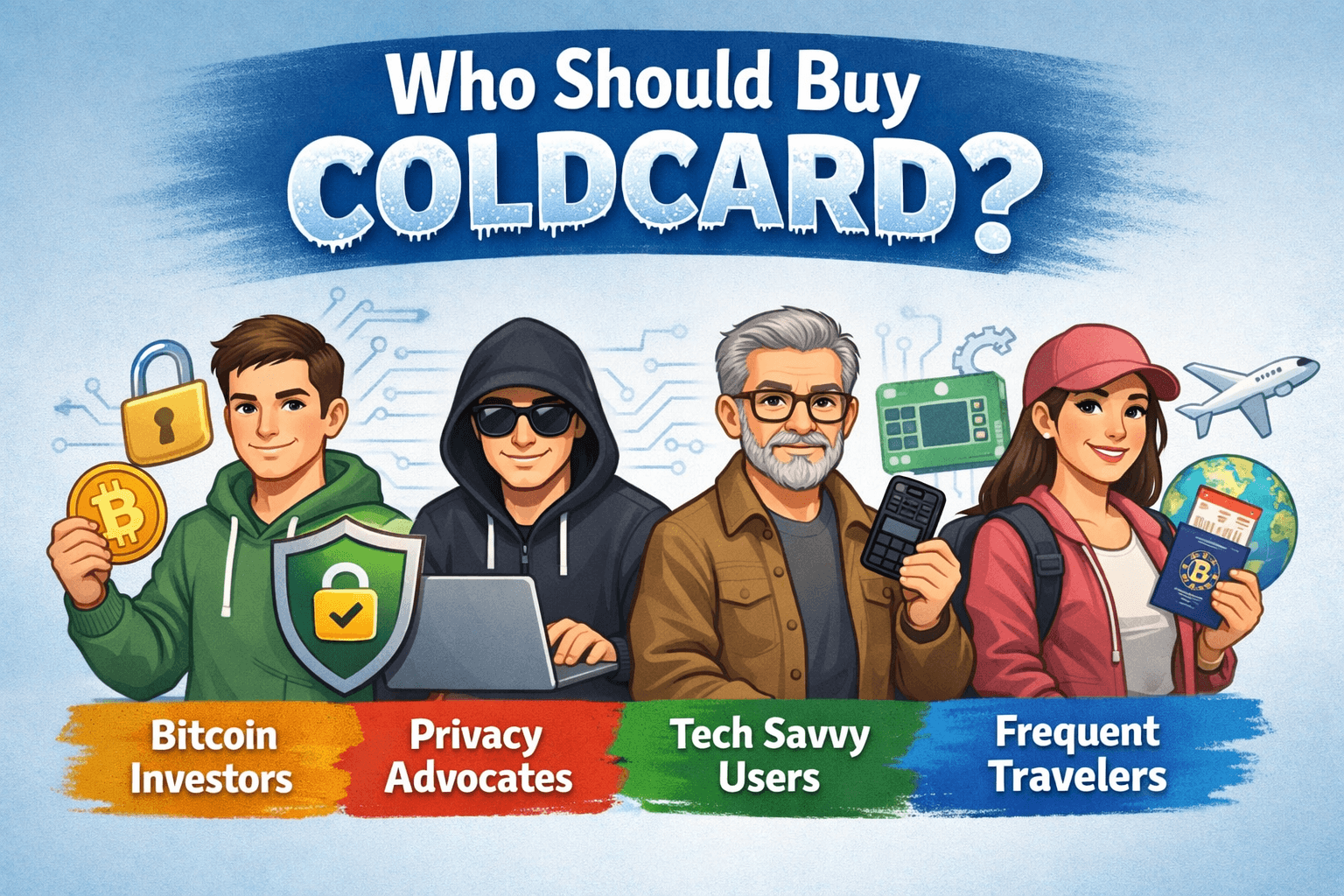
Understanding Which Bitcoin Users Benefit Most From Coldcard
Coldcard’s design philosophy prioritizes security and control. That makes it extremely powerful in the right hands, but unnecessarily complex for others.
This section breaks down the types of users who benefit most from Coldcard and those who may find a simpler hardware wallet more suitable.
Coldcard Is Best For
Coldcard is particularly well-suited for people who approach Bitcoin storage as a long-term security practice rather than a casual investment tool.
One of the most common user groups is Bitcoin maximalists. Because the device focuses exclusively on Bitcoin, it appeals to users who deliberately avoid altcoins and want a wallet optimized for Bitcoin’s transaction model.
Another strong fit is long-term holders protecting meaningful Bitcoin balances. Investors who plan to store BTC for years often prioritize reducing every possible attack vector. Coldcard’s air-gapped transaction model and PSBT workflows support this goal.
The device is also popular among privacy-focused users. Many Coldcard users pair the wallet with privacy-oriented desktop software or their own Bitcoin nodes to reduce reliance on third-party services.
Coldcard is also widely used in multisignature setups, where multiple hardware wallets must sign a transaction before funds can move. This approach is common for high-value storage, institutional custody, or collaborative treasury management.
Finally, Coldcard is a natural choice for technically comfortable users who already interact with tools like Sparrow Wallet, Electrum, or self-hosted Bitcoin nodes. These environments integrate well with Coldcard’s PSBT-based workflow.
For these users, Coldcard provides a level of flexibility and control that many consumer wallets cannot match.
Coldcard Is Not Ideal For
Despite its strengths, Coldcard is not the best choice for every cryptocurrency user.
Total beginners may struggle with the device’s setup process and transaction workflows. Coldcard assumes users understand concepts such as seed phrases, backups, and transaction verification. Without that foundation, the learning curve can feel steep.
The wallet is also less appealing to people who prefer mobile-first convenience. Many hardware wallets today integrate directly with smartphone apps, allowing users to send transactions quickly. Coldcard instead relies heavily on desktop wallet integrations.
Another limitation is the lack of support for altcoins. Users who hold Ethereum, tokens, NFTs, or other cryptocurrencies will need additional wallets to manage those assets.
Finally, Coldcard may not be ideal for people unwilling to learn secure operating practices. Hardware wallets do not eliminate responsibility. Users must still manage backups, passphrases, and recovery procedures correctly.
For those looking for the easiest possible hardware wallet experience, options like Ledger Nano X or Trezor Model T may be more approachable.
Decision Shortcut
For readers who want a quick answer, the decision often comes down to how seriously you approach Bitcoin self-custody.
Buy Coldcard if:
You hold Bitcoin primarily, want maximum control over private keys, and are comfortable learning advanced security workflows such as air-gapped signing and PSBT transactions.
Skip Coldcard if:
You prefer simple mobile apps, hold multiple cryptocurrencies, or want the easiest possible hardware wallet setup.
Coldcard rewards users who invest time in learning its security model. Those who prefer convenience over control may find other hardware wallets easier to live with.
Understanding who Coldcard is built for naturally leads to the next practical step: preparing for setup. Hardware wallets are security devices, so the process begins even before you power the device on.
Checking packaging, verifying authenticity, and gathering the right accessories are all part of safe onboarding. Skipping these steps can expose users to supply-chain risks or incomplete backups later.
What Comes In The Box And What You Need Before Setup
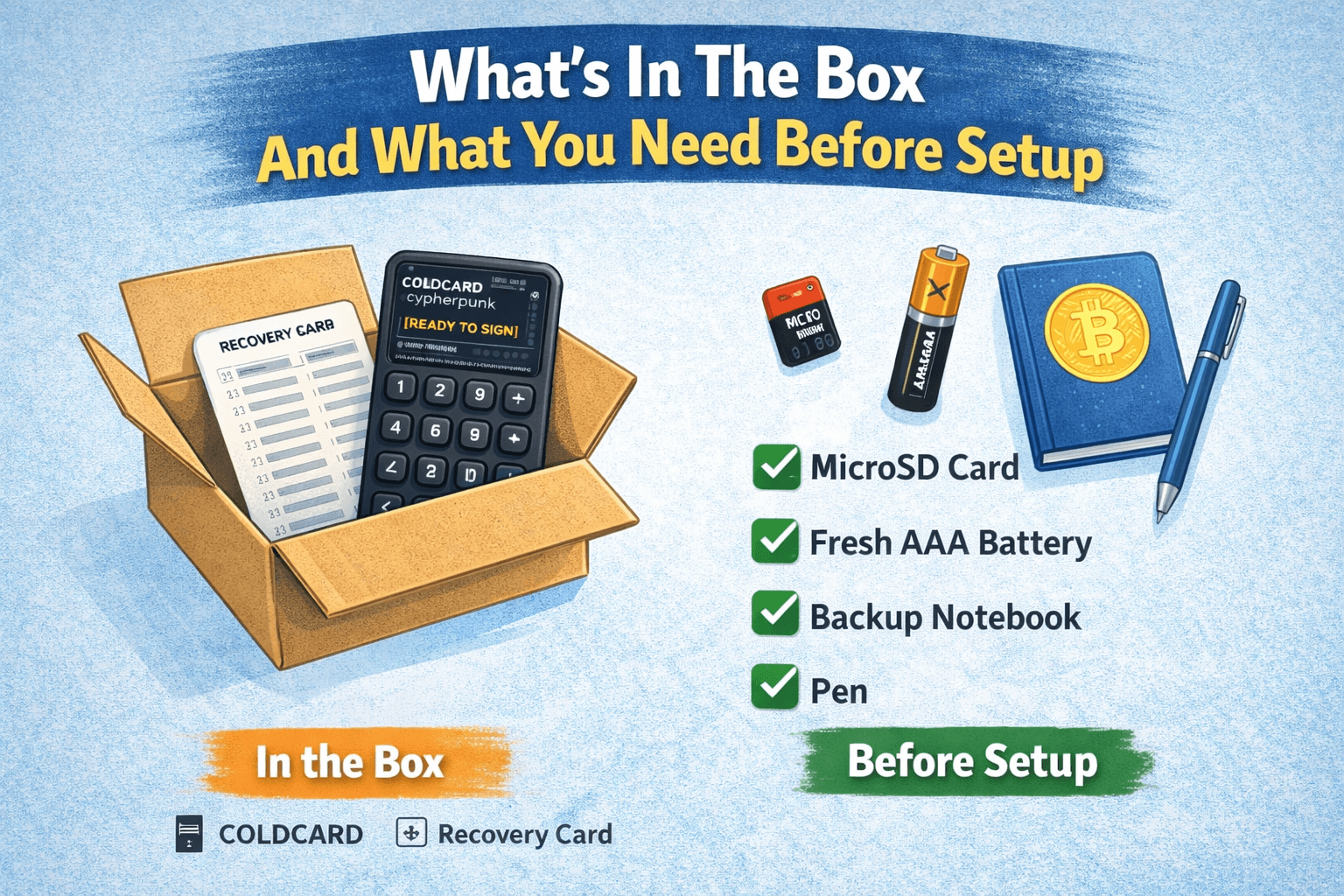
Essential Items And Preparation Required Before Setting Up Coldcard
Coldcard devices are intentionally minimalist. The company expects users to control their own operational security environment rather than relying on bundled accessories.
Before setting up the wallet, it helps to know exactly what comes with the device and what additional items you should prepare.
What’s Included
When purchasing a Coldcard device from Coinkite, the box includes the hardware wallet and basic documentation to guide the initial setup.
The core component is the Coldcard device, which includes a small screen, physical keypad, and microSD slot. These elements allow users to verify transaction details and interact with the wallet without relying on external software.
Most packages also include a tamper-evident bag. This protective packaging helps users detect whether the device may have been opened or manipulated during shipping. Verifying the integrity of this packaging is an important first step before powering on the wallet.
In addition to the device and packaging materials, users will usually receive basic setup instructions and a backup card intended for recording the wallet’s seed phrase.
Coldcard intentionally avoids shipping unnecessary accessories so that users can choose their own cables and storage solutions according to their security preferences.
What You Should Buy Separately
Although the device itself contains everything required to generate private keys, several additional items can make the setup process safer and more practical.
A microSD card is one of the most useful accessories. Coldcard uses microSD storage for encrypted backups and air-gapped transaction workflows. Having at least one reliable card available simplifies both setup and long-term wallet management.
Users should also prepare a power-only USB cable or a trusted cable. Some Coldcard workflows intentionally avoid data transfer over USB, so using a power-only cable can add an extra layer of isolation.
Another highly recommended accessory is a steel backup solution. Seed phrases written on paper can degrade over time or become vulnerable to fire and water damage. Steel backup plates provide a far more durable long-term storage method for recovery phrases.
For users planning advanced setups, a compatible desktop wallet such as Sparrow Wallet or Electrum may also be required. These applications allow watch-only wallets and PSBT workflows that interact with the Coldcard device.
Preparing these items ahead of time helps avoid interruptions during the setup process.
Check The Packaging Before You Use It
Hardware wallets depend heavily on supply-chain security. Before powering on the device, users should carefully inspect the packaging and confirm that it has not been tampered with.
Coldcard devices ship in tamper-evident bags designed to reveal whether the seal has been broken. If the bag appears damaged, resealed, or otherwise suspicious, it is best to pause setup and contact the seller.
Purchasing directly from official channels or authorized distributors significantly reduces supply-chain risks. Hardware wallets obtained from unknown third-party sellers or marketplaces may pose a higher risk of tampering.
If anything about the packaging or device appears unusual, it is safer to avoid using the wallet until its authenticity is confirmed.
Once packaging integrity is verified and the necessary accessories are ready, the next step is creating the wallet itself.
Coldcard Setup Guide: Step-By-Step For First-Time Users
Setting up a Coldcard wallet is straightforward once the security steps are understood. However, because the device prioritizes safety over convenience, the process includes several verification stages designed to protect private keys.
The following walkthrough outlines the typical setup flow for new users.
Step 1: Verify The Device And Packaging
Before turning on the wallet, confirm that the tamper-evident packaging is intact and that the device appears untouched.
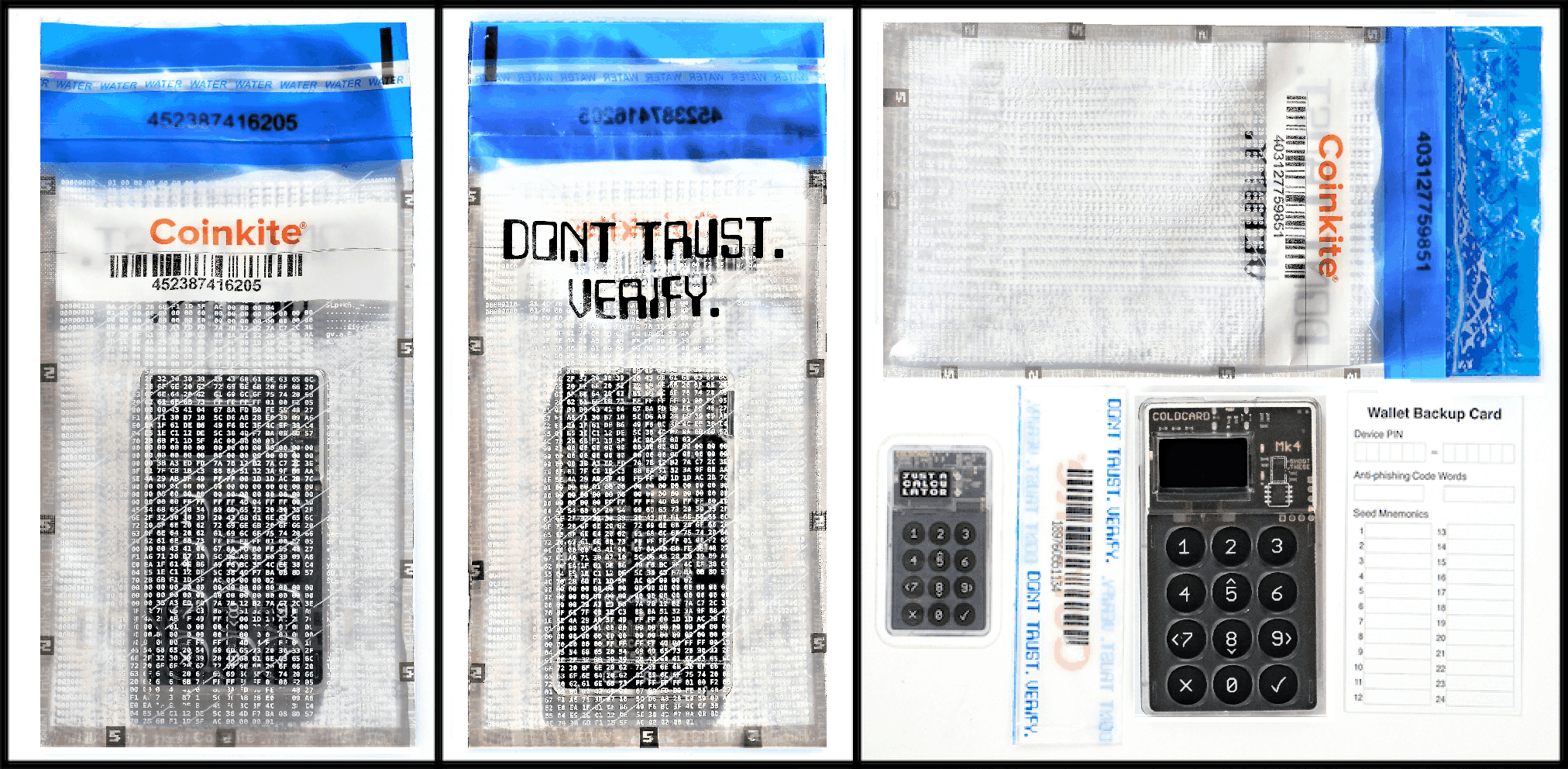
Verify The Device And Packaging of Coldcard. Image via
ColdcardInspect the bag seal and check for signs of damage or resealing. This step helps ensure that the device has not been accessed before reaching you.
Using a hardware wallet that may have been modified during shipping introduces unnecessary security risk.
Step 2: Power On And Create Your PIN
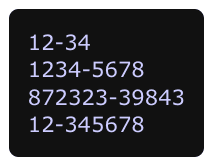
Create Your Pin. Image via
ColdcardAfter verifying the device, connect it to a power source using a trusted cable.
Coldcard uses a two-part PIN system. The first part of the PIN unlocks the device interface, while the second part confirms the login and grants access to wallet functions.
This structure helps prevent attackers from easily guessing the full PIN if they gain physical access to the device.
Users should create a PIN that is both memorable and difficult to guess. Writing the PIN down in an insecure location defeats the purpose of using a hardware wallet.
Step 3: Generate A New Seed Phrase
Setup Your New Wallet & Seed Phrase. Image via
ColdcardOnce the PIN is set, the device will generate a seed phrase that serves as the wallet's master backup.
This phrase usually consists of 12 or 24 words derived from the Bitcoin wallet standard known as BIP-39. These words allow the wallet to be restored if the device is lost or damaged.
The seed phrase will appear on the Coldcard screen one word at a time. Users must carefully record the phrase in the correct order using the provided backup card or another secure method.
This phrase must never be stored digitally in insecure locations such as screenshots, cloud notes, or email drafts. Since your recovery phrase controls your entire wallet, check our guide on protecting seed phrases from theft, loss, and physical damage.
Step 4: Confirm And Secure The Backup
After writing down the seed phrase, the device typically asks users to confirm several of the words to ensure the backup was recorded correctly.
Coldcard also offers an encrypted microSD backup option that stores an encrypted copy of the wallet backup file on a microSD card. This provides a secondary recovery path if the written seed phrase becomes damaged.
Many users combine paper or steel backups with encrypted digital backups to create redundancy.
Step 5: Pair With Compatible Wallet Software
Coldcard does not operate as a standalone wallet interface. Instead, it integrates with desktop wallet software that allows users to monitor balances and prepare transactions.
Common choices include Sparrow Wallet and Electrum, both of which support watch-only wallet setups.
In this configuration, the desktop wallet can track balances and create transactions without having access to the private keys stored on the Coldcard device.
Step 6: Verify A Receiving Address
Before receiving funds, users should verify that the receiving address displayed on their computer matches the one shown directly on the Coldcard device.
If you are sending funds for the first time, review our beginner’s guide to crypto wallet addresses and how transactions reach the right wallet.
Malware can sometimes replace Bitcoin addresses on infected computers. Verifying the address on the hardware wallet screen ensures that funds are being sent to the correct destination.
Developing this habit significantly reduces the risk of address-replacement attacks.
Step 7: Test With A Small Transaction
After completing the setup process, it is wise to perform a small test transaction before transferring larger amounts of Bitcoin.
Send a small amount of BTC to the new address, verify that it arrives correctly, and then attempt a small outgoing transaction if desired.
This test confirms that the wallet, backup, and transaction workflows are functioning properly before storing larger balances.
Common Setup Mistakes To Avoid
Several common mistakes can undermine the security benefits of a hardware wallet.
- Rushing the seed phrase backup process is one of the most serious errors. If the phrase is written incorrectly or stored insecurely, recovery may become impossible.
- Another mistake is misunderstanding the difference between the wallet’s PIN and the optional passphrase. These serve different roles and must be managed carefully.
- Failing to verify receiving addresses on the device screen is another frequent oversight that can expose users to malware attacks.
- Finally, many users skip testing their recovery process. Performing a test restore with the seed phrase helps confirm that backups are valid before storing meaningful funds.
Once the device is set up, the next step is understanding what actually happens behind the scenes when you use Coldcard. Hardware wallets often appear simple on the surface, but their security depends on a few important architectural ideas.
Coldcard’s design revolves around isolating private keys from internet-connected devices while still allowing transactions to be created and signed. To understand how that works in practice, it helps to break down the key concepts that power the device.
How Coldcard Works
Understanding Coldcard Architecture And Offline Transaction Security Model
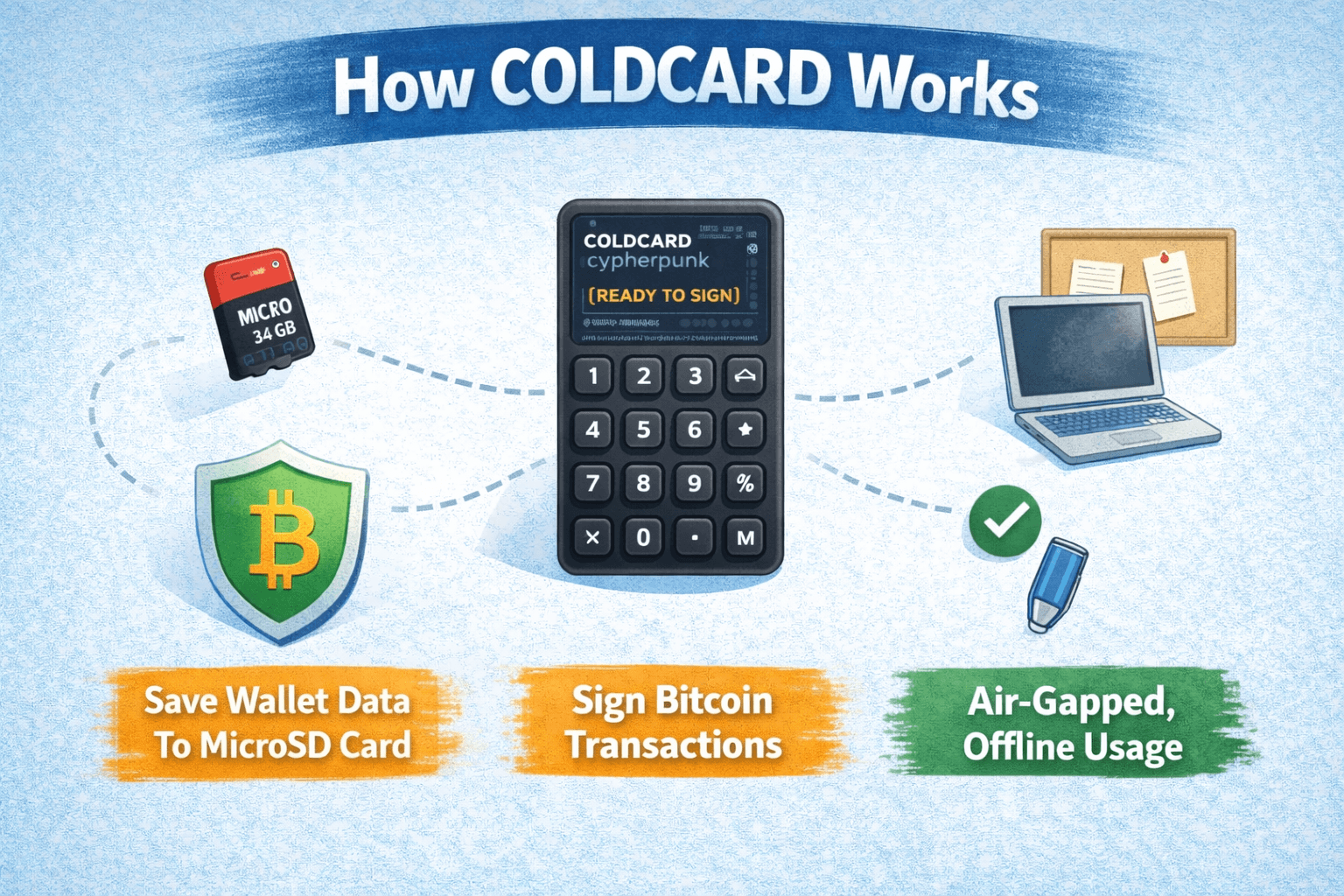
At a high level, Coldcard separates transaction creation from transaction signing. The computer or wallet software prepares a transaction, while the Coldcard device verifies and signs it using private keys stored inside the hardware wallet.
Because the signing process occurs on the device, the private keys never leave the wallet's secure environment. Even if the computer used to prepare the transaction is compromised by malware, the attacker cannot access the keys themselves.
Several technical concepts enable this architecture.
What “Air-Gapped” Means
An air-gapped device remains isolated from internet-connected systems. In the context of Coldcard, this means the wallet can operate without directly connecting to a computer through data transfer.
Instead of transmitting data over USB, users can move transaction files using a microSD card. The desktop wallet prepares the transaction and saves it as a file on the card. That file is then inserted into the Coldcard device, which reviews and signs the transaction offline.
Because the signing process happens without a live connection to the computer, malware cannot interact with the private keys during the operation.
Air-gapped workflows are considered one of the most secure ways to handle Bitcoin transactions, especially for long-term cold storage setups.
What PSBT Means
Coldcard relies heavily on a format called PSBT, which stands for Partially Signed Bitcoin Transaction.
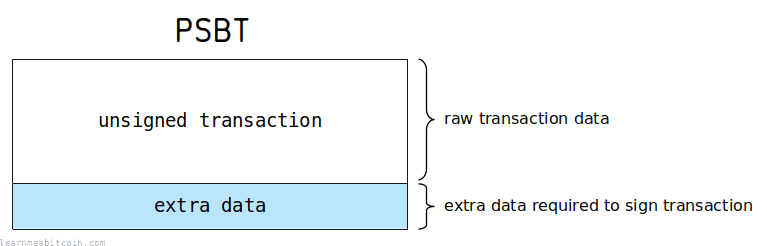
Partially Signed Bitcoin Transaction Format. Image via
LearnBitcoinPSBT is a standard that allows different devices or software systems to collaborate on a transaction without exposing private keys. Instead of signing a transaction immediately, the software prepares an unsigned transaction file that can be passed between devices.
Here is how the process typically works:
- A desktop wallet, such as Sparrow or Electrum, creates the transaction and exports it as a PSBT file. That file contains the transaction details but does not include any signatures.
- The PSBT file is then transferred to the Coldcard device, usually via a microSD card. Coldcard verifies the destination address, transaction amount, and fees before signing the transaction with the private key stored inside the device.
- Once signed, the updated PSBT file can be moved back to the desktop wallet, which broadcasts the transaction to the Bitcoin network.
This approach ensures the private key never leaves the hardware wallet.
PSBT is also widely used in multisignature wallets, where multiple devices must sign the same transaction for it to be valid.
What the Secure Element and Offline Signing Actually Do
Coldcard protects private keys using a combination of secure hardware components and offline signing workflows.
The device contains a secure element chip designed to protect sensitive cryptographic material from extraction. Even if an attacker gains physical access to the wallet, accessing the private key stored in the secure element is extremely difficult.
When a transaction is approved on the device, the signing process happens internally within this protected environment. The signed transaction is then exported without revealing the underlying private key.
This separation between transaction preparation and signing ensures that private keys remain isolated even when interacting with external software.
Why Bitcoin-Only Can Improve Security
Coldcard’s Bitcoin-only design is not just a philosophical choice. It also has technical security implications.
Supporting multiple blockchains requires additional code, additional transaction formats, and additional wallet logic. Each of these elements introduces more complexity and potential vulnerabilities.
By focusing exclusively on Bitcoin, Coldcard’s firmware remains smaller and easier to audit. A reduced codebase can make it easier for security researchers and developers to review the system and detect vulnerabilities.
This design choice does come with a trade-off. Users who hold multiple cryptocurrencies will need additional wallets to manage their assets.
However, for individuals who store Bitcoin as a long-term asset, the Bitcoin-only approach can simplify the security model and reduce unnecessary risk.
Understanding Coldcard’s architecture makes it easier to see why the wallet is often associated with air-gapped Bitcoin security. In practice, this approach means transactions can be created, signed, and broadcast without ever exposing private keys to an internet-connected computer.
The workflow may feel unfamiliar at first, but once you learn it, it becomes a powerful way to keep signing operations completely offline.
How To Perform Air-Gapped Transactions On Coldcard
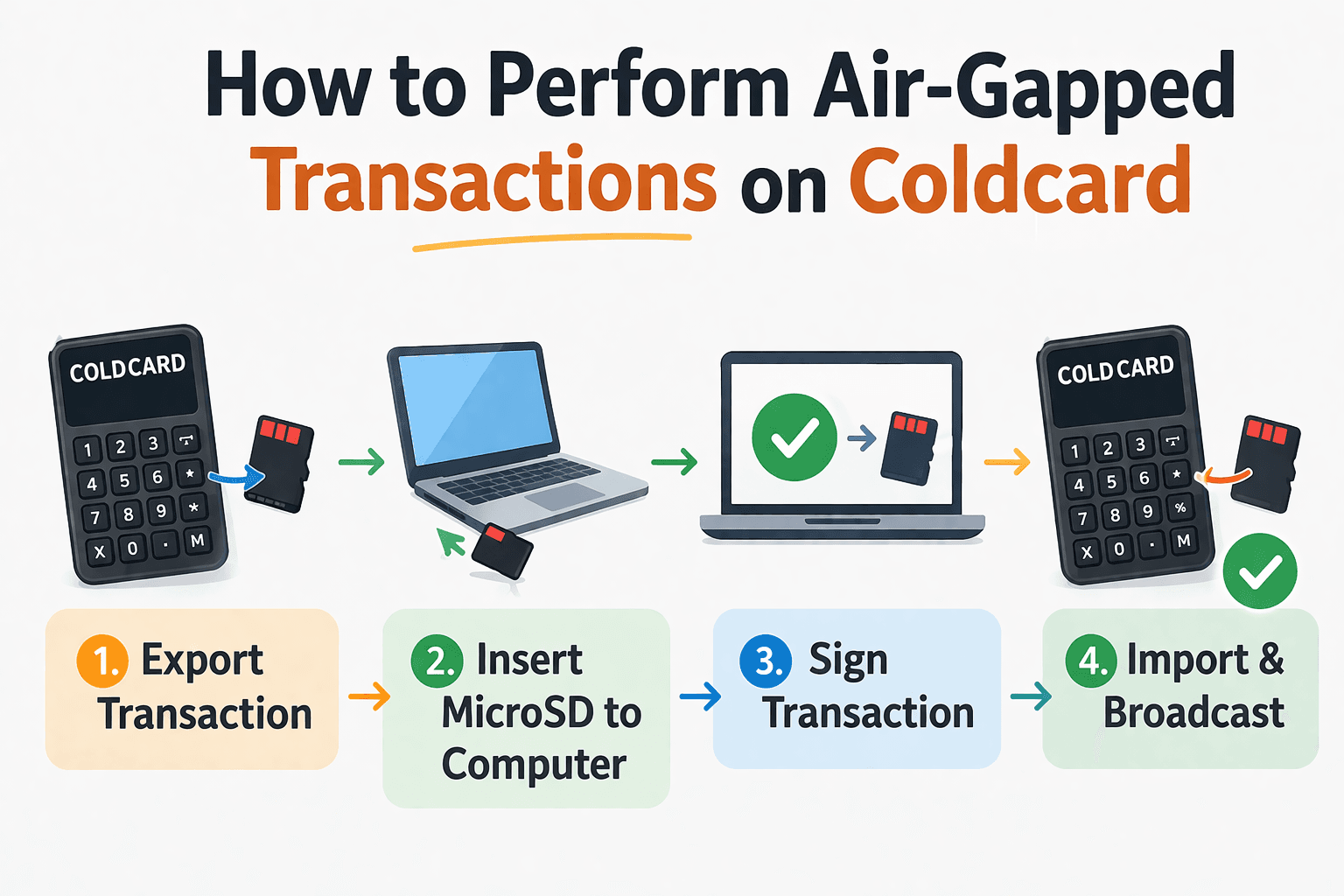
Air-Gapped Signing Workflow Protects Private Keys From Online Exposure
Coldcard’s air-gapped transaction process is one of the device’s defining security features. Instead of signing transactions while connected to a computer, the signing process happens offline inside the Coldcard device.
This is achieved using PSBT files and microSD cards. A transaction is first prepared on a desktop wallet, transferred to Coldcard through a microSD card, signed on the device, and then returned to the computer for broadcasting.
Because the Coldcard never needs to exchange transaction data directly with an internet-connected system, the private keys remain isolated from malware and remote attackers.
To understand how this works in practice, it helps to break the process into receiving and sending workflows.
What You Need
Before performing an air-gapped transaction, ensure the necessary components are in place. The workflow relies on a few basic tools working together.
You will typically need:
- Coldcard hardware wallet
- microSD card
- Desktop wallet software such as Sparrow Wallet or Electrum
- Power source for Coldcard (USB power cable or external battery pack)
- A configured watch-only wallet connected to your Coldcard
The desktop wallet is responsible for preparing and broadcasting transactions. Coldcard’s role is strictly to verify and sign transactions using the private key stored inside the device.
Once these components are ready, you can perform fully offline transaction signing.
Air-Gapped Receiving Workflow
Receiving Bitcoin with Coldcard does not require signing a transaction, but address verification remains critical for security.
Malware on a computer can sometimes replace Bitcoin addresses with attacker-controlled ones. Coldcard protects against this by allowing users to verify receiving addresses directly on the device screen.
The receiving workflow usually follows these steps:
Step 1: Generate a Receiving Address
Open your connected desktop wallet (for example, Sparrow or Electrum) and generate a new receiving address.
The software will display a Bitcoin address that can be shared with the sender.
Step 2: Verify the Address on the Coldcard Device
Before using the address, confirm it directly on the Coldcard screen.
To do this:
- Navigate to the address verification option on the device
- Compare the address displayed on the Coldcard with the one shown on your computer
- Confirm that both addresses match exactly
This step ensures that the address has not been altered by malware.
Step 3: Share the Address
Once the address is verified on the device, it can be safely shared with the sender.
After the sender broadcasts the transaction, the desktop wallet will detect the incoming Bitcoin and update the balance.
Coldcard itself does not need to remain connected during this process because the desktop wallet tracks blockchain activity.
Air-Gapped Sending Workflow Using PSBT
Sending Bitcoin through an air-gapped workflow involves several stages. Each stage keeps the private key isolated inside the Coldcard device.
The process is slightly longer than standard wallet transactions but provides significantly stronger security.
Step 1: Create the Transaction on Your Desktop Wallet
Start by opening your desktop wallet and creating a transaction.
Enter the following information:
- Recipient’s Bitcoin address
- Amount to send
- Transaction fee rate
Instead of broadcasting the transaction immediately, choose the option to export the transaction as a PSBT file.
Save the PSBT file to the microSD card.
Step 2: Transfer the PSBT File to Coldcard
Remove the microSD card from the computer and insert it into the Coldcard device.
Coldcard will detect the PSBT file stored on the card.
On the device:
- Navigate to the Ready To Sign menu
- Select the PSBT transaction file
- Load the transaction details for review
Step 3: Review Transaction Details on the Device
Coldcard will display the transaction information on its screen.
Carefully review the following details:
- Recipient address
- Amount being sent
- Transaction fee
Verifying these details on the Coldcard screen is critical because it prevents malware from silently altering transaction data.
If the information matches your intended transaction, you can approve the signing process.
Step 4: Sign the Transaction Offline
After approval, Coldcard signs the transaction using the private key stored inside the device.
The key never leaves the hardware wallet.
Once the signing process is complete, the Coldcard saves the signed PSBT file back to the microSD card.
Step 5: Return the Signed Transaction to Your Computer
Remove the microSD card from the Coldcard device and insert it back into the computer.
Import the signed transaction into your desktop wallet.
At this point, the transaction is fully signed and ready for broadcasting.
Step 6: Broadcast the Transaction
The desktop wallet broadcasts the signed transaction to the Bitcoin network.
Once confirmed, the transaction will appear on the blockchain, and the wallet balances will update accordingly.
Throughout this entire workflow, the private key remains isolated inside the Coldcard device.
USB Workflow vs Air-Gapped Workflow
Coldcard supports two ways of interacting with wallet software.
The first method uses a USB connection between the Coldcard and the computer. This workflow is faster and easier because transactions can be signed directly through the wallet interface.
The second method uses the air-gapped workflow, which transfers transactions using microSD cards.
The difference between the two approaches comes down to convenience versus maximum isolation.
USB workflows are convenient and suitable for many users. Air-gapped workflows, however, provide stronger protection because the Coldcard device never communicates directly with the computer during signing.
For long-term Bitcoin cold storage or high-value holdings, many users prefer the air-gapped method.
Troubleshooting Common Air-Gap Issues
Although the workflow is reliable once understood, new users sometimes encounter small operational issues.
The most common problems include:
MicroSD card not recognized
- Ensure the card is formatted correctly (usually FAT32)
- Try another microSD card if detection fails
Wallet software cannot read the PSBT
- Confirm the desktop wallet supports PSBT workflows
- Sparrow and Electrum typically provide the most reliable compatibility
Address mismatch during verification
- Re-check the wallet pairing
- Ensure the correct extended public key (xpub) was exported
Coldcard fails to sign the transaction
- Confirm the wallet firmware is up to date
- Verify that the transaction file format is supported
Most of these issues are resolved by checking wallet compatibility and ensuring firmware remains updated.
Now that the transaction workflow is clear, the next question becomes more fundamental. Security is the entire reason hardware wallets exist, so it is worth examining whether Coldcard actually delivers the level of protection its design promises.
Coldcard has developed a strong reputation among Bitcoin power users because it prioritizes defensive security layers rather than consumer convenience. The device combines offline signing, secure hardware components, and several defensive features designed to protect users even in difficult scenarios such as theft or coercion.
At the same time, no hardware wallet is perfectly secure. The real safety of any self-custody setup depends on both the device and the operational habits of the user.
Security is the defining reason Coldcard exists. The device was designed from the beginning to reduce attack surfaces around Bitcoin private keys and to support operational security practices used by serious self-custody users.
Rather than relying on a single defensive mechanism, Coldcard layers multiple protections. Some operate at the hardware level, others operate through transaction verification workflows, and several rely on user-controlled authentication systems. Evaluating these layers individually helps clarify how the wallet protects funds in real-world scenarios.
Coldcard Security Review: How Safe Is It Really?
Examining Coldcard’s Defensive Architecture And Real-World Security Strengths
Coldcard’s security model is built around isolation. The device keeps private keys inside the hardware wallet and requires user verification for every critical action. Signing operations occur inside the device, and the wallet encourages workflows that avoid direct connections with internet-connected machines.
This layered approach is what gives Coldcard its reputation among security-focused Bitcoin users. Each protection mechanism serves a specific role within the self-custody model.
Security Features That Matter Most
Coldcard includes a set of defensive features designed to protect private keys and prevent unauthorized access. These mechanisms operate together rather than independently, which is why understanding their roles individually is helpful.
Offline Signing
Coldcard allows transactions to be signed entirely offline. Instead of connecting directly to a computer for transaction signing, users can move transaction files between devices using microSD cards.
This air-gapped workflow keeps the signing process isolated from internet-connected systems. Even if a computer used to create the transaction is compromised by malware, the attacker cannot access the private keys inside the Coldcard device.
Secure Element
Coldcard uses a secure element chip designed to protect cryptographic secrets. A secure element is a specialized microcontroller built to resist physical tampering and side-channel attacks.
Private keys generated by the wallet are stored inside this chip. Extracting those keys without authorization is extremely difficult because the chip includes hardware protections against direct probing and fault injection attacks.
PIN Protection
Coldcard requires a PIN code to unlock the device and access wallet functions. The wallet uses a two-part PIN structure, meaning users enter the PIN in two segments rather than a single continuous code.
This design reduces the risk of observation attacks because the full PIN cannot be easily inferred from partial entry attempts. Without the correct PIN, the device cannot reveal wallet data or sign transactions.
Anti-Phishing Words
To protect against device tampering and phishing attempts, Coldcard displays a pair of anti-phishing words after the first half of the PIN is entered.
These words are unique to the device and should match the words shown during the original setup process. If the words ever appear different, it signals that something may be wrong with the device or the authentication process.
Passphrase Support
Coldcard supports optional BIP-39 passphrases. A passphrase acts as an additional secret layered on top of the seed phrase.
When used, the passphrase creates an entirely separate wallet derived from the same seed. Without the correct passphrase, the wallet derived from the seed phrase cannot be accessed.
This feature allows users to maintain hidden wallets or additional layers of protection beyond the primary seed backup.
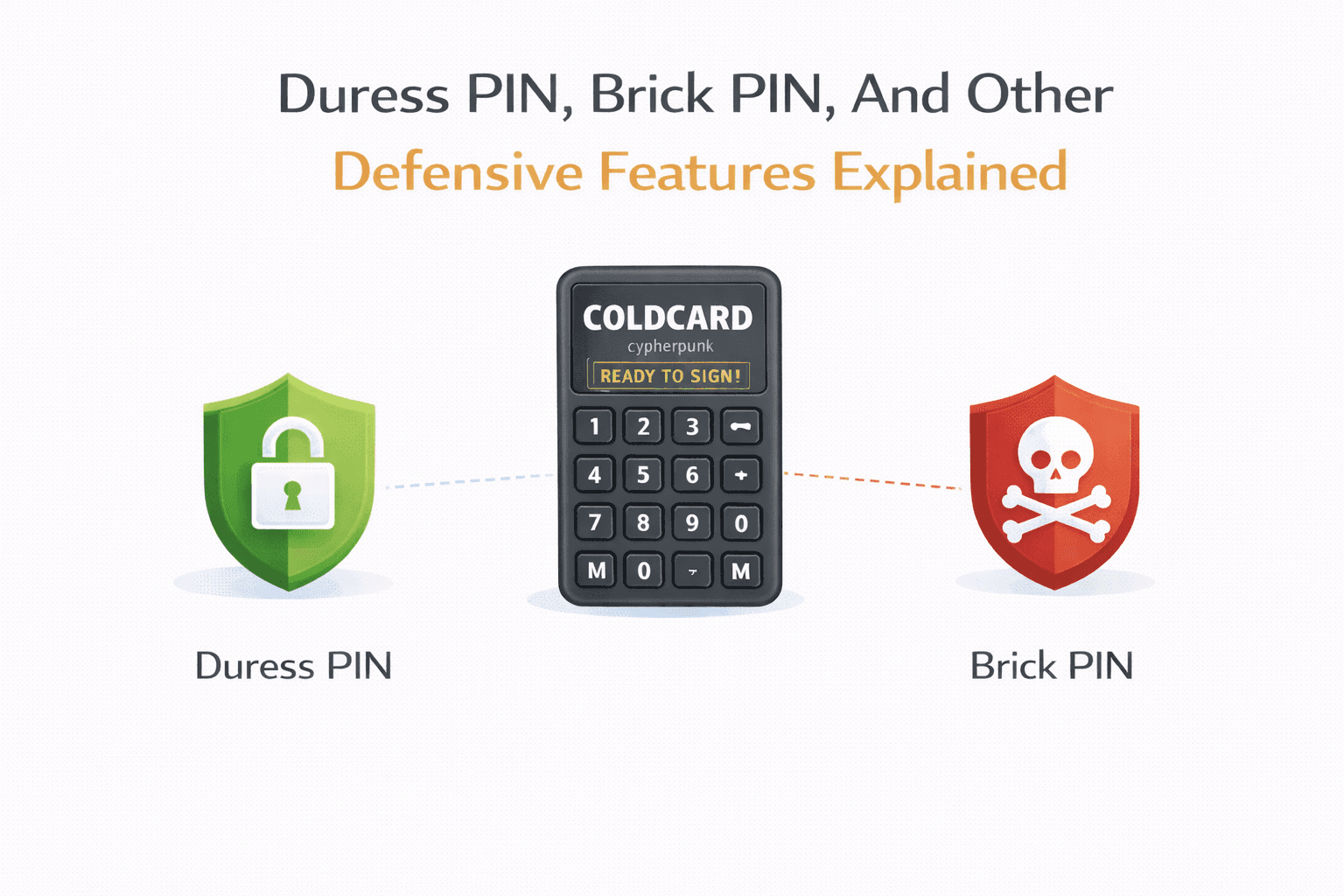
Duress PIN and Brick-Me PIN
Coldcard includes defensive PIN options intended for extreme situations. A duress PIN can unlock a decoy wallet or a limited wallet environment rather than the primary wallet.
The brick-me PIN permanently disables the device if entered. The hardware becomes unusable, protecting the private keys if the device is seized by an attacker.
These features are rarely needed for everyday use but can be useful for users concerned about coercion or forced access.
Login Countdown and Delay Mechanisms
Coldcard includes mechanisms that slow down repeated login attempts. After incorrect PIN entries, the device may introduce delays before another attempt can be made.
These delays increase exponentially with additional failures, making brute-force attacks significantly more difficult.
Failed-Attempt Wipe Behavior
Some Coldcard configurations allow the device to wipe itself after repeated failed authentication attempts. This protects the wallet if someone attempts to guess the PIN repeatedly.
If the wipe condition is triggered, the device resets and removes sensitive data from memory. Funds remain recoverable using the seed phrase backup.
Tamper-Evident Packaging
Coldcard devices ship in tamper-evident bags that show visible signs if the packaging has been opened or altered.
Inspecting the packaging before using the wallet helps protect against supply-chain attacks, where malicious actors modify hardware wallets before they reach the user.
Physical Tamper Resistance
Coldcard hardware includes protective elements designed to discourage physical tampering. Some internal components are protected by epoxy layers or physical design choices that make invasive attacks more difficult.
While no hardware device is completely immune to physical attacks, these protections increase the effort required to extract secrets directly from the device.
Transparent And Inspectable Design
Coldcard’s firmware and many parts of its design philosophy emphasize transparency and inspectability. The focus on Bitcoin-only functionality helps keep the firmware smaller and easier to audit compared with multi-asset wallets.
For security-focused users, this approach can make it easier to evaluate how the device handles sensitive operations.
For an even safer setup process, check our breakdown of common hardware wallet mistakes that can compromise your crypto.
Duress PIN, Brick PIN, And Other Defensive Features Explained
Coldcard Includes Emergency PIN Features Designed For Coercion Scenarios
Coldcard includes several defensive features designed for situations where a user may face coercion or unauthorized access attempts. These mechanisms provide additional responses beyond standard PIN authentication.
Duress PIN
A Duress PIN unlocks a secondary “decoy” wallet rather than the main wallet containing the user’s actual funds. When this PIN is entered, the device behaves normally and reveals a separate wallet that may hold a small amount of Bitcoin. The purpose is to give the appearance that the wallet has been unlocked successfully without exposing the real funds secured by the main PIN.
When It Helps
This feature is intended for coercion scenarios, such as physical threats or forced wallet access. By presenting a believable wallet with limited funds, the owner can avoid revealing the primary wallet that holds the majority of their Bitcoin.
The Risk Of Misconfiguration
If the Duress wallet is not properly prepared, it may look suspiciously empty or unrealistic. This can defeat the purpose of the feature. Users must also ensure they clearly remember which PIN unlocks which wallet, otherwise they could accidentally access the wrong wallet during normal use.
Brick PIN
The Brick PIN is an emergency PIN that permanently disables the Coldcard device when entered. Once triggered, the wallet becomes unusable and cannot be restored to normal operation. This feature exists to protect the device in extreme situations where the owner prefers destroying the wallet rather than allowing someone else to access it.
When It Helps
This function can be useful in scenarios where a device may be forcibly accessed and the owner wants to prevent any possibility of wallet compromise. Even if an attacker obtains the device, the Brick PIN ensures the hardware itself can no longer be used.
The Risk Of Misconfiguration
Because the Brick PIN permanently disables the device, accidentally entering it can destroy access to the hardware wallet. Although funds remain recoverable using the seed phrase on another compatible wallet, users could temporarily lose access if they are not prepared with a proper backup.
Other Defensive PIN Mechanisms
Coldcard also supports additional protective behaviors such as login delays, PIN attempt limits, and anti-phishing word checks. These features help detect tampering and prevent attackers from brute-forcing the PIN.
When They Help
These mechanisms become important when a device is lost or stolen. Delays and attempt limits slow down unauthorized access attempts, while anti-phishing words help users confirm that the device has not been modified.
The Risk Of Misconfiguration
Incorrectly configuring PIN delays or forgetting PIN combinations can lock users out of their own device. Like many security features, these protections work best when the user maintains clear records of their recovery information and backup procedures.
Real Security Strengths
Once the defensive PIN mechanisms and tamper protections are understood, it becomes easier to see where Coldcard’s security model genuinely stands out. The wallet is not simply relying on hardware protection alone; it combines offline transaction signing, strict operational workflows, and Bitcoin-focused design choices to reduce common attack surfaces.
These architectural decisions make the device particularly attractive to users who treat self-custody as a long-term security responsibility rather than a convenience feature.
Very Strong For Keeping Private Keys Offline
Coldcard is designed so that private keys never need to touch an internet-connected device. Transactions can be prepared on a computer, exported as PSBT files, signed on the Coldcard itself, and then returned to the computer for broadcasting. Because the signing process happens entirely inside the device, the private keys remain isolated from malware or compromised systems.
This air-gapped approach significantly reduces the chances that a compromised computer could extract sensitive wallet data.
Excellent For Disciplined Self-Custody Users
Coldcard rewards users who are comfortable with operational security practices. Individuals who understand seed backups, passphrases, address verification, and node-based verification will find that the device supports these practices well.
Instead of simplifying the workflow at the expense of control, Coldcard gives users fine-grained custody control, which is especially valuable for long-term holders managing meaningful Bitcoin balances.
Better Suited Than Mainstream Wallets For Advanced Bitcoin Setups
Coldcard integrates naturally with advanced Bitcoin infrastructure such as PSBT workflows, multisignature wallets, and personal nodes. Many experienced Bitcoin users rely on desktop wallets like Sparrow or Electrum and prefer verifying transactions through their own node.
In these environments, Coldcard becomes a powerful signing device rather than just a standalone wallet. This flexibility makes it particularly useful for multisig setups or node-based custody strategies where multiple devices coordinate to sign transactions.
Real Security Weaknesses And User Risks
Despite its strong security model, no hardware wallet can eliminate risk entirely. In practice, many security failures come from operational mistakes rather than device vulnerabilities.
Coldcard’s advanced feature set can introduce complexity, and that complexity itself becomes a potential risk if users do not fully understand the workflows involved.
Complexity Is Itself A Risk: Coldcard provides powerful security tools, but the learning curve is steeper than most consumer hardware wallets. Users unfamiliar with PSBT transactions, wallet exports, or microSD workflows may initially find the device confusing.
Mistakes With Backup Or Passphrases Can Be Catastrophic: The seed phrase and optional passphrase ultimately control access to the funds. Losing a seed phrase, misrecording it, or forgetting a passphrase can permanently lock users out of their Bitcoin.
User Error Can Defeat Device-Level Security: Even the most secure hardware wallet cannot protect funds if users expose their seed phrase digitally, fall for phishing attacks, or fail to verify receiving addresses on the device screen.
Physical Theft and Seed Exposure Remain Critical Risks: If someone gains access to the seed phrase or backup materials, the funds can be recovered on another compatible wallet. For this reason, secure storage of recovery backups remains one of the most important aspects of hardware wallet security.
Together, these points highlight an important truth: Coldcard’s security model is extremely strong, but it assumes the user is willing to follow disciplined custody practices.
Is Coldcard Safer Than Ledger Or Trezor?
Coldcard is often considered stronger in Bitcoin-only, air-gapped, and advanced self-custody setups. Its design emphasizes isolation and operational security rather than convenience.
However, it is not automatically the best choice for every user. Wallets from Ledger and Trezor offer simpler interfaces and broader asset support, which may be more practical for beginners.
Ultimately, the safest wallet depends on how it is used. Poor operational security can undermine any hardware wallet, regardless of its architecture.
Security features protect the wallet itself, but long-term safety ultimately depends on how well the backup and recovery process is handled. Hardware wallets can fail, be lost, or become physically damaged. When that happens, the seed phrase and recovery strategy are what determine whether the funds remain accessible.
Coldcard provides multiple ways to back up wallet data, ranging from traditional seed phrases to encrypted microSD backups. Each method offers different levels of durability, redundancy, and operational complexity. Understanding these options helps users build a recovery plan that matches the value of the Bitcoin being stored.
Backup And Recovery Strategies
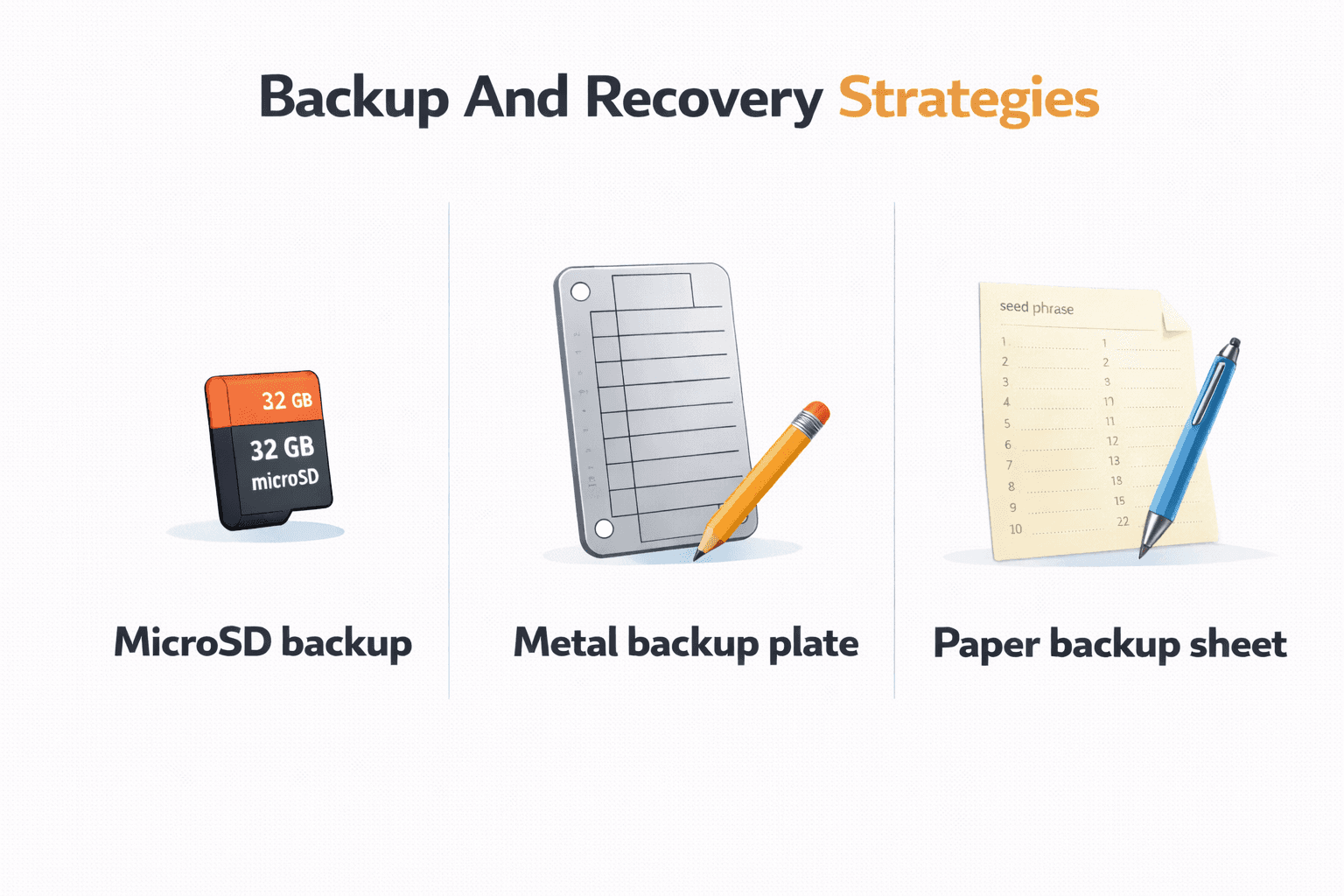
Protecting Bitcoin Access Through Secure Redundant Backup And Recovery Methods
Backing up a hardware wallet is one of the most important steps in self-custody. If the Coldcard device stops working or is destroyed, the wallet can still be restored as long as the recovery information is available.
Coldcard supports several backup methods, and many experienced users combine more than one approach to reduce single points of failure.
Your Backup Options
Coldcard provides several backup mechanisms that can be used individually or together, depending on the user’s security preferences.
Seed Phrase Backup
The most fundamental backup method is the seed phrase, usually consisting of 12 or 24 words generated during the wallet setup process.
These words represent the master key that can recreate the wallet on another Coldcard device or any compatible Bitcoin wallet software that supports the same recovery standard.
Because the seed phrase controls access to the funds, it must be stored securely and never shared. Anyone with access to the seed phrase can restore the wallet and move the Bitcoin.
Encrypted microSD Backup
Coldcard offers an additional backup option through encrypted microSD files. During setup, the device can generate an encrypted backup file that is stored on a microSD card.
This file contains the wallet data but is protected by encryption, meaning it cannot be accessed without the correct password.
Encrypted backups provide redundancy in case the written seed phrase becomes damaged or unreadable.
Optional Passphrase
Coldcard also supports optional BIP-39 passphrases, which act as an additional secret layered on top of the seed phrase.
When enabled, the passphrase generates a completely separate wallet derived from the same seed. Without the correct passphrase, the wallet cannot be restored even if the seed phrase is known.
Some users use this feature to create hidden wallets or additional protection against physical theft.
Steel Backup Solutions
Many experienced Bitcoin holders choose to transfer their seed phrase to steel backup plates rather than relying solely on paper.
Steel backups protect against fire, water damage, and physical deterioration. This makes them especially valuable for long-term storage of large Bitcoin holdings.
Paper Backup vs Steel Backup
The choice between paper and steel backups depends largely on the amount of Bitcoin being stored and the expected storage duration.
Paper backups are inexpensive and easy to create. For smaller balances or short-term storage, they may be sufficient.
However, paper is vulnerable to environmental damage. Fire, water, and physical wear can destroy a paper backup over time.
Steel backups, on the other hand, are designed to survive extreme conditions. Many steel plates can withstand high temperatures and physical damage that would destroy paper.
For long-term storage of meaningful Bitcoin balances, steel backups are generally the safer option.
How To Restore A Coldcard
Restoring a Coldcard wallet is straightforward as long as the recovery information is available.
The process generally follows these steps:
- Power on the Coldcard device
- Select the Restore Wallet option
- Enter the seed phrase in the correct order
- Enter the optional passphrase if one was used
- Confirm the wallet configuration
Once restored, the device will regenerate the same private keys and addresses that existed on the original wallet.
Balances will appear again after the wallet software synchronizes with the Bitcoin blockchain.
Coldcard can also restore wallets from encrypted backup files stored on microSD cards, provided the correct password is available.
Best Practices For Backup Storage
Creating a backup is only the first step. Storing the backup properly is equally important.
A good backup strategy usually includes:
- Storing backups in multiple locations to avoid a single point of failure
- Keeping seed phrases separate from passphrases
- Avoiding digital storage, such as cloud services or screenshots
- Protecting backups from fire, water, and physical damage
Some users also perform a test recovery using their backup before storing large amounts of Bitcoin. This confirms that the backup information was recorded correctly.
If you want a practical walkthrough of secure storage strategies, watch this video explaining the safest ways to store crypto and protect your private keys.
What Happens If You Lose The Device?
One common misunderstanding about hardware wallets is that the funds are stored on the device itself.
In reality, the Bitcoin remains on the blockchain. The hardware wallet simply stores the private keys required to access it.
If the Coldcard device is lost, stolen, or destroyed, the wallet can be restored using the seed phrase and optional passphrase on another Coldcard or compatible wallet.
The real danger occurs if both the device and the recovery backup are lost. Without the seed phrase or backup file, there is no way to restore access to the funds.
This is why backup planning is such a critical part of responsible self-custody.
How To Update Coldcard Firmware Safely
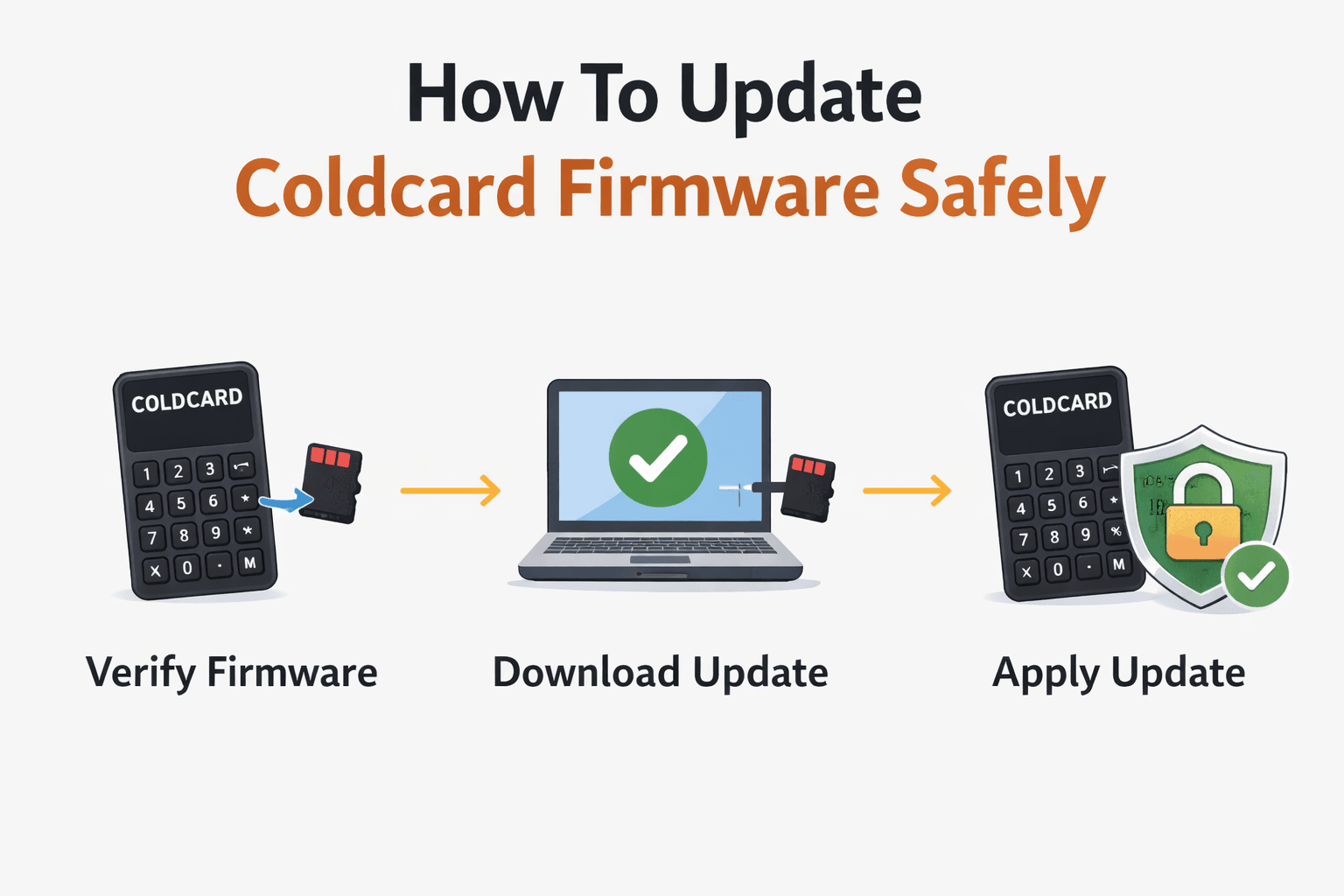
Understanding Coldcard Pricing And Secure Purchasing Considerations
Coldcard firmware updates follow a security-first workflow similar to the device’s transaction model. Instead of automatically downloading updates through an internet connection, the user manually retrieves firmware files and installs them through the device.
This approach reduces the risk of malicious firmware being installed silently. It also gives users full control over verifying update authenticity before installation.
Why Firmware Updates Matter
Firmware controls how the Coldcard device generates keys, verifies transactions, and interacts with wallet software. Over time, updates may introduce security improvements, compatibility changes, or bug fixes that affect how the wallet behaves.
For example, firmware updates can strengthen protections against new attack techniques, improve compatibility with desktop wallets such as Sparrow or Electrum, and introduce additional security features or usability improvements. Ignoring updates for long periods can eventually lead to compatibility issues with modern wallet software or leave the device running outdated security logic.
At the same time, firmware updates should never be installed casually. Because firmware controls the wallet’s core behavior, verifying the authenticity of the update is an important part of the process.
How To Verify Firmware Before Updating
Before installing any firmware update, users should confirm that the file came from the official Coldcard source and has not been altered.
The first step is downloading the firmware only from the official Coldcard or Coinkite website. Hardware wallet firmware should never be downloaded from unofficial mirrors, forums, or random links shared online.
Coldcard firmware files are typically accompanied by verification information that allows users to confirm the file’s authenticity. This verification process ensures the firmware has not been modified by a malicious actor before installation.
Users who follow advanced security practices may verify the firmware signature using tools provided by the Coldcard development team. This step confirms that the firmware was produced by the legitimate developers and has not been tampered with.
Although this verification process requires some technical familiarity, it significantly reduces the risk of installing malicious firmware.
Firmware Update Process
Updating Coldcard firmware generally involves transferring the firmware file to the device using a microSD card. The process avoids direct internet connections and maintains the wallet’s offline workflow philosophy.
The typical update process follows these steps:
Download the latest firmware file from the official Coldcard website.
Copy the firmware file onto a formatted microSD card.
Insert the microSD card into the Coldcard device.
Navigate to the firmware upgrade option within the device menu.
Select the firmware file and confirm installation.
Wait for the device to complete the update and reboot.
After the installation finishes, the Coldcard device will restart and operate using the updated firmware version.
It is always wise to confirm the firmware version on the device screen after the update to ensure the process completed successfully.
Firmware Update Risks To Avoid
Although firmware updates are routine maintenance, several mistakes can introduce unnecessary risk.
Downloading firmware from unofficial sources is the most serious risk. Malicious firmware could potentially compromise the wallet and expose private keys.
Another common mistake is interrupting the update process. Removing power while firmware installation is underway can corrupt the device’s software.
Skipping authenticity checks is another risk. Even if the firmware appears legitimate, verifying the file ensures it has not been altered.
Finally, users should avoid updating firmware without understanding the process. Reading the official documentation beforehand helps prevent mistakes during installation.
When performed carefully, firmware updates keep the Coldcard device secure while maintaining compatibility with modern wallet software.
With the operational aspects covered, the next step is looking at the wallet’s functional capabilities. Coldcard’s reputation does not come from a single feature but from a collection of design choices that focus on Bitcoin self-custody.
Each feature plays a specific role in how the wallet protects private keys, interacts with wallet software, and supports advanced Bitcoin setups. Some of these features provide clear security advantages, while others introduce a learning curve that new users should be aware of.
Understanding how these features work in practice helps clarify why Coldcard is often favored by experienced Bitcoin users.
Coldcard Features Breakdown
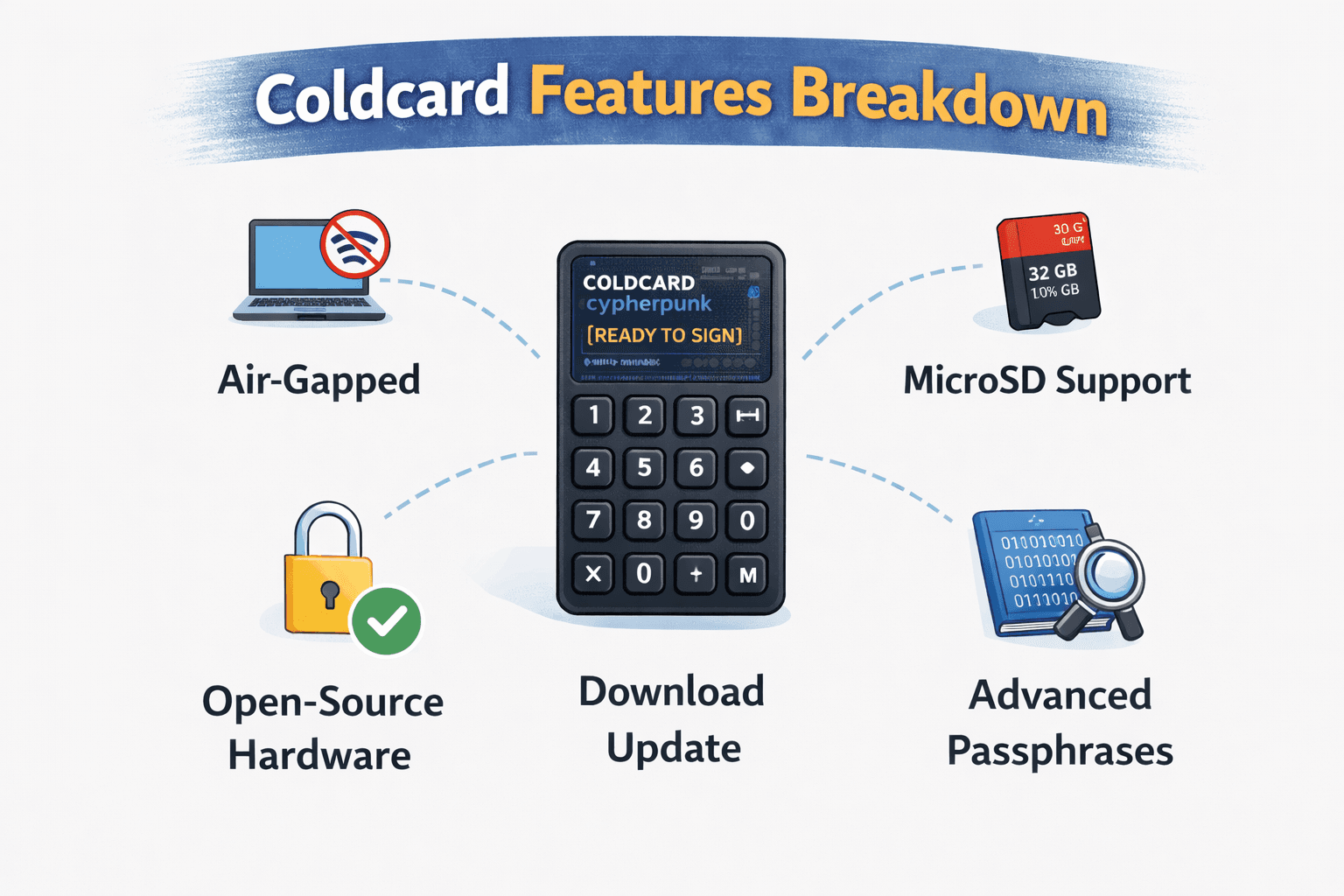
Key Coldcard Features That Enable Advanced Bitcoin Self-Custody
Coldcard is not designed as a general-purpose crypto wallet. Instead, it focuses on features that support Bitcoin security practices such as air-gapped signing, multisignature coordination, and node-based transaction verification.
The following features represent the core capabilities that define the Coldcard ecosystem.
Bitcoin-Only Design
Coldcard follows a strict Bitcoin-only philosophy. Rather than supporting multiple blockchains, the device focuses entirely on the Bitcoin network and its transaction model.
What It Is
A Bitcoin-only wallet stores and signs transactions exclusively for Bitcoin. The firmware and transaction logic are built around Bitcoin’s scripting system and standards such as BIP-39 and PSBT.
Coldcard does not support altcoins, tokens, or NFTs. Every component of the device is optimized for Bitcoin operations.
Why It Matters
Supporting multiple blockchains increases firmware complexity. Each additional network introduces different address formats, signing rules, and transaction structures.
By focusing only on Bitcoin, Coldcard keeps its firmware smaller and easier to audit. This can reduce the attack surface compared with multi-asset wallets.
Who Benefits From It
Bitcoin maximalists and long-term Bitcoin holders benefit the most from this approach. Users who primarily store BTC often prefer tools that prioritize security rather than multi-chain compatibility.
Downside Or Learning Curve
The obvious limitation is asset support. Users who hold Ethereum, tokens, or other cryptocurrencies must use separate wallets to manage those assets.
PSBT Support
Coldcard relies heavily on the PSBT standard to coordinate transaction signing between the hardware wallet and external software.
What It Is
PSBT stands for Partially Signed Bitcoin Transaction. It is a standardized format that allows different wallets and devices to collaborate on a transaction without exposing private keys.
Instead of signing transactions immediately, a wallet can create a partially prepared transaction file that is later signed by a hardware wallet.
Why It Matters
PSBT enables secure workflows where the computer prepares the transaction while the hardware wallet performs the signing. This separation protects the private key from malware on the computer.
The format also allows multiple devices to sign the same transaction, which is essential for multisignature setups.
Who Benefits From It
Advanced users who operate multisignature wallets or air-gapped setups rely heavily on PSBT workflows. The format also makes Coldcard compatible with many Bitcoin wallet applications.
Downside Or Learning Curve
For beginners, the PSBT workflow may feel unfamiliar. Understanding how unsigned and signed transactions move between devices requires some technical learning.
Full Node Compatibility
Coldcard works well with Bitcoin full nodes and node-connected wallets.
What It Is
A full node is software that independently verifies Bitcoin transactions and blocks without relying on third-party services.
Coldcard can be paired with node-compatible wallet software, allowing users to sign transactions while relying on their own node for blockchain verification.
Why It Matters
Using a personal node removes reliance on external blockchain explorers or wallet servers. This improves both privacy and transaction verification.
Instead of trusting third-party infrastructure, users can confirm balances and transaction history through their own node.
Who Benefits From It
Privacy-conscious users and advanced Bitcoin enthusiasts benefit most from this feature. Many Coldcard users run full nodes as part of a self-sovereign Bitcoin setup.
Downside Or Learning Curve
Running a full node requires additional hardware, storage space, and configuration. For casual Bitcoin users, the setup may feel unnecessary.
Multisig Support
Coldcard integrates well with multisignature Bitcoin wallets.
What It Is
Multisignature, often called multisig, is a security model where multiple private keys are required to authorize a transaction.
For example, a 2-of-3 multisig wallet requires any two of three keys to sign before funds can be moved.
Why It Matters
Multisig setups significantly improve security because a single compromised device cannot move funds.
This model is commonly used by institutions, family vault setups, and users protecting large Bitcoin holdings.
Who Benefits From It
High-value Bitcoin holders and organizations managing shared funds often rely on multisig setups. Coldcard’s PSBT workflow integrates smoothly with multisignature environments.
Downside Or Learning Curve
Multisig introduces additional complexity. Coordinating multiple keys and devices requires careful setup and backup planning.
microSD Backups And Offline Operations
Coldcard uses microSD cards as a central component of its offline workflow.
What It Is
The device supports encrypted backups stored on microSD cards and uses the card to transfer PSBT transaction files between devices.
This allows the Coldcard to operate without direct data connections to a computer.
Why It Matters
microSD-based workflows enable air-gapped transaction signing. This reduces exposure to malware and keeps private keys isolated during transaction approval.
The encrypted backup option also provides an additional recovery mechanism beyond the seed phrase.
Who Benefits From It
Users who prioritize maximum isolation between hardware wallets and internet-connected computers benefit most from this feature.
Downside Or Learning Curve
Handling microSD cards introduces extra operational steps. Some users may find the process slower compared with wallets that use direct USB connections.
Passphrases And Wallet Segmentation
Coldcard supports optional passphrases that create additional wallet layers.
What It Is
A passphrase acts as an additional secret, combined with the seed phrase, to generate a completely different wallet.
Each passphrase produces a unique set of Bitcoin addresses.
Why It Matters
Passphrases allow users to create hidden wallets, decoy balances, or multiple independent storage compartments using the same seed phrase.
This provides an additional layer of protection if the seed phrase becomes exposed.
Who Benefits From It
Users storing large amounts of Bitcoin often use passphrases to separate funds into multiple wallets.
Downside Or Learning Curve
Passphrases must be remembered perfectly. Losing the passphrase means losing access to the wallet derived from it.
Wallet Compatibility
Coldcard is designed to integrate with several widely used Bitcoin wallet applications.
What It Is
Instead of relying on a proprietary wallet interface, Coldcard connects with external wallet software that handles transaction creation and blockchain synchronization.
Common compatible wallets include Sparrow Wallet, Electrum, and other node-compatible tools.
Why It Matters
External wallet compatibility gives users flexibility. They can choose software that fits their preferred workflow, whether that involves privacy tools, node integration, or multisignature coordination.
Who Benefits From It
Advanced users who prefer powerful desktop wallet interfaces gain the most from this flexibility.
Downside Or Learning Curve
Because Coldcard does not provide a simple all-in-one mobile app, users must learn how to interact with third-party wallet software.
With the feature set explained, the next question is more practical. Security architecture and technical capabilities matter, but they do not fully describe what it feels like to use the device every day.
Hardware wallets are physical tools. Their design, interface, and interaction model influence how comfortable users feel reviewing transactions, navigating menus, and managing funds. Coldcard approaches design very differently from many consumer wallets, prioritizing physical control and verification over minimalistic touch interfaces.
Understanding how the device is built and how it behaves in daily use helps reveal whether its design philosophy works in practice.
Design, Build Quality, And Everyday Use
Evaluating Coldcard Hardware Design And Real-World Usability Experience
Coldcard’s physical design reflects its security-first philosophy. Instead of relying on touchscreen navigation or mobile pairing, the device emphasizes direct interaction through buttons and a small display.
The goal is to ensure that transaction verification happens entirely on the hardware wallet itself. This approach may feel old-fashioned compared with modern touchscreen wallets, but it reinforces the idea that sensitive actions should be confirmed on a trusted device.
Physical Design And Portability
Coldcard is a compact hardware wallet designed to be portable without sacrificing usability. The device includes a small screen and a physical keypad that allows users to enter PIN codes and navigate menus directly on the wallet.
The keypad is one of the device’s most distinctive features. Unlike some hardware wallets that rely on companion apps for PIN entry, Coldcard allows the entire authentication process to occur on the device itself. This reduces the risk of exposing sensitive input through a connected computer.
The screen is designed to display transaction information clearly, including recipient addresses and transaction fees. Because Coldcard encourages users to verify every transaction on the device, the screen plays a critical role in preventing address-replacement attacks.
In terms of portability, the device is small enough to store easily in a secure location such as a safe or hardware wallet storage case. Its lightweight design makes it convenient to transport when necessary, though many users keep hardware wallets stored securely rather than carrying them daily.
Day-To-Day User Experience
Using Coldcard on a daily basis feels different from using many mainstream hardware wallets. The interface relies on a combination of menu navigation and button inputs rather than touchscreen gestures.
For users familiar with hardware wallets, the menu system is straightforward. The device presents options clearly, and most actions follow a logical sequence of confirmation screens.
Transaction verification is one of the most important parts of the experience. Coldcard displays full transaction details on the device screen before signing. Users must confirm the destination address, amount, and fees using the physical keypad.
This process reinforces the wallet’s security philosophy. Instead of trusting the computer interface alone, the device ensures that the final approval happens on the hardware wallet itself.
Although the interface is functional and reliable, it does require some familiarity with the device’s menu structure. New users may need time to learn where certain functions are located.
What Using Coldcard Feels Like In Practice
In practical use, Coldcard often feels like a tool designed for deliberate interaction rather than quick transactions.
The initial setup typically takes longer than mainstream hardware wallets because users must record seed phrases carefully, verify backups, and configure wallet software. For someone new to hardware wallets, the process may take thirty to sixty minutes, depending on how carefully each step is performed.
Once configured, routine operations such as verifying addresses and signing transactions become easier. The device’s menu structure makes it possible to review transactions carefully before approval, which reinforces safe habits.
First-time users sometimes find the PSBT workflow confusing, especially when transferring files between the desktop wallet and the microSD card. After performing the process a few times, however, the steps become predictable and easier to follow.
Advanced users often appreciate the control that Coldcard provides. The device integrates well with node-based setups, multisignature wallets, and air-gapped transaction workflows.
Tips From Testing
During real-world usage, a few practical habits make the Coldcard experience smoother.
Keep a dedicated microSD card specifically for transaction files and backups.
Verify every receiving address directly on the device screen.
Perform a small test transaction before storing large balances.
Familiarize yourself with the device menus before attempting advanced features.
These small habits can prevent mistakes and make the wallet easier to manage over time.
Coldcard vs Ledger Nano X vs Trezor Model T
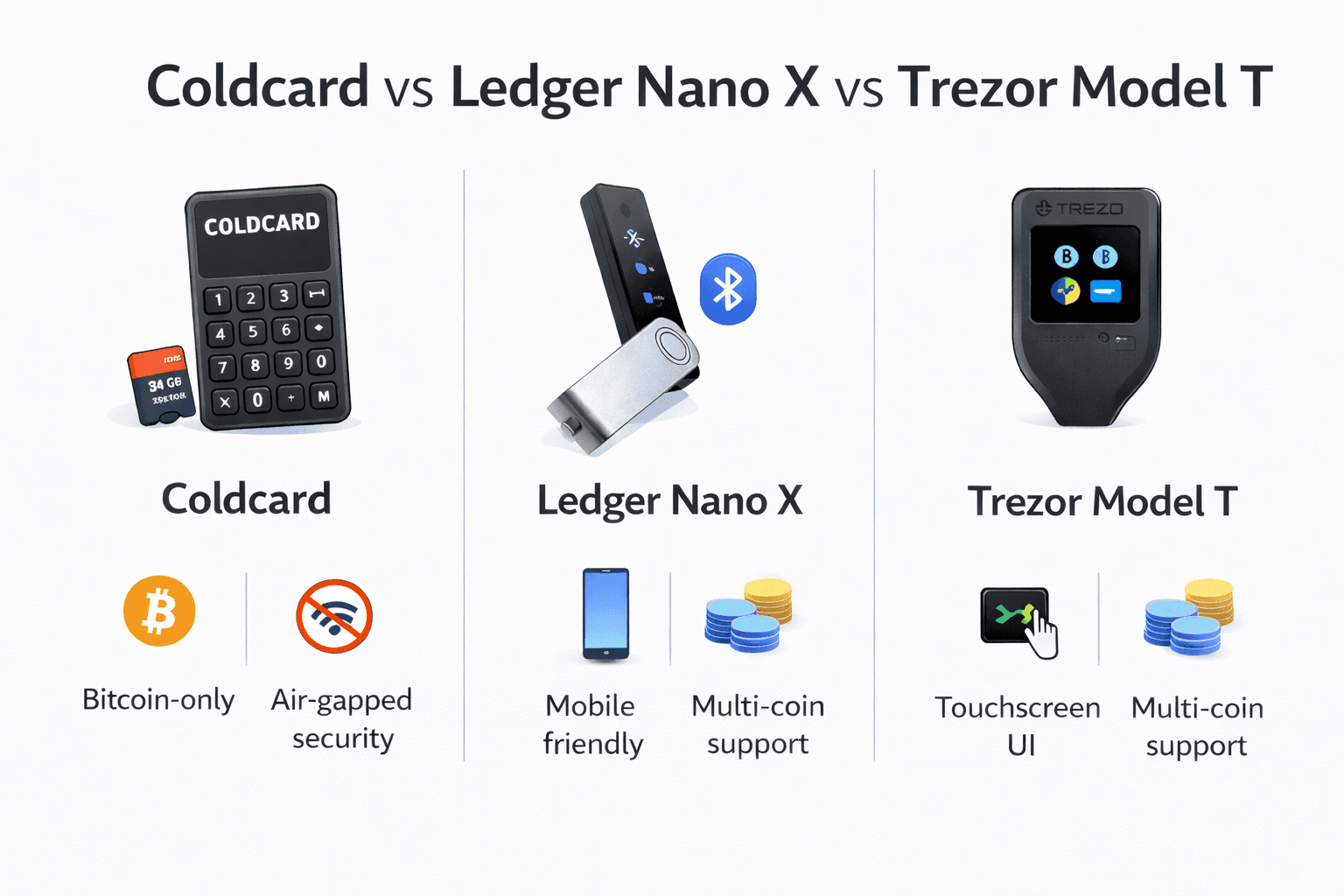
Coldcard is often compared with two of the most widely used hardware wallets in the market: the Ledger Nano X and the Trezor Model T. All three devices aim to protect cryptocurrency private keys, but they approach the problem from very different angles.
Coldcard focuses on Bitcoin self-custody and operational security, emphasizing air-gapped transaction signing and advanced control over wallet workflows. Ledger prioritizes multi-asset support and ecosystem convenience, while Trezor emphasizes open-source transparency and accessibility.
Understanding these design philosophies helps clarify why each wallet appeals to different types of users.
Quick Comparison Table
| Feature | Coldcard | Ledger Nano X | Trezor Model T |
|---|
| Supported Assets | Bitcoin only | 5,000+ cryptocurrencies | 1,000+ cryptocurrencies |
| Air-Gapped Signing | Yes (microSD PSBT workflow) | No | Limited |
| Open-Source Firmware | Mostly open | Closed secure element firmware | Fully open-source |
| Secure Element | Yes | Yes | No |
| Mobile App Support | No dedicated mobile app | Yes (Ledger Live) | Limited |
| microSD Support | Yes | No | Yes |
| Duress / Defensive Features | Yes | No | No |
| Multisig Integration | Strong | Moderate | Moderate |
| Ease of Use | Advanced | Beginner-friendly | Beginner-friendly |
| Best For | Bitcoin security setups | Multi-asset investors | Open-source users |
| Approximate Price | $150–$180 | $149 | $219 |
This comparison shows that the wallets are optimized for different priorities. Coldcard leans heavily toward security architecture, Ledger focuses on convenience and ecosystem integration, and Trezor balances transparency with usability. If budget matters as much as security, our guide to the best cheap hardware wallets is a useful comparison point.
Coldcard vs Ledger Nano X
The biggest difference between Coldcard and the Ledger Nano X is security philosophy.
Coldcard is designed around the idea that private keys should interact with internet-connected systems as little as possible. Its air-gapped transaction model allows users to move PSBT transaction files through microSD cards rather than connecting the wallet directly to a computer.
The Ledger Nano X follows a more convenience-oriented design. It connects easily to the Ledger Live mobile and desktop applications and supports Bluetooth connectivity, allowing users to manage their assets directly from a smartphone.
This convenience comes with trade-offs.
Coldcard minimizes the attack surface by reducing direct device communication with computers or mobile devices. Ledger, on the other hand, focuses on creating a smooth ecosystem where users can manage many assets through a unified interface.
From a user-fit perspective, the difference is clear:
- Coldcard is better suited for Bitcoin-focused users who prioritize security workflows and long-term cold storage.
- Ledger Nano X is better suited for investors who hold multiple cryptocurrencies and want simple portfolio management through a mobile app.
For users storing a large Bitcoin balance and interacting with node-based wallets, Coldcard often feels more aligned with those needs.
Coldcard vs Trezor Model T
Comparing Coldcard with the Trezor Model T highlights a different set of trade-offs.
Trezor emphasizes open-source transparency. Its firmware and hardware design are widely inspectable, which appeals to users who value auditability and community oversight. The Model T also includes a touchscreen interface that simplifies navigation and PIN entry.
Coldcard, by contrast, emphasizes operational security workflows. Its design focuses on air-gapped signing, microSD transaction transfers, and defensive features such as duress PINs.
Another key difference lies in asset support.
Trezor Model T supports a large number of cryptocurrencies, making it useful for users who manage diversified portfolios. Coldcard deliberately avoids multi-chain functionality and focuses entirely on Bitcoin.
From a practical standpoint:
- Trezor Model T works well for users who want an open-source wallet with a smoother user experience and multi-asset compatibility.
- Coldcard works better for advanced Bitcoin users running multisignature wallets, node setups, or air-gapped storage systems.
The choice often depends on whether the user values ease of use and transparency or maximum isolation and operational control.
Which Wallet Should You Choose?
Choosing between Coldcard, Ledger Nano X, and Trezor Model T ultimately comes down to how you approach cryptocurrency storage.
Coldcard makes the most sense for users who treat Bitcoin custody as a security discipline. Its air-gapped workflows, PSBT transaction model, and defensive features make it particularly attractive for long-term Bitcoin storage and advanced self-custody setups.
Ledger Nano X works best for users who manage multiple cryptocurrencies and want a simple interface with strong mobile support. The Ledger ecosystem makes portfolio management much easier for casual investors.
Trezor Model T sits between the two extremes. It offers open-source transparency and a beginner-friendly interface while still providing strong hardware wallet protections.
In practice, many experienced users choose their wallet based on portfolio composition and operational preferences. Someone holding only Bitcoin for long-term storage may gravitate toward Coldcard, while a diversified crypto investor may find Ledger or Trezor easier to use.
Coldcard is not the only hardware wallet designed specifically for Bitcoin users. Over the past few years, several manufacturers have introduced Bitcoin-only devices that focus on self-custody security rather than multi-asset compatibility.
Comparing Coldcard with other Bitcoin-focused wallets helps place its design philosophy in context. While these wallets share similar goals of protecting private keys and supporting advanced custody workflows, they differ in how they balance usability, transparency, and operational complexity.
Coldcard vs Other Bitcoin-Only Wallets
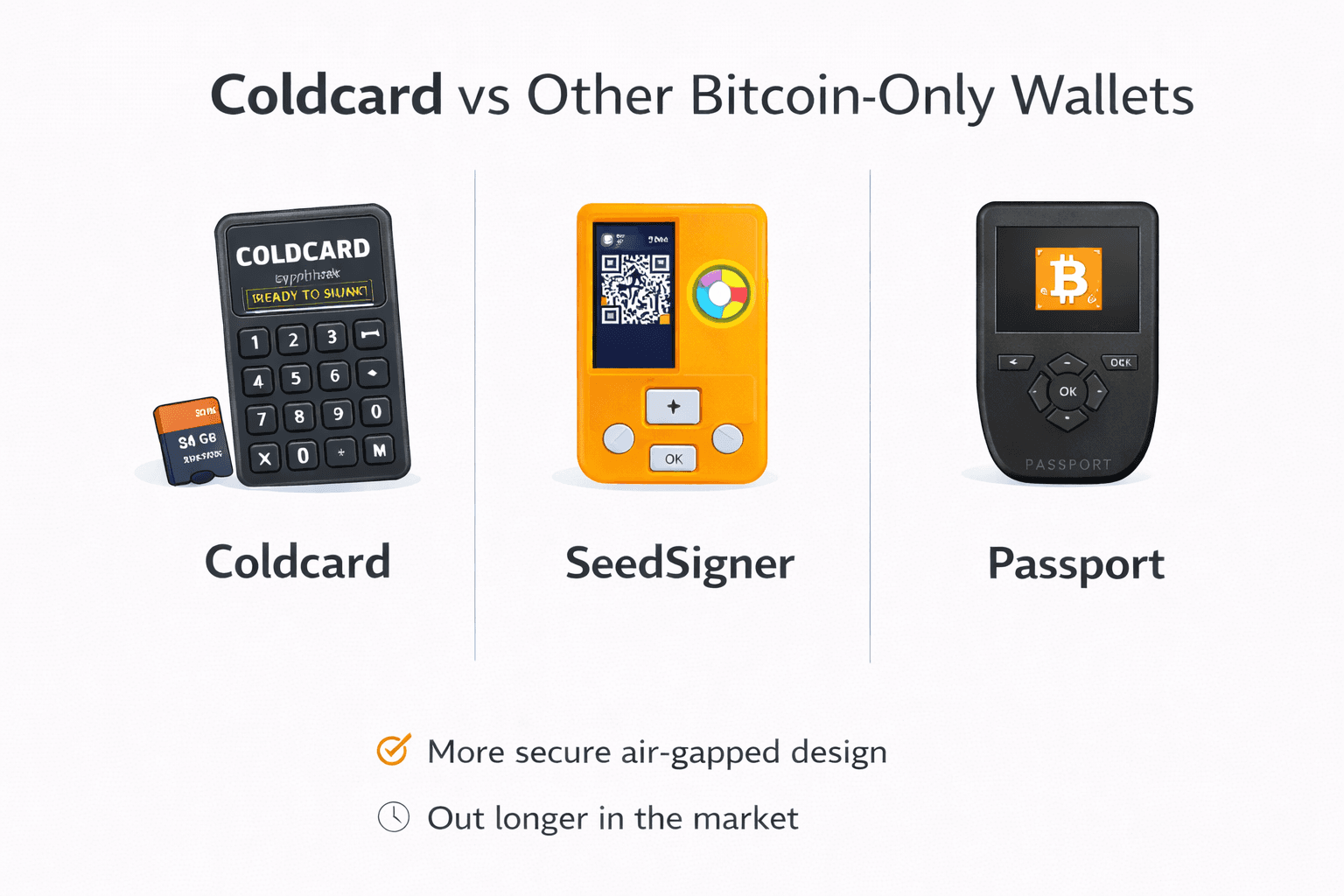
How Coldcard Compares With Leading Bitcoin-Only Hardware Wallets
A growing category of hardware wallets now targets Bitcoin-only users. Devices such as the Blockstream Jade, Foundation Passport, SeedSigner, and BitBox02 Bitcoin‑Only Edition all focus on Bitcoin security rather than supporting hundreds of cryptocurrencies.
Although they share the same core purpose, their design approaches differ in several important ways, including their security models, ease of use, and integration with the entire Bitcoin ecosystem.
Coldcard vs Jade/Passport/SeedSigner/BitBox02 Bitcoin-Only Edition
Understanding how these wallets differ requires examining four important factors: the security model, usability, open-source design, and ideal user profile.
Security Model
Coldcard is built around an air-gapped signing model, where transactions can be transferred using microSD cards rather than direct device connections. This approach minimizes the interaction between private keys and internet-connected systems.
The Blockstream Jade wallet also supports air-gapped signing but uses QR codes instead of microSD cards. This design enables completely offline transaction signing while allowing transactions to be transferred visually between devices.
SeedSigner takes a different approach. Rather than being a traditional hardware wallet, it is an open-source DIY signing device built from common hardware components such as a Raspberry Pi. Transactions are typically signed using QR codes, and the device does not permanently store private keys.
Foundation Passport closely resembles Coldcard in philosophy. It supports microSD-based PSBT workflows and emphasizes air-gapped security. The Passport device also includes a camera for QR-based transaction transfer.
BitBox02 Bitcoin-Only Edition focuses on simplicity. It does not prioritize air-gapped workflows but instead provides strong hardware key protection through a dedicated secure chip while maintaining a very streamlined user experience.
Each device protects private keys effectively, but the workflow and security assumptions differ. If you are weighing Coldcard against similar devices, this breakdown of the best Trezor alternatives also covers security-first wallet options.
Ease Of Use
Coldcard is often considered one of the most powerful Bitcoin wallets, but it also comes with a learning curve. The PSBT workflow, microSD transfers, and external wallet integration require some familiarity with Bitcoin custody tools.
Blockstream Jade attempts to simplify the experience through QR-based transactions and integration with Blockstream’s Green wallet software.
Foundation Passport offers a more polished user interface than Coldcard while maintaining air-gapped transaction support.
BitBox02 Bitcoin-Only Edition is widely regarded as one of the easiest Bitcoin hardware wallets to use. Its interface and software integration prioritize simplicity while still providing strong security protections.
SeedSigner, while powerful, is generally aimed at advanced users who are comfortable assembling and configuring their own signing devices.
Open-Source Approach
Transparency is an important topic in the hardware wallet ecosystem.
SeedSigner is fully open-source and designed specifically around transparency and reproducibility. Users can build the device themselves using publicly available instructions.
Trezor-style transparency also appears in devices such as Passport and Jade, which emphasize open development and inspectable firmware.
Coldcard’s firmware and development process incorporate open elements, but the device also includes secure hardware components that limit full hardware transparency.
BitBox02 maintains open firmware while still relying on specialized hardware security elements.
For users who prioritize open development and reproducibility, the open-source stance of each wallet may influence their decision.
Ideal User Profile
Different Bitcoin-only wallets appeal to different types of users.
Coldcard is best suited for advanced Bitcoin users who want maximum control over transaction signing and custody workflows. It integrates particularly well with multisignature setups and node-based wallets.
Blockstream Jade appeals to users who prefer QR-based signing workflows and integration with the Blockstream ecosystem.
Foundation Passport targets users who want Coldcard-style air-gapped security with a more polished user interface.
SeedSigner attracts highly technical users interested in DIY hardware and fully open-source signing devices.
BitBox02 Bitcoin-Only Edition is often recommended for users who want a simple but secure Bitcoin-only wallet without the operational complexity of Coldcard.
Each device serves a slightly different segment of the Bitcoin security community.
Comparisons help clarify where Coldcard sits in the hardware wallet landscape, but another practical question usually follows: how much does the device actually cost and where should it be purchased safely?
Hardware wallets protect private keys, which means the purchasing process itself becomes part of the security model. Buying from unreliable sources or using a device that may have been tampered with during shipping can introduce unnecessary risk.
Understanding the real cost of using Coldcard, along with safe purchasing practices, helps ensure that the wallet provides the protection it is designed for.
Coldcard Price, Value, And Where To Buy Safely
Understanding Coldcard Pricing And Secure Purchasing Considerations
Coldcard hardware wallets are positioned in the mid-range of the hardware wallet market. The price reflects the device’s focus on Bitcoin-only security features and advanced transaction workflows rather than consumer-oriented convenience tools.
When evaluating the cost, it is also important to consider additional accessories that may be required to operate the wallet safely over the long term.
How Much Coldcard Costs
The current retail price for the Coldcard Mk4 typically falls in the range of $150 to $180 USD, depending on the retailer and any bundled accessories. Pricing can change over time, so checking the official store or authorized distributors before purchasing is recommended.
Compared with other hardware wallets, Coldcard’s price is roughly similar to devices like the Ledger Nano X and slightly lower than premium wallets such as the Trezor Model T.
The device price generally includes the hardware wallet itself and basic packaging materials. Additional accessories, such as microSD cards or steel backup plates, are usually purchased separately.
What You May Need To Budget Beyond The Device
Although the Coldcard wallet itself is relatively affordable, many users invest in additional tools to strengthen their backup and recovery strategy.
A microSD card is one of the most useful accessories because it enables air-gapped transaction workflows and encrypted wallet backups.
Many users also purchase steel seed backup plates to protect their recovery phrases against fire or physical damage. These metal backups are designed to withstand environmental hazards that would destroy paper backups.
Another possible cost involves secure storage solutions. Some users keep hardware wallets and backup materials inside safes or secure storage containers to reduce the risk of theft.
Advanced users running node-based setups may also invest in hardware for a personal Bitcoin node, which can improve privacy and transaction verification.
While these additions are optional, they often form part of a comprehensive self-custody setup.
Where To Buy Coldcard Safely
Because hardware wallets protect valuable assets, the purchasing process should be approached carefully.
The safest option is buying directly from the official Coldcard manufacturer, Coinkite, through its official store. Purchasing from the manufacturer reduces the risk of receiving a modified or tampered device.
Some authorized distributors also sell Coldcard devices, though buyers should verify that the seller is legitimate before placing an order.
Purchasing from random online marketplaces or unknown resellers introduces a higher risk of supply-chain manipulation. A malicious actor could potentially alter a device before shipping it to the buyer.
Ensuring the authenticity of the seller is therefore an important part of the security process.
Buying Tips And Security Warnings
After receiving the device, users should inspect the packaging carefully before beginning the setup process.
Coldcard wallets typically ship inside tamper-evident packaging designed to show whether the device has been opened or altered. If the packaging appears damaged or resealed, it is best to pause setup and contact the seller.
Users should also avoid using devices that appear preconfigured. A legitimate hardware wallet should always generate a new seed phrase during the first setup process.
Resetting the device and generating a new wallet is a good precaution if there is any uncertainty about the device’s history.
Following these simple purchasing precautions helps ensure that the hardware wallet begins its life in a secure state.
Hardware wallets are often marketed as ultimate security tools, but no device is perfect. Every wallet design involves trade-offs between usability, flexibility, and security discipline.
Coldcard’s focus on Bitcoin-only custody and air-gapped transaction workflows provides strong security advantages. At the same time, those same design decisions introduce complexity and limitations that users should understand before choosing the device.
Recognizing these trade-offs makes the review more realistic and helps readers determine whether Coldcard aligns with their own needs and technical comfort level.
Common Problems, Trade-Offs, And Limitations
Recognizing Coldcard Limitations Before Choosing A Hardware Wallet
Coldcard offers powerful security features, but its design assumes users are willing to learn operational security practices. That expectation can create friction for newcomers who are accustomed to simple mobile wallets or exchange accounts.
The following limitations represent the most common challenges users encounter when adopting the Coldcard ecosystem.
Why Coldcard Can Feel Difficult For Beginners
Coldcard’s setup process includes several steps that may be unfamiliar to first-time hardware wallet users. Concepts such as seed phrase management, PSBT transaction files, and microSD-based workflows require careful attention.
Unlike some consumer wallets that guide users through simplified mobile interfaces, Coldcard expects users to understand the fundamentals of Bitcoin custody. Navigating the device menus, exporting wallet data, and pairing with external wallet software may take time to learn.
For users who approach Bitcoin storage with patience and curiosity, the learning curve eventually becomes manageable. However, beginners seeking an extremely simple onboarding process may find other hardware wallets easier to start with.
The Downsides Of Bitcoin-Only Support
Coldcard’s Bitcoin-only philosophy simplifies the device’s security architecture, but it also limits flexibility.
Many cryptocurrency investors hold multiple assets such as Ethereum, tokens, or NFTs. Because Coldcard supports only Bitcoin, users must rely on additional wallets to manage those assets.
For Bitcoin maximalists, this limitation is often seen as a strength. For diversified investors, it may feel restrictive.
No Mobile-First Simplicity
Modern hardware wallets increasingly integrate with mobile applications, allowing users to manage assets from their smartphones. Coldcard does not follow this model.
Instead, the wallet relies heavily on desktop wallet integrations and microSD transaction transfers. While this approach enhances isolation from internet-connected systems, it reduces the convenience many users expect from modern crypto tools.
People who frequently move funds or manage assets on mobile devices may find this workflow slower than alternatives that provide dedicated mobile apps.
When The Security Features Become Overkill
Coldcard’s security model is extremely robust, but some users may find its advanced features unnecessary.
For someone storing a small amount of Bitcoin, complex workflows such as air-gapped PSBT signing or multisignature coordination may feel excessive. Simpler wallets can often provide adequate protection for smaller holdings.
Coldcard tends to make the most sense for users who treat Bitcoin storage as a long-term security responsibility rather than a casual investment tool.
Common User Errors That Matter More Than Device Specs
Even the strongest hardware wallet cannot compensate for poor operational security.
Many Bitcoin losses occur not because of device vulnerabilities but because of mistakes in backup management. Losing a seed phrase, storing it digitally, or exposing it to unauthorized access can compromise funds regardless of the wallet used.
Passphrase management introduces additional risk as well. Forgetting a passphrase effectively locks the user out of the associated wallet permanently.
Coldcard provides powerful security tools, but their effectiveness ultimately depends on the user’s discipline and understanding.
After examining Coldcard’s architecture, features, workflows, and trade-offs, the final step is answering the most important question: Is this the right hardware wallet for you?
Coldcard clearly targets a specific audience. Its design prioritizes security discipline and Bitcoin-focused custody rather than convenience or multi-asset flexibility. For some users, this makes it one of the most powerful hardware wallets available. For others, it may introduce unnecessary complexity.
Evaluating the wallet through the lens of user profiles helps clarify when Coldcard makes sense and when another device might be a better fit.

 Coldcard Focuses On Bitcoin-Only Security And Sovereign Self-Custody. Image via
Coldcard Focuses On Bitcoin-Only Security And Sovereign Self-Custody. Image via 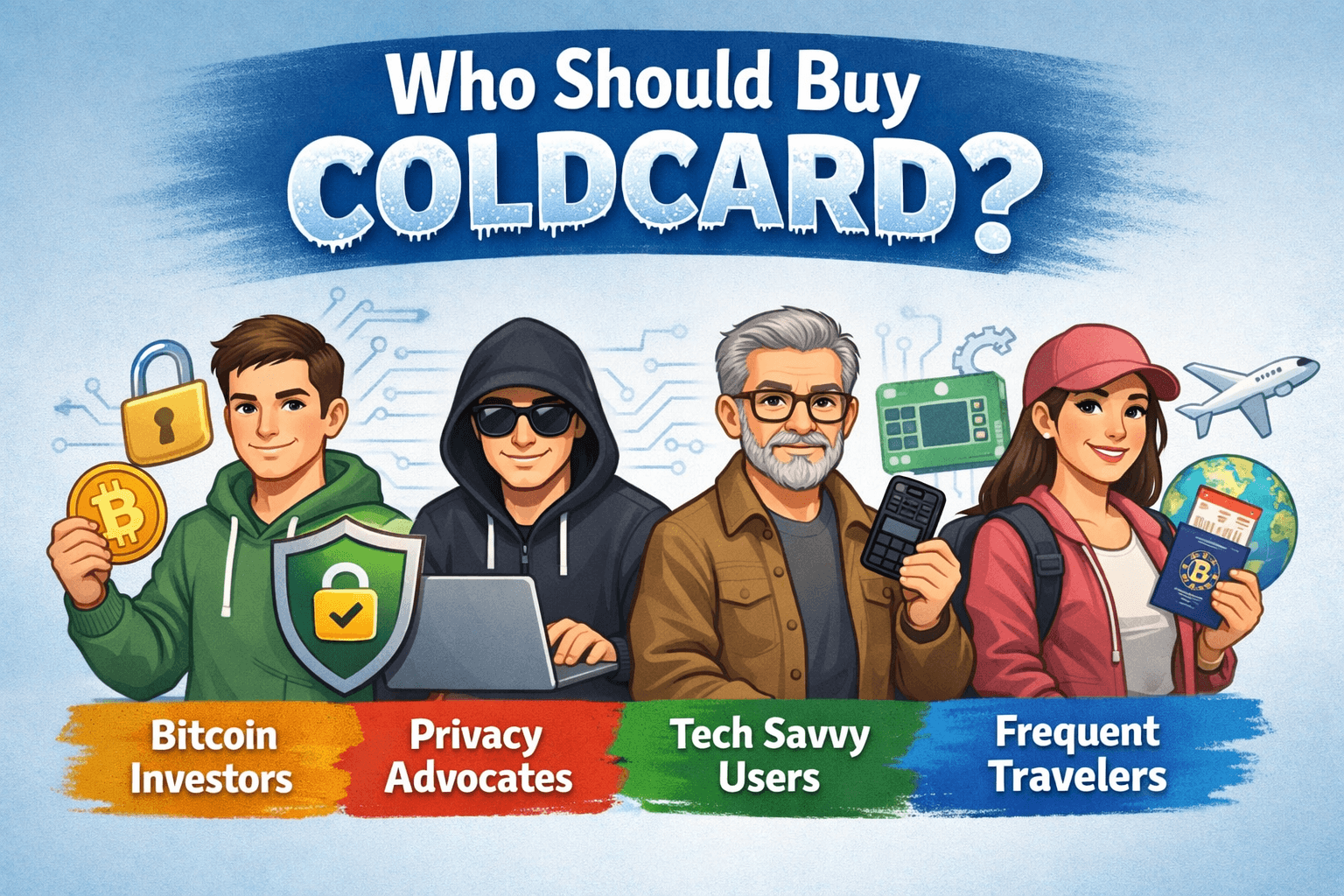 Understanding Which Bitcoin Users Benefit Most From Coldcard
Understanding Which Bitcoin Users Benefit Most From Coldcard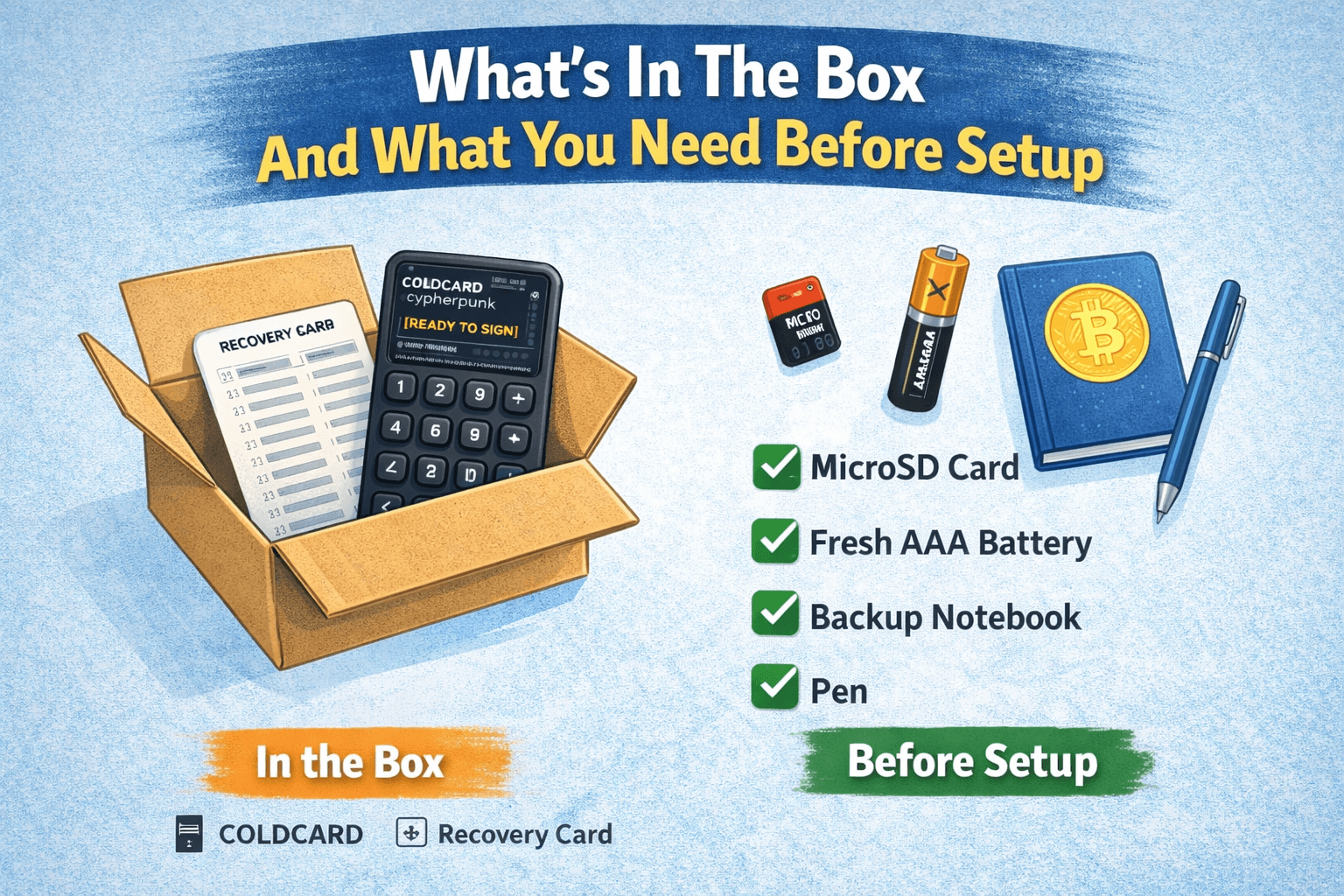 Essential Items And Preparation Required Before Setting Up Coldcard
Essential Items And Preparation Required Before Setting Up Coldcard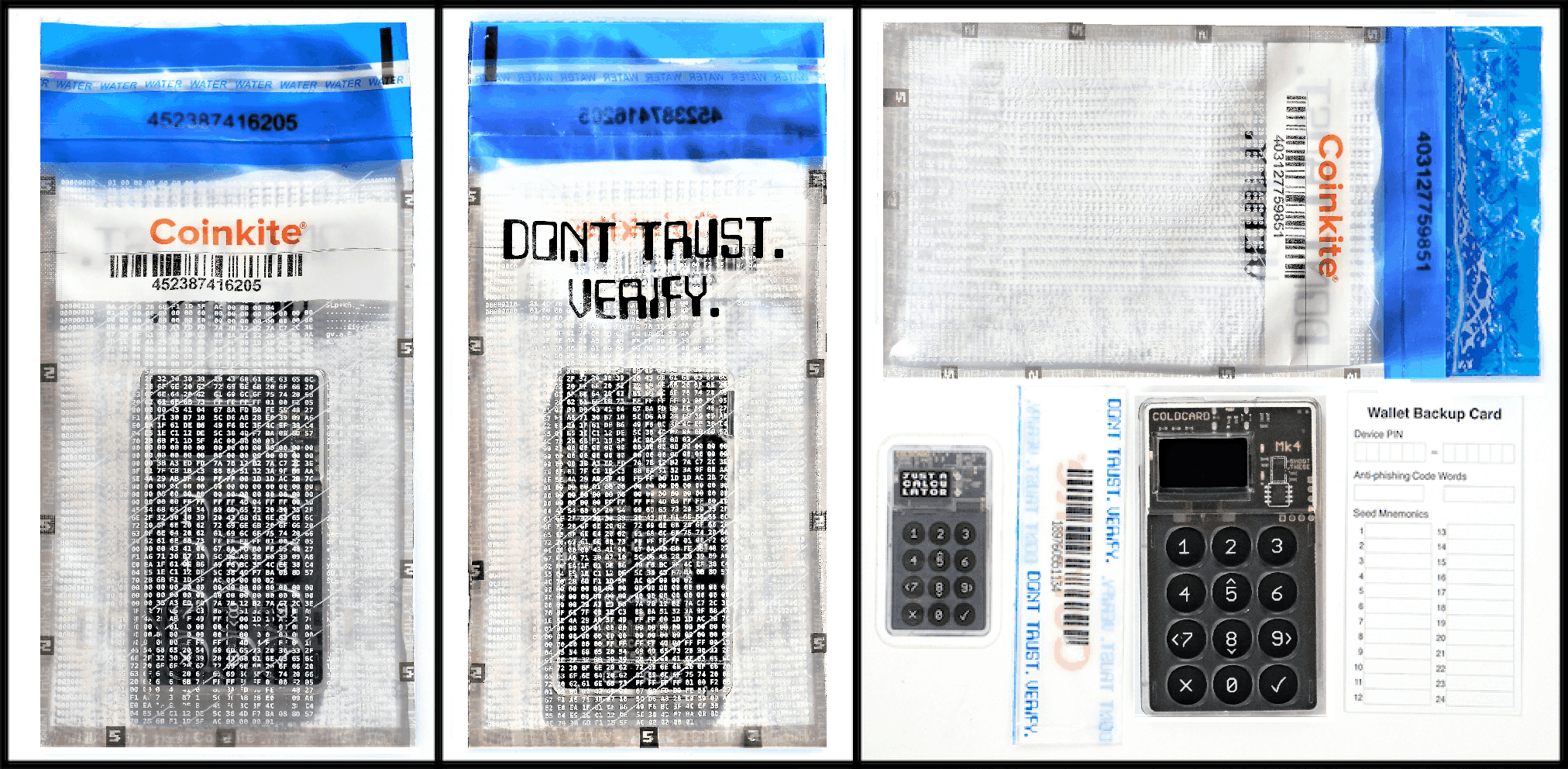 Verify The Device And Packaging of Coldcard. Image via
Verify The Device And Packaging of Coldcard. Image via 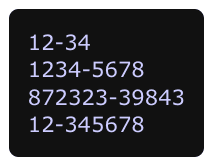 Create Your Pin. Image via
Create Your Pin. Image via 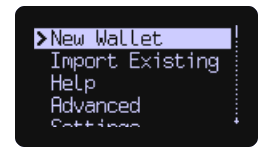 Setup Your New Wallet & Seed Phrase. Image via
Setup Your New Wallet & Seed Phrase. Image via 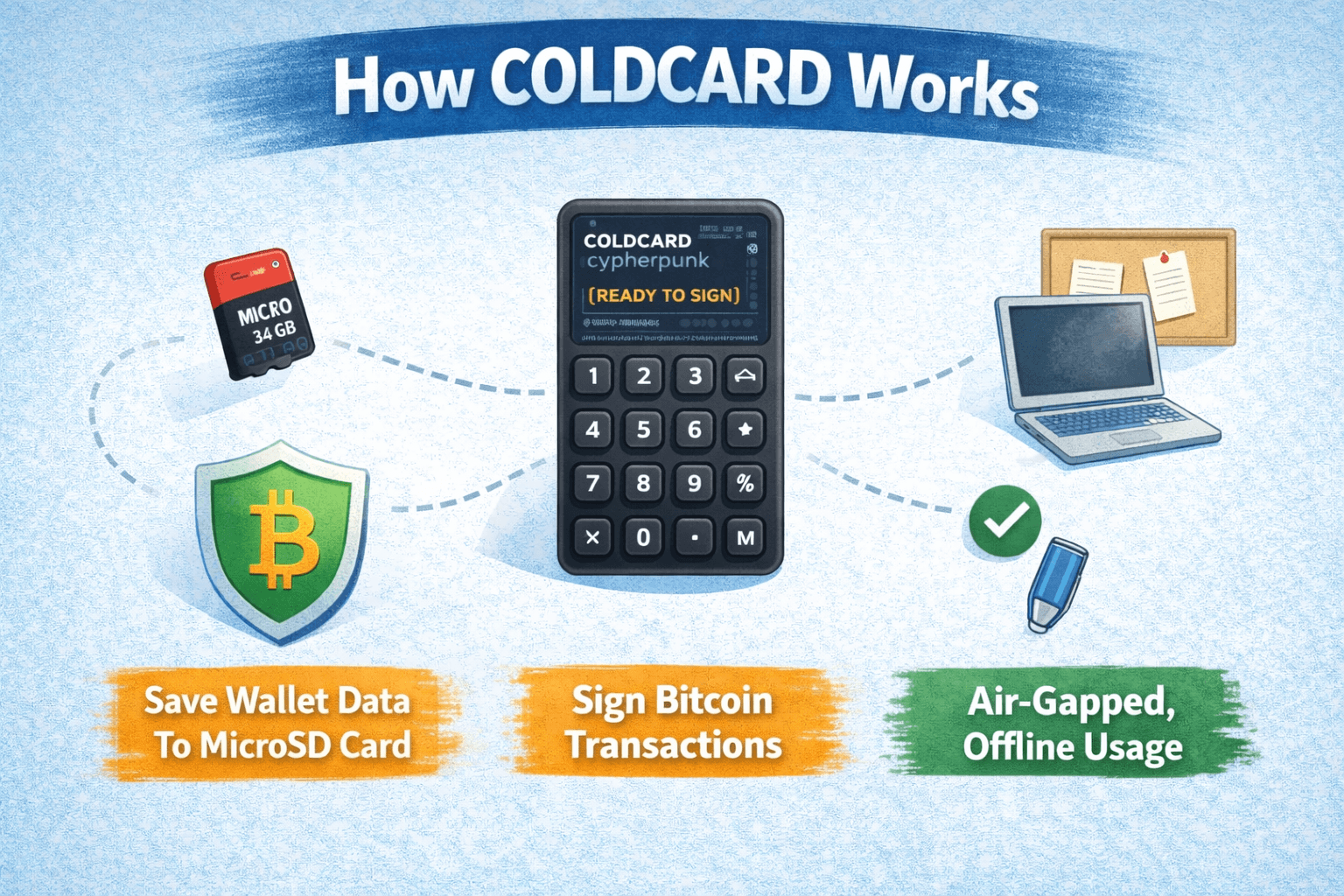 Understanding Coldcard Architecture And Offline Transaction Security Model
Understanding Coldcard Architecture And Offline Transaction Security Model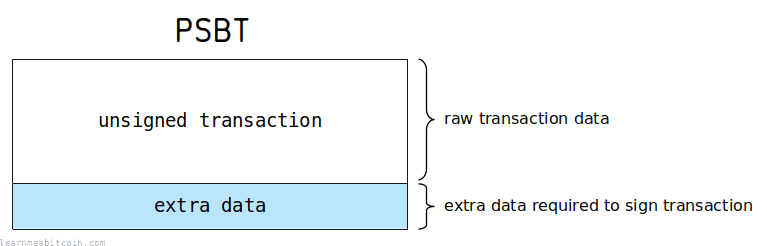 Partially Signed Bitcoin Transaction Format. Image via
Partially Signed Bitcoin Transaction Format. Image via 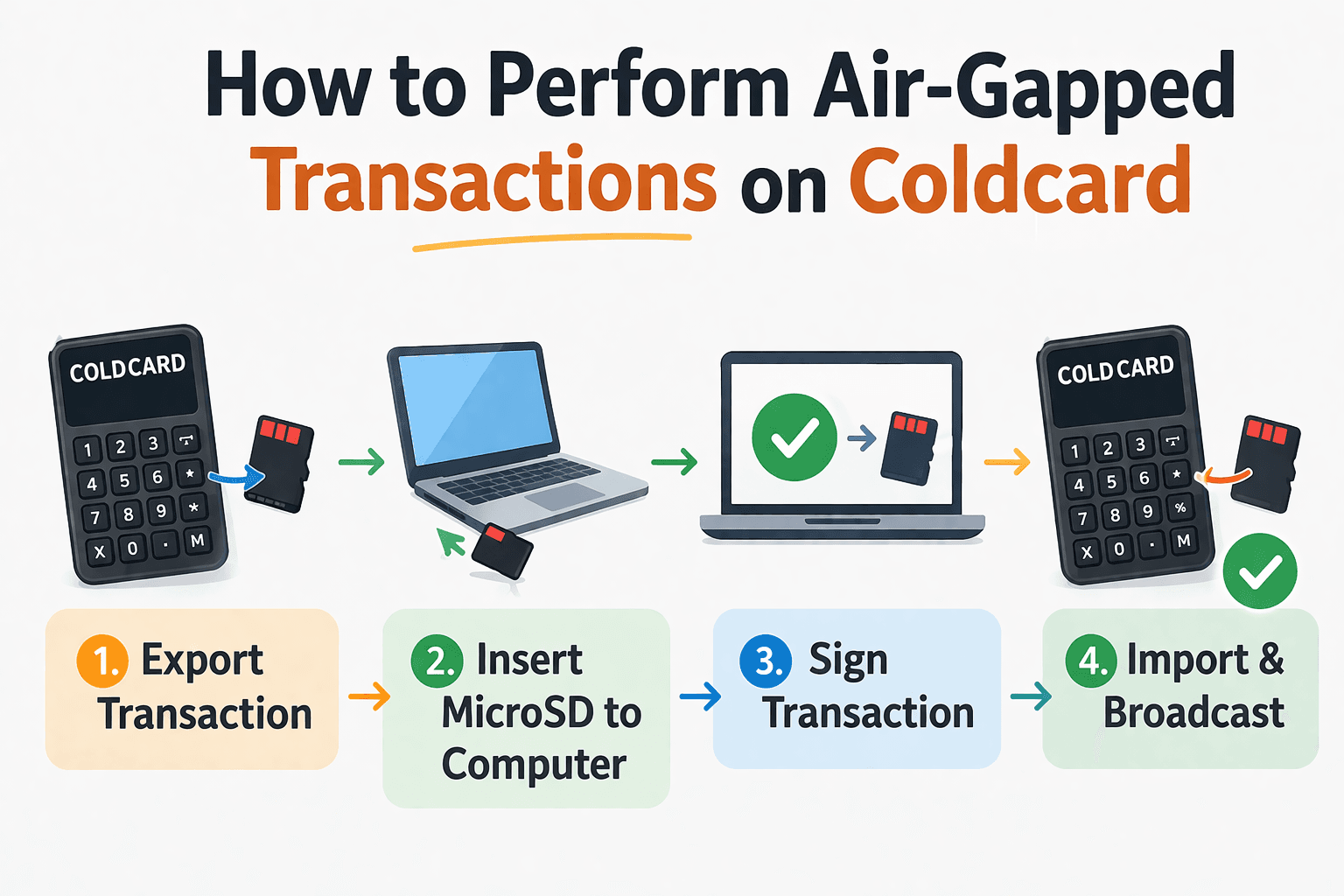 Air-Gapped Signing Workflow Protects Private Keys From Online Exposure
Air-Gapped Signing Workflow Protects Private Keys From Online Exposure Examining Coldcard’s Defensive Architecture And Real-World Security Strengths
Examining Coldcard’s Defensive Architecture And Real-World Security Strengths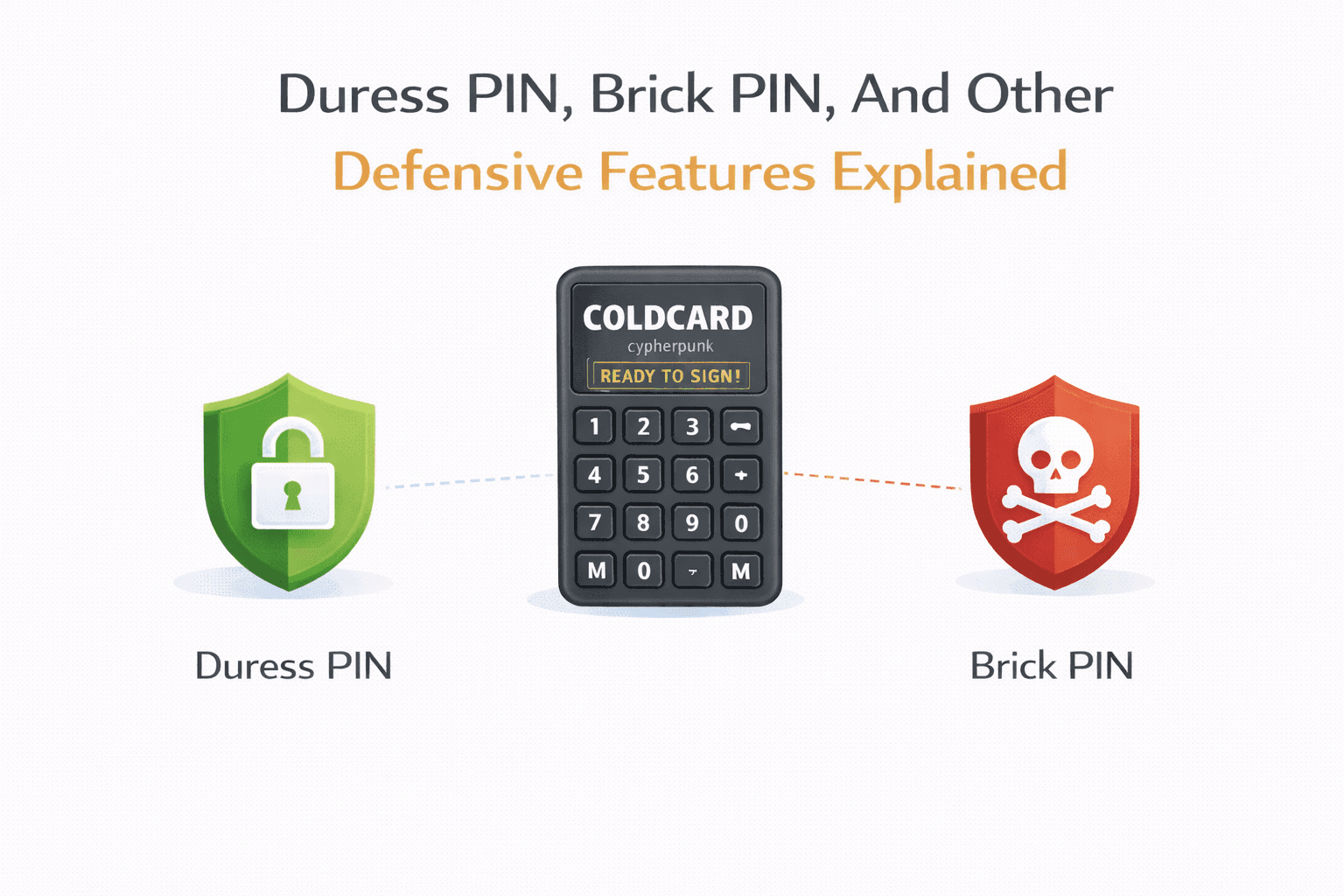 Coldcard Includes Emergency PIN Features Designed For Coercion Scenarios
Coldcard Includes Emergency PIN Features Designed For Coercion Scenarios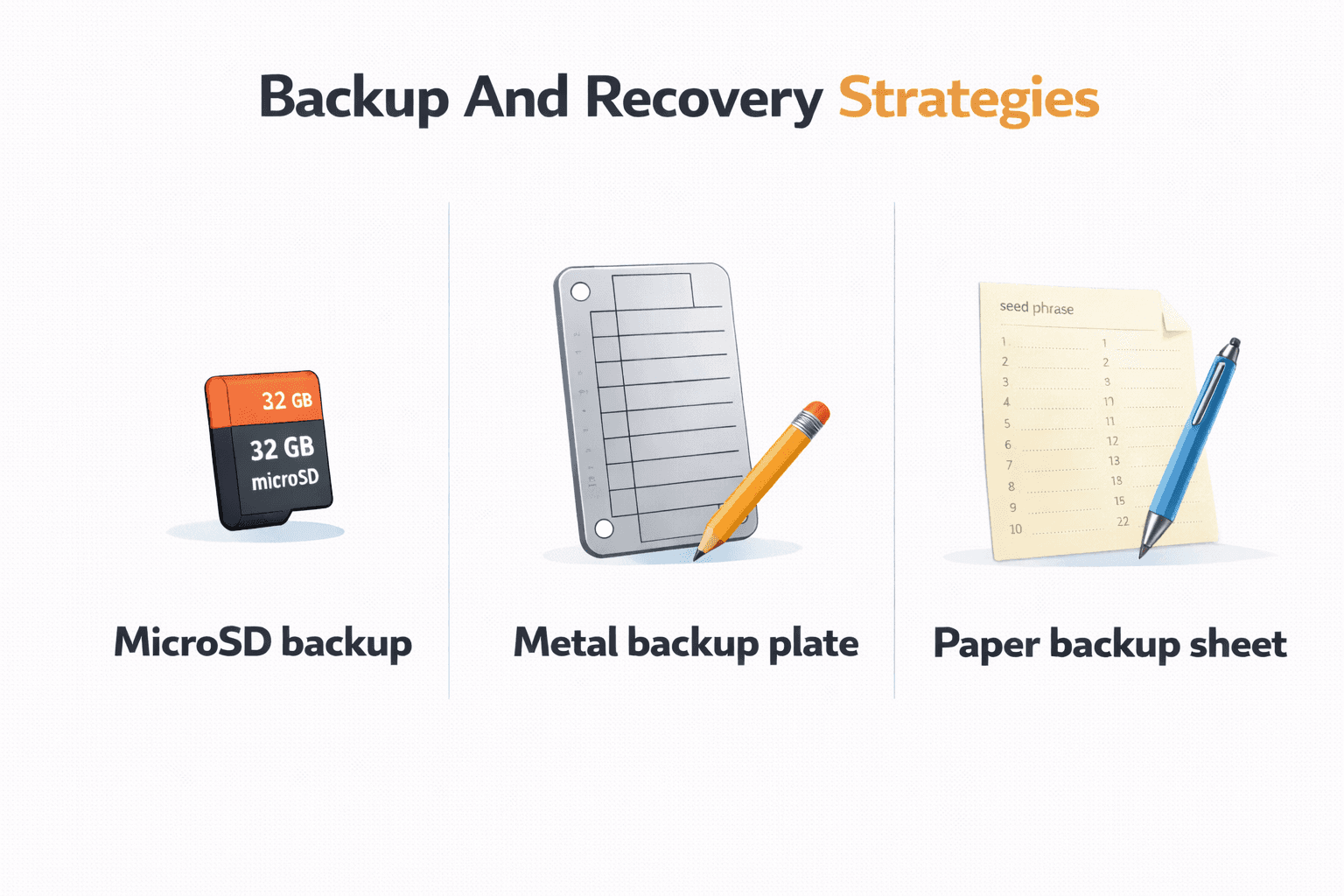 Protecting Bitcoin Access Through Secure Redundant Backup And Recovery Methods
Protecting Bitcoin Access Through Secure Redundant Backup And Recovery Methods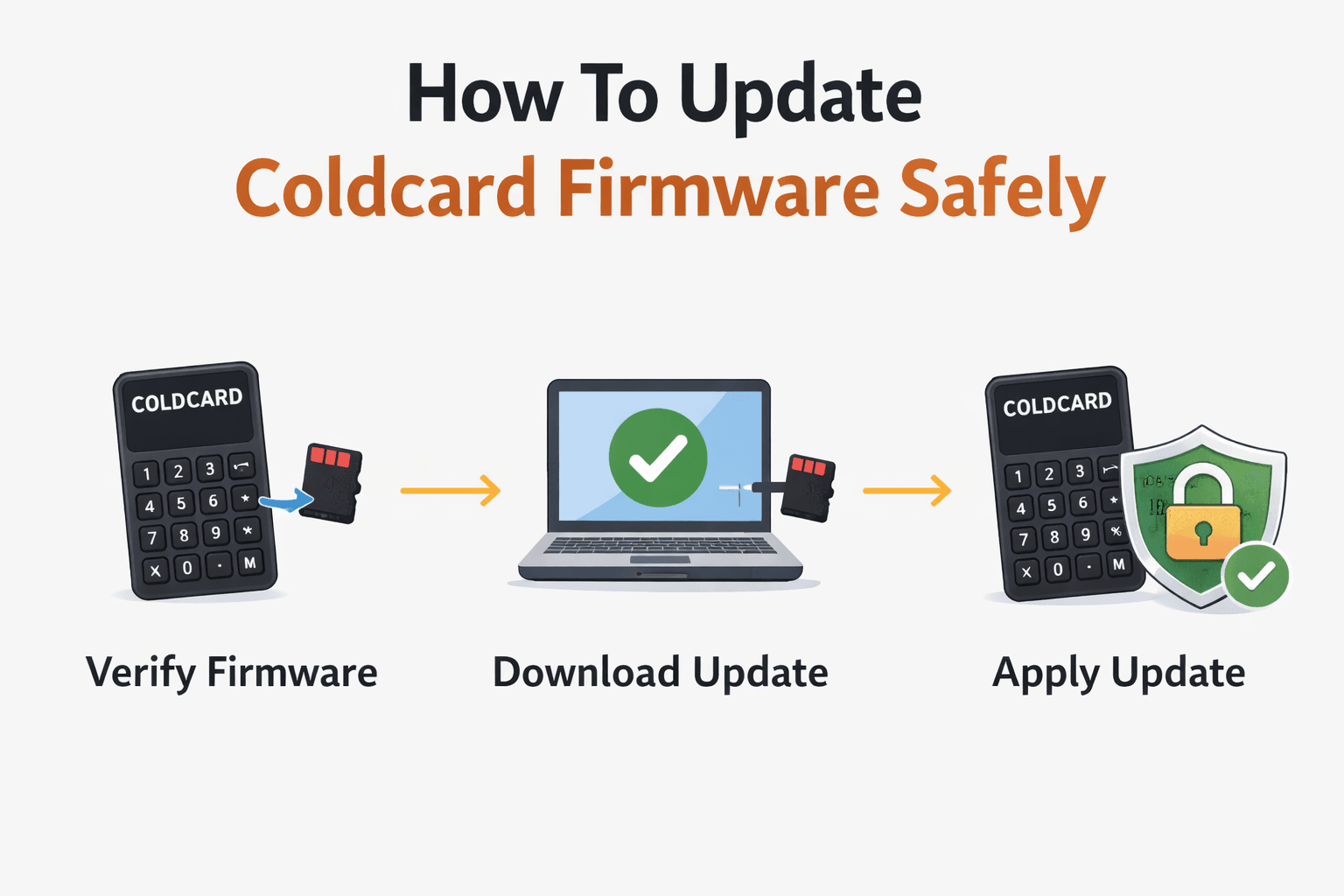 Understanding Coldcard Pricing And Secure Purchasing Considerations
Understanding Coldcard Pricing And Secure Purchasing Considerations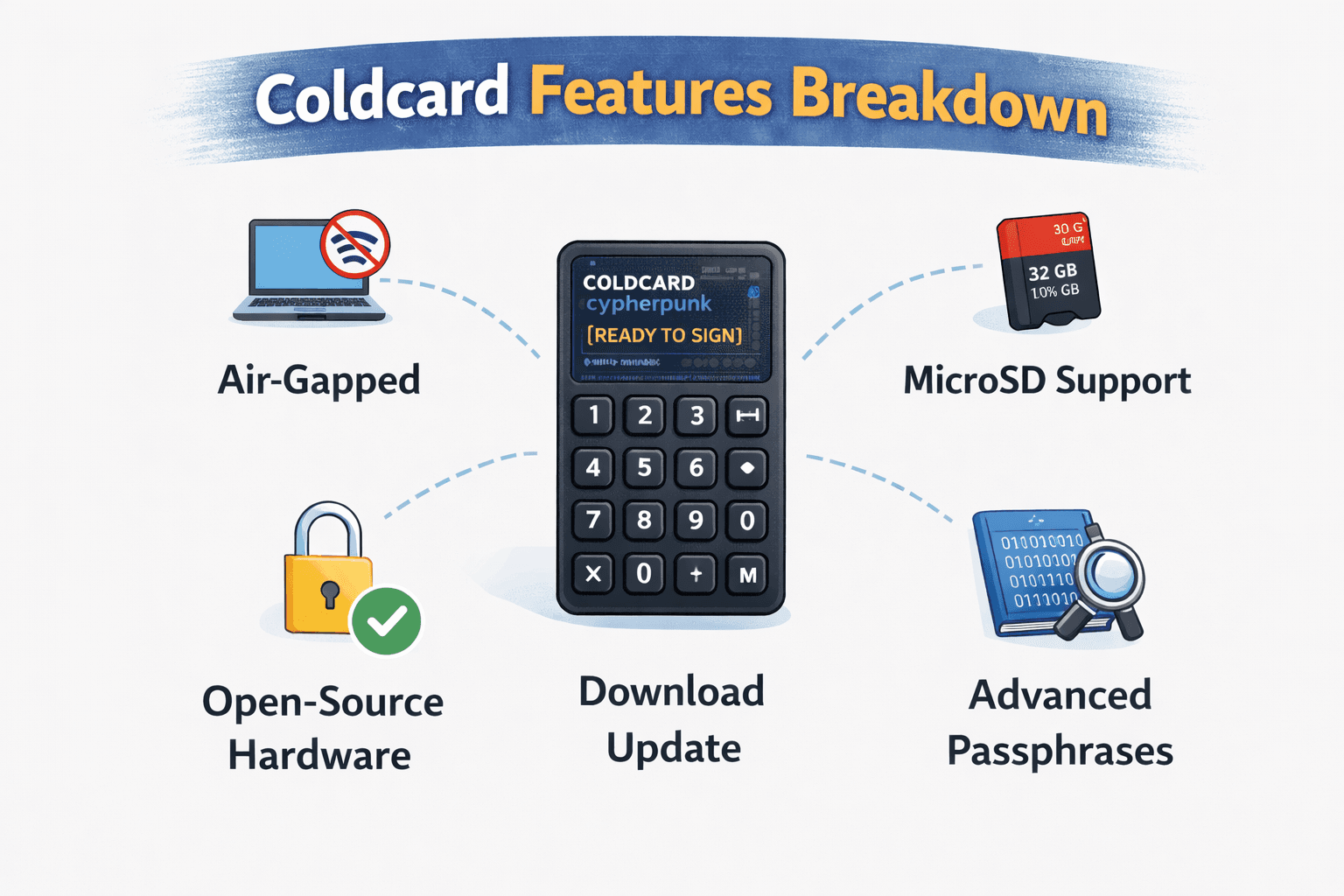 Key Coldcard Features That Enable Advanced Bitcoin Self-Custody
Key Coldcard Features That Enable Advanced Bitcoin Self-Custody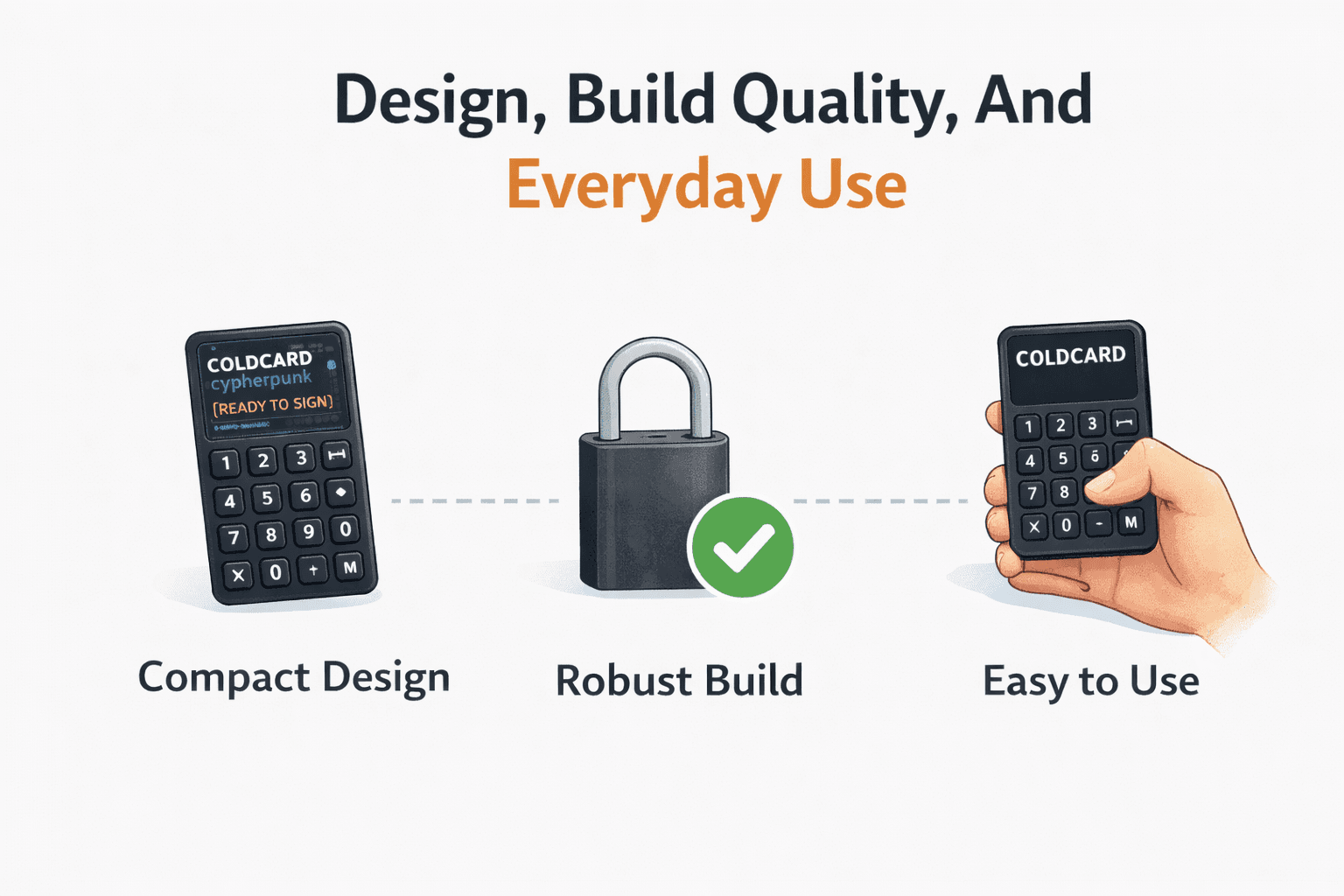 Evaluating Coldcard Hardware Design And Real-World Usability Experience
Evaluating Coldcard Hardware Design And Real-World Usability Experience 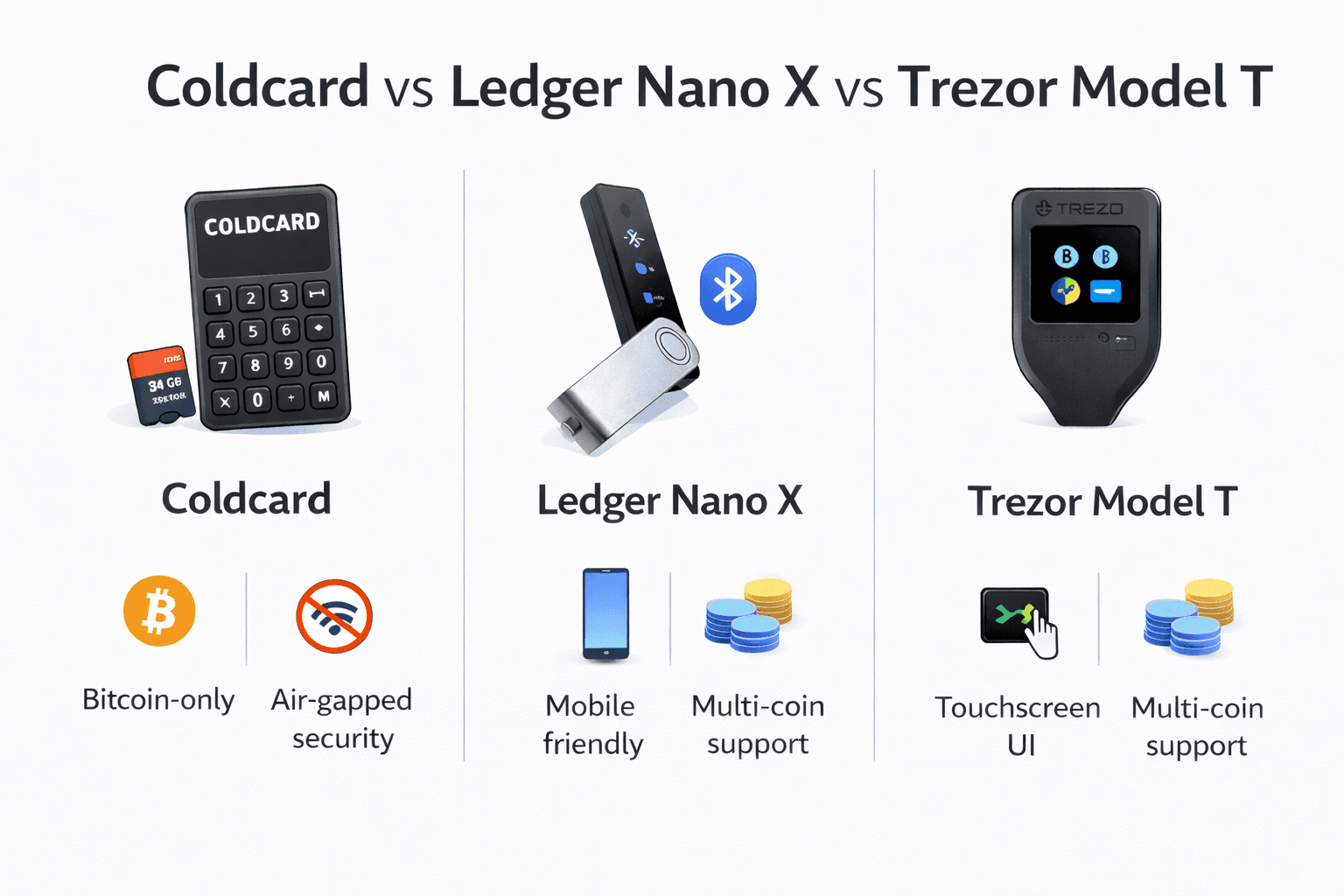
 How Coldcard Compares With Leading Bitcoin-Only Hardware Wallets
How Coldcard Compares With Leading Bitcoin-Only Hardware Wallets Understanding Coldcard Pricing And Secure Purchasing Considerations
Understanding Coldcard Pricing And Secure Purchasing Considerations Recognizing Coldcard Limitations Before Choosing A Hardware Wallet
Recognizing Coldcard Limitations Before Choosing A Hardware Wallet



