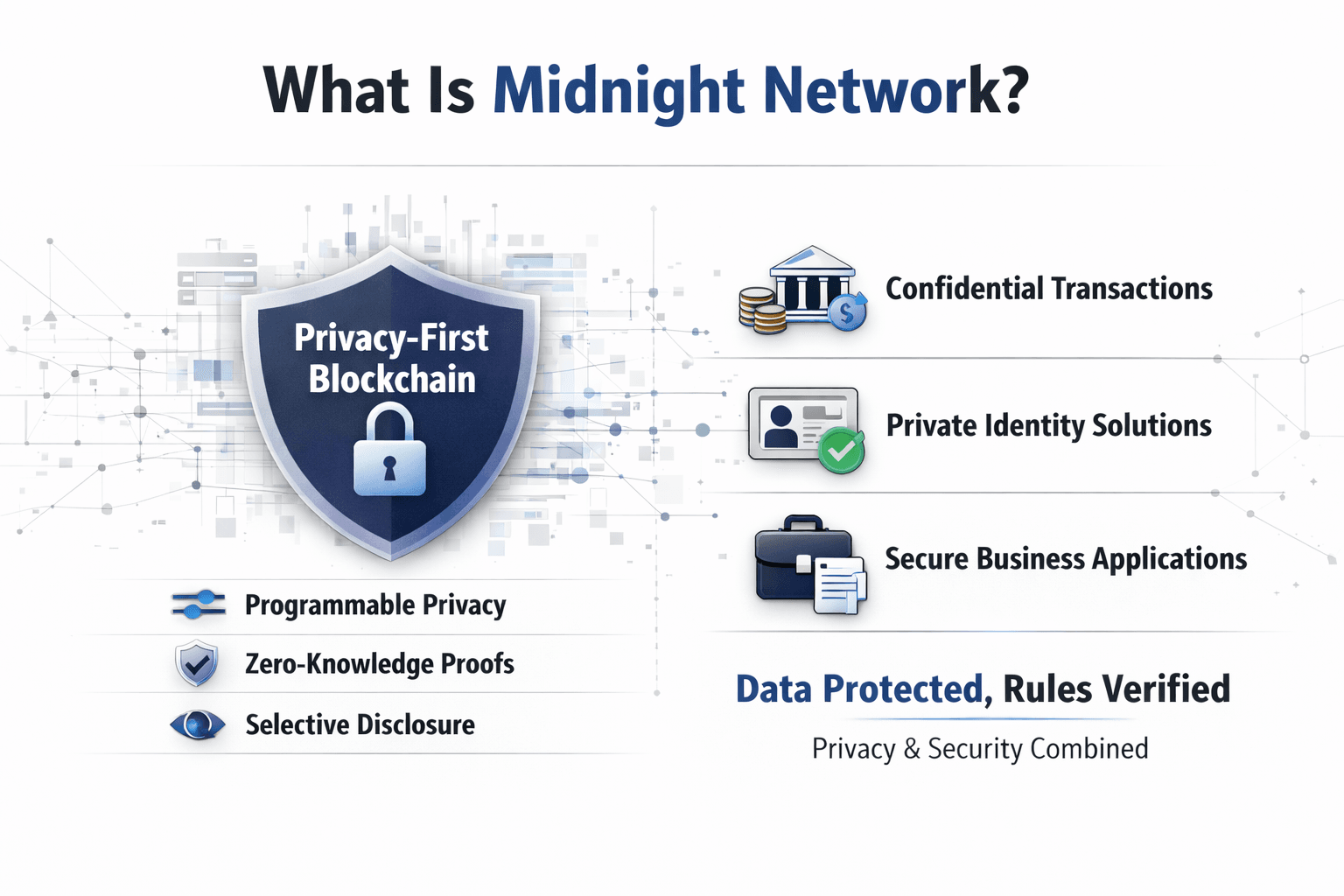
Midnight Network is a fourth-generation privacy-focused blockchain and the first partner chain connected to the Cardano ecosystem. It combines zero-knowledge proofs, a dual-ledger architecture, and selective disclosure so applications can keep sensitive data confidential without giving up verification.
- Privacy-first design: Midnight is built for applications that need confidentiality and verifiability at the same time, rather than forcing everything into public view.
- Mainnet is now live: Midnight launched its mainnet in March 2026, moving the project from rollout preparation into live network operation.
- Programmable privacy model: Developers can choose what stays private, what becomes visible, and what can be proven without revealing the underlying data.
- Dual-ledger architecture: Midnight separates public coordination from shielded state, allowing confidential execution alongside visible network activity where needed.
- NIGHT and DUST system: NIGHT is the fixed-supply native token, while DUST acts as the renewable resource used for network activity and more predictable usage costs.
- Built for compliance-ready use cases: Midnight is designed for areas like confidential DeFi, identity, enterprise workflows, and regulated applications where selective disclosure matters.
What Is Midnight Network?
Midnight Network is a privacy-first blockchain designed for applications that need data confidentiality without giving up verification. It combines programmable privacy, zero-knowledge proofs, and selective disclosure so sensitive information can stay protected while the network still proves that rules were followed.
 A Privacy-First Network Built For Verifiable Applications
A Privacy-First Network Built For Verifiable ApplicationsMidnight Network is built for a part of crypto that public chains still handle badly: applications that need to keep sensitive data private while remaining verifiable on-chain. A normal public blockchain exposes too much by default, which makes it awkward for financial activity, identity-based systems, and business workflows where confidentiality matters. Midnight changes that by giving developers a way to protect data inside the application itself instead of pushing everything into public view.
That design rests on programmable privacy. Developers can decide what stays private, what becomes visible, and what can be proven without revealing the raw data underneath. Zero-knowledge proofs handle verification, while selective disclosure allows an application to reveal only the part that actually needs to be shown.
Taken together, that makes Midnight closer to application infrastructure than a narrow privacy asset. It is built for systems that require trust, auditability, and confidentiality simultaneously.
Why Midnight Exists
A public blockchain works well when transparency is the point, because an open state makes verification easy. The problem is that the same model creates data exposure by default, and that becomes a serious limitation once blockchain moves into sensitive business, financial, identity, and institutional workflows.
Midnight’s thesis is that privacy should be a protocol primitive, not an add-on. In other words, privacy by design has to sit inside the network itself if blockchain wants to support compliance-heavy and enterprise blockchain use cases without leaking too much information along the way.
The Cardano Connection
Midnight is aligned with Cardano, but architected as its own network and economic system. It is positioned as the first partner chain connected to the Cardano ecosystem, with Input Output, also known as IOHK, involved in its development and rollout.
So, is Midnight a Cardano sidechain? The cleaner answer is no in the simple sense people usually mean. It shares strategic alignment with Cardano and draws from that ecosystem, but it runs as its own network with its own architecture, privacy model, and economic system.
The Core Idea Behind Midnight: Rational Privacy
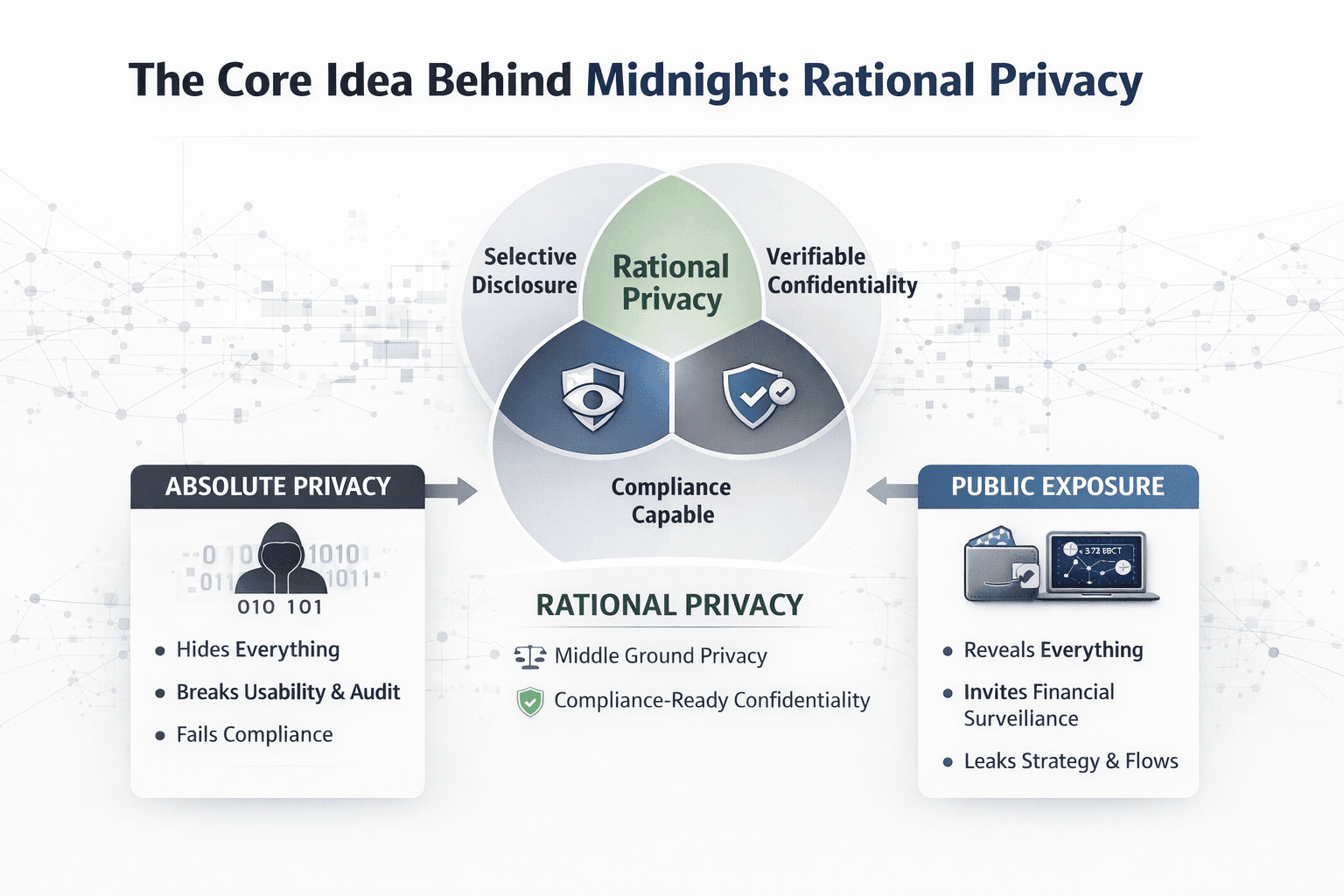
Midnight’s main idea is rational privacy: keep sensitive data private by default, make disclosure selective, and preserve enough verifiability for real applications to operate in regulated environments. It sits between total exposure and total opacity, and that middle ground is where Midnight tries to make privacy usable rather than absolute.
 Midnight’s Approach To Controlled Privacy And Disclosure
Midnight’s Approach To Controlled Privacy And DisclosureThe Privacy Problem Public Chains Create
On most public chains, wallet balances, transaction flows, and contract interactions are visible by design. That level of on-chain transparency helps with trust, but it also turns transaction visibility into a weakness when the activity involves market strategy, private capital flows, or business logic that should not be exposed in real time.
The effects are practical. Financial surveillance becomes easier, strategy leakage becomes more likely, institutions grow more reluctant to use public infrastructure, and MEV thrives when pending activity can be analyzed and exploited. What works for open verification often works against confidentiality.
Rational Privacy vs Absolute Privacy
Rational privacy does not mean hiding everything from everyone. It means privacy that is selective, purposeful, and usable in systems that still need policy checks, oversight, and controlled disclosure. That is why Midnight frames privacy as something that can be programmed into the application, instead of treating secrecy as an all-or-nothing condition.
In practice, this means a user or application can prove a fact without exposing the full record behind it. That is what makes selective disclosure useful and what gives Midnight its idea of compliance-ready privacy. The goal is programmable confidentiality that protects sensitive information while still letting the system function inside regulated environments.
The Privacy Trilemma
Midnight’s privacy trilemma is the effort to hold three things together at once: privacy, programmability, and compliance. Many systems can deliver one or two of those qualities, but start to strain when asked to support all three. Private systems often narrow what developers can build, while highly programmable systems usually default to full exposure.
The network claims that its architecture can support all three simultaneously. Privacy protects the data, programmability gives developers room to build useful applications, and compliance remains possible because disclosure can be selective rather than total. That is the design ambition behind the network, and it is also what separates Midnight from simpler privacy models that only solve for concealment.
How Midnight Network Works
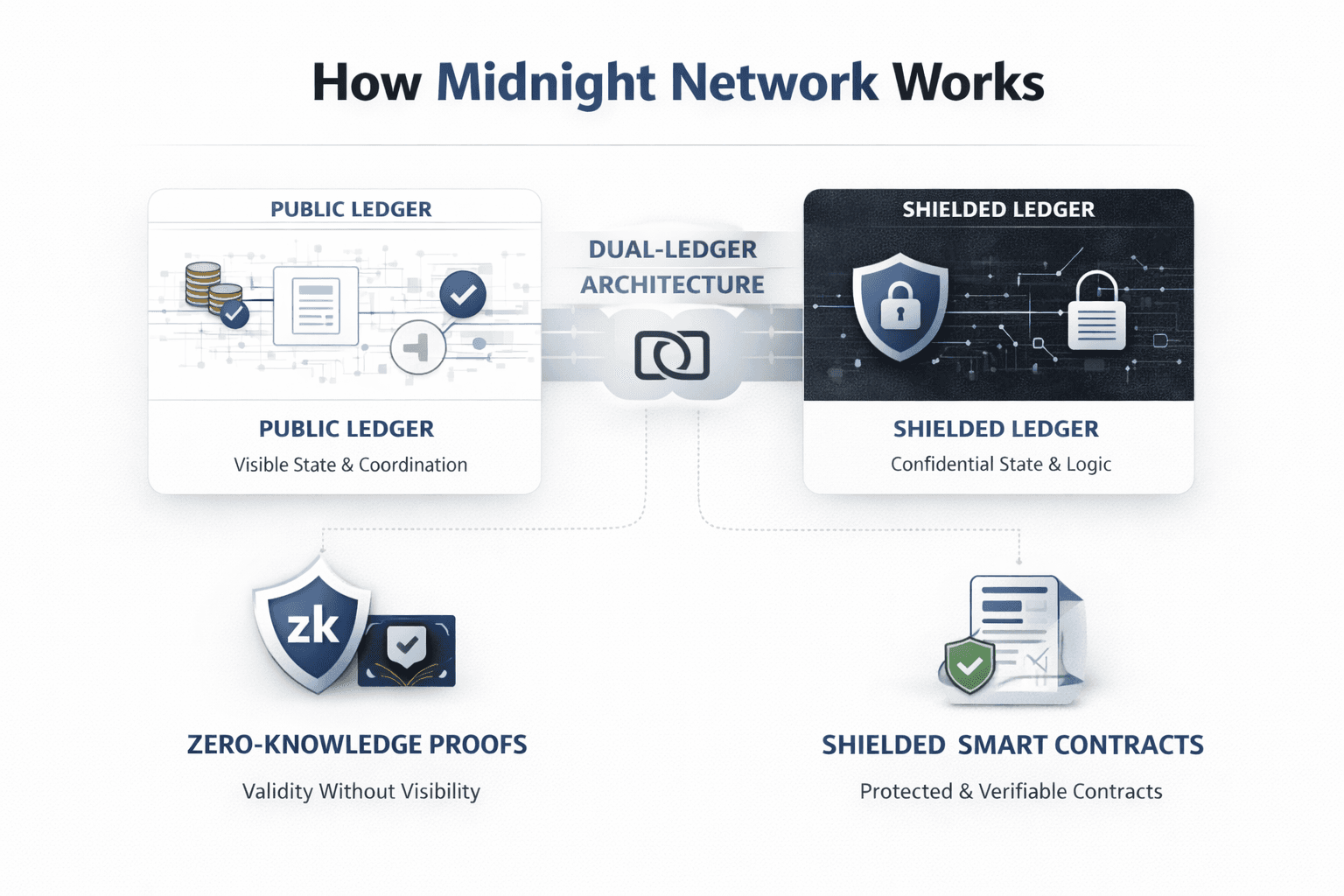
Midnight works through a design that separates public coordination from confidential execution. Its architecture combines a dual-ledger architecture with zero-knowledge proofs so applications can keep sensitive state private while still proving that transactions and contract logic followed the rules. Midnight’s own overview frames this as programmable privacy supported by a system that preserves utility, predictable operation, and developer usability.
 A Working System For Confidential State And Verification
A Working System For Confidential State And VerificationDual-Ledger Architecture
At the core of the Midnight protocol is a public ledger and a shielded ledger working together. The public ledger handles visible state, coordination, and the parts of network activity that need shared ordering or confirmation. The shielded ledger handles confidential state, where sensitive data and protected application logic can exist without being exposed to everyone by default.
The point of that split is clarity, not complexity. Midnight is not trying to bolt privacy onto a fully transparent base after the fact. It gives developers a system where public coordination can remain visible, while confidential state stays protected inside the application flow. That is what allows the network to keep verifiability without forcing every useful piece of data into public view.
Zero-Knowledge Proofs in Midnight
ZK proofs are what let Midnight verify correctness without revealing raw data. The useful way to understand them here is simple: the network does not need to see the underlying information if it can verify that the rules were satisfied. That makes zero-knowledge proofs less about abstract cryptography and more about rule-following without disclosure.
This is why Midnight’s model can be described as validity without visibility. A transaction, state transition, or contract action can be checked against protocol rules, and the network can confirm it is valid, while the sensitive inputs remain hidden. That is the basis for confidential execution on Midnight.
Shielded Smart Contracts
Midnight uses shielded smart contracts so applications can work with private state while still running on-chain. That creates a clear difference from Ethereum-style public smart contracts, where contract logic is verifiable but the state and interactions are usually visible to anyone watching the chain.
This matters because Midnight is built for programmable privacy, not only for private transfers. The network is meant to support Midnight dApps whose logic depends on confidentiality, whether that involves financial state, protected credentials, or business workflows that should not leak through a fully public execution model.
Selective Disclosure
Selective disclosure is the part that makes Midnight’s privacy model usable in the real world. It allows a user or application to prove a limited fact without exposing the entire record behind it. That could mean proving a compliance threshold without revealing full financial records, proving creditworthiness to a lender without exposing complete salary history, or proving healthcare consent without exposing patient records.
That approach is what gives Midnight its compliance-ready edge. A tax authority, lender, or healthcare provider may need cryptographic proof that a condition was met, but they do not always need unrestricted access to the whole dataset. Midnight’s model creates room for an audit trail while still protecting the data that should remain private.
Compact and the Midnight Developer Stack
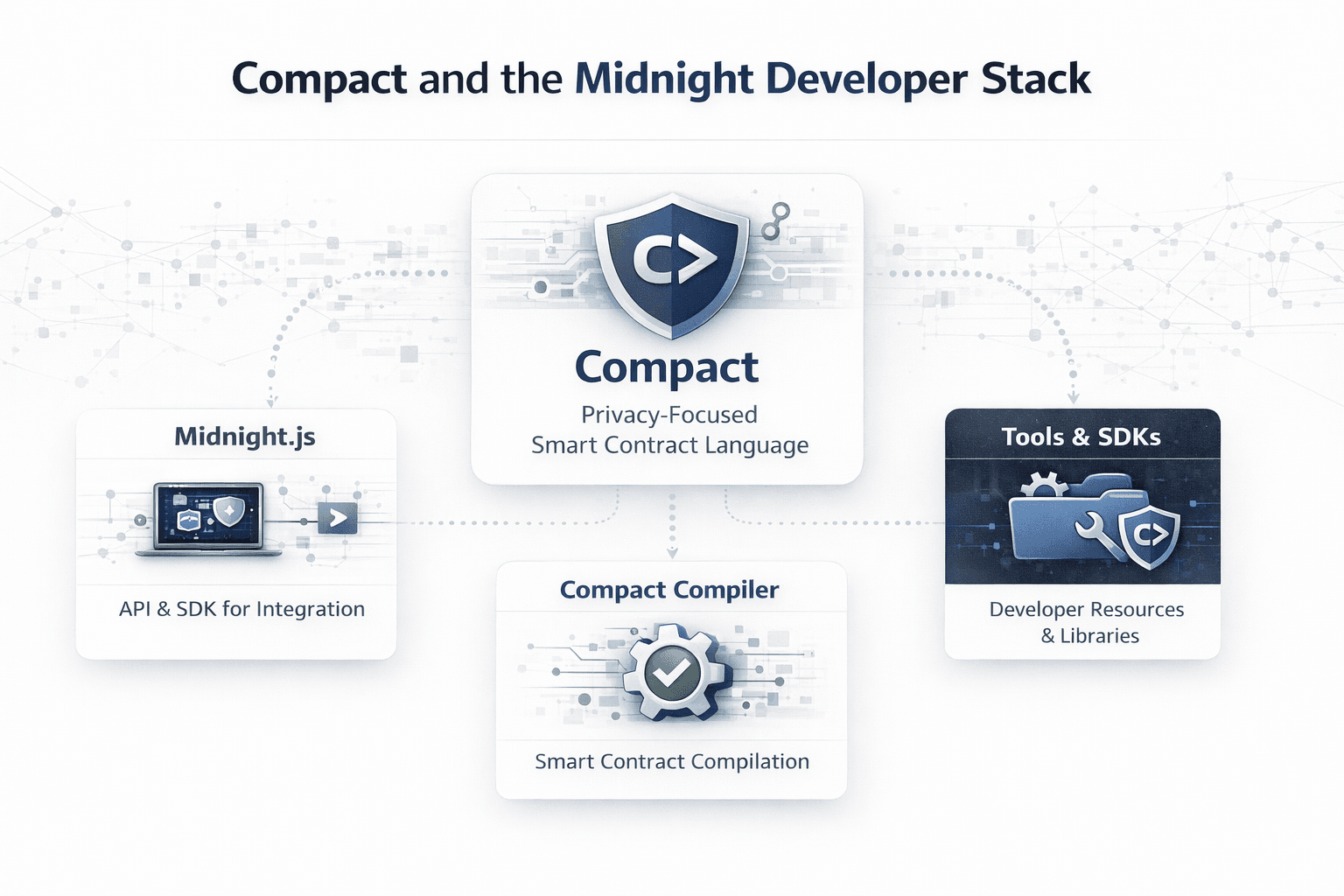
Midnight’s developer stack is built around the idea that privacy-preserving applications need their own tooling model, not a patched version of public-chain development. That is why the network uses Compact as a dedicated smart contract language, alongside practical tools that make confidential application logic easier to write, test, and deploy.
 Midnight’s Developer Language, Tooling, And Build Environment
Midnight’s Developer Language, Tooling, And Build EnvironmentWhat Compact Is
Compact is Midnight’s privacy-focused smart contract language. It is designed to work well with TypeScript tooling and developer workflows, but it should not be flattened into “TypeScript for Midnight,” because it is its own bounded smart contract language with a specific role inside the network’s execution model.
That distinction is important because Compact is built for privacy-preserving DApps from the ground up. Developers are not simply writing ordinary public smart contracts and then trying to wrap privacy around them later. They are working in a model where confidentiality is part of the application design itself, and Compact gives them a structured way to express that logic without dragging them into the weeds of proof engineering every step of the way.
Why Midnight Needed a New Language
Solidity and most conventional smart contract languages were built for environments where public state is the default. That may work well for transparent execution, but it does not map neatly onto ZK-compatible execution, where contracts may need to work across both private state and public state without blurring the line between them.`
Compact exists to make that boundary explicit and usable. It gives developers a way to define confidential logic clearly, while still allowing interaction with visible state where necessary. That is a meaningful shift, because once privacy becomes part of the contract model itself, developers can build applications where confidentiality is not a workaround but a native feature of how the system behaves.
Tooling Developers Actually Care About
Midnight’s tooling becomes more useful when it stays practical. Midnight.js gives developers a way to interact with the network from the application side, while the Compact compiler handles the contract layer and the translation needed for execution. Together, those tools are meant to reduce the amount of low-level complexity developers have to think about when building privacy-aware applications.
The rest of the stack follows the same logic. Preprod and test-network resources give teams a place to experiment before moving toward production, and the SDK and developer documentation are there to support actual building rather than theoretical exploration. That balance matters. Midnight is asking developers to work with a more privacy-aware model, so the tooling has to make that feel workable from the start.
NIGHT, DUST, and the Midnight Economic Model
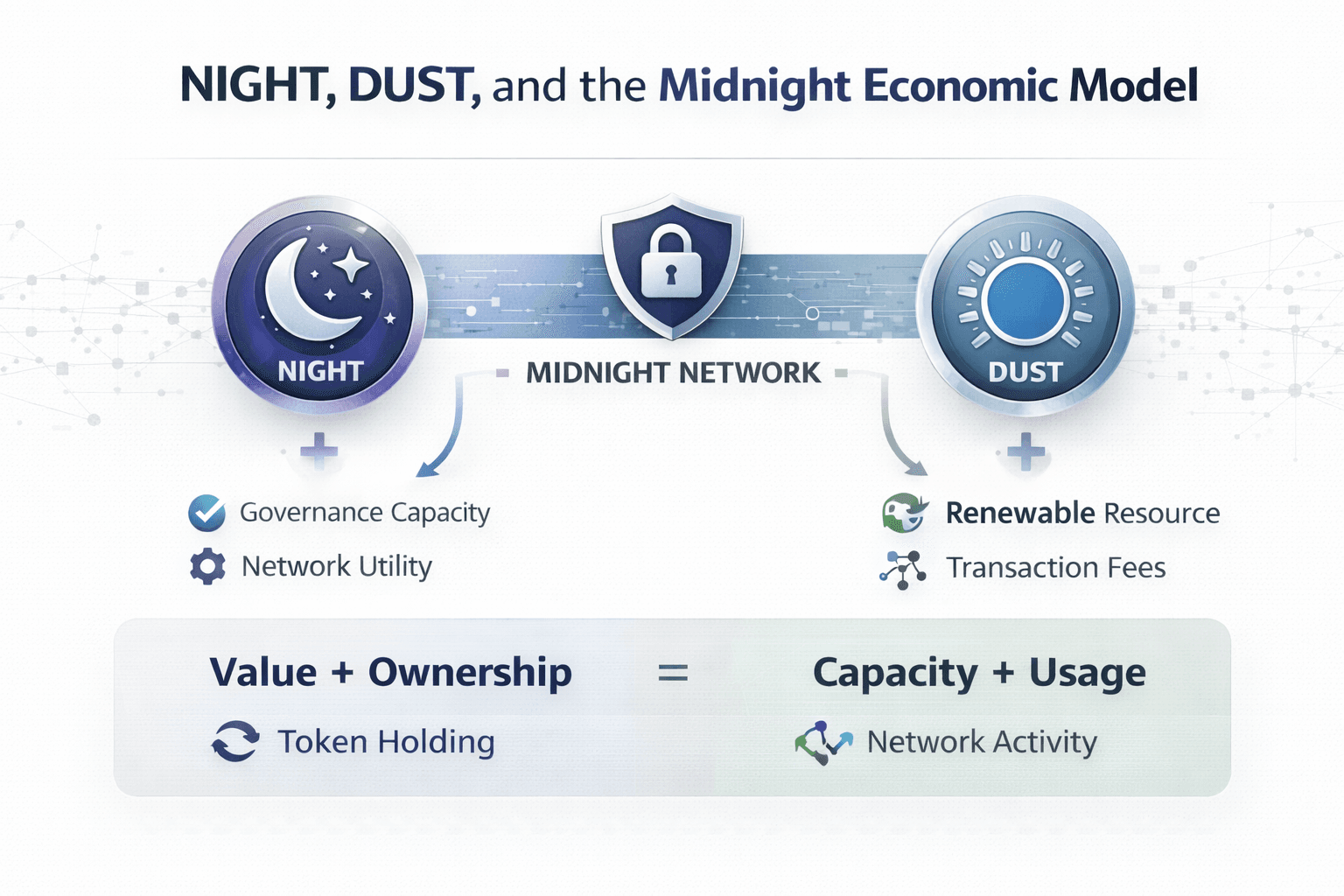
Midnight’s economic model separates value from usage. Instead of using one token for everything, it splits the system into NIGHT, which carries governance and utility functions, and DUST, which acts as the renewable resource used for network activity.
 Two Assets Shaping Midnight’s Usage And Cost Model
Two Assets Shaping Midnight’s Usage And Cost ModelWhat NIGHT Is
NIGHT is the unshielded native governance and utility token of the Midnight network, with a fixed supply of 24 billion. It went live in December 2025, and its role is broader than the usual gas-token model people associate with Ethereum-style networks.
The clean way to think about NIGHT is as the asset that anchors the network’s economic and governance layer. It is used for participation, coordination, and long-term utility, but it is not spent directly every time someone interacts with the chain. That distinction is important because Midnight deliberately avoids the simple model where the main token is constantly burned through day-to-day usage.
What DUST Is and Why It Matters
DUST is the renewable resource used for network activity on Midnight. It is generated by holding NIGHT, which means the system separates ownership of value from access to network capacity. That may sound like a small token-design choice, but it has big consequences for how the chain feels in practice.
Because DUST is the resource used for transaction fees and network usage, the cost of operating on Midnight becomes less tightly tied to the market price of the main token. That creates more predictable fees, which is a much better fit for budgeting, app design, and enterprise adoption. For businesses and developers, this is one of the more serious parts of Midnight’s design, because stable operating expectations matter far more than flashy token mechanics.
Why the NIGHT + DUST Model Is Strategically Important
The NIGHT and DUST model affects more than tokenomics. It changes how applications can onboard users, how costs can be planned, and how network capacity can be accessed without turning every interaction into a direct token-spending event.
That opens up room for better product design. Apps can think more clearly about sponsored usage, abstracted onboarding, and predictable cost flows. It also fits Midnight’s broader idea of cooperative economics, where the token-resource model is supposed to support practical network usage rather than forcing every participant through the same narrow economic path.
Readers thinking about the macro-market positioning can also see our take on the best cryptos to buy in 2026.
Glacier Drop, Scavenger Mine, and Token Distribution
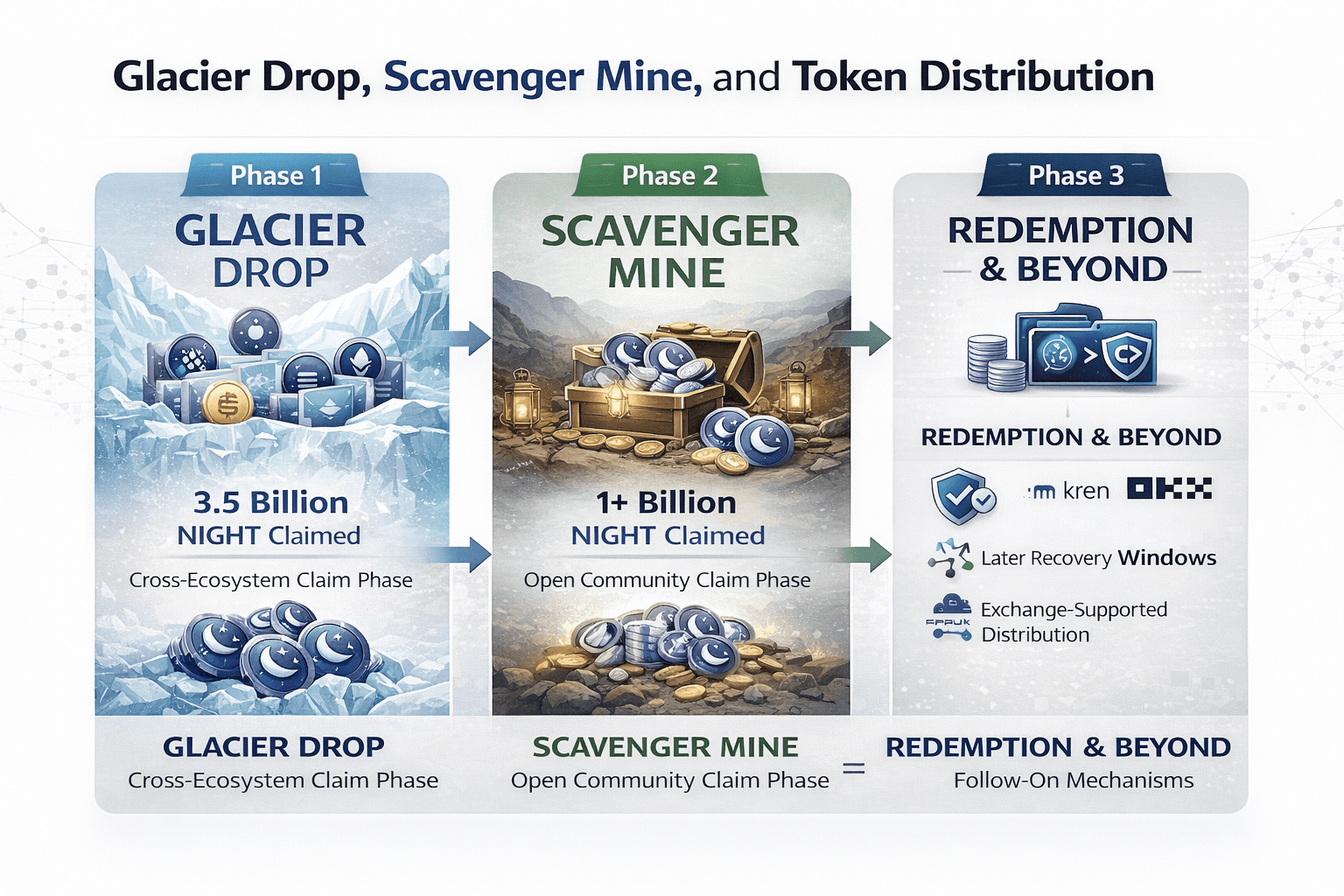
Midnight’s token distribution was designed as a multi-phase rollout rather than a one-shot airdrop.
 How Midnight Distributed NIGHT Across Chains And Users
How Midnight Distributed NIGHT Across Chains And UsersGlacier Drop, Clearly Explained
Glacier Drop was the first phase of Midnight’s cross-chain distribution event. It targeted eligible self-custodied holders across multiple ecosystems, including ADA, BTC, ETH, SOL, XRP, BNB, AVAX, and BAT, with claims tied to wallet eligibility rather than a narrow single-chain user base. That gave Midnight a wider initial reach than most token launches and made the first phase feel more like a network-wide distribution than a standard crypto airdrop.
The scale is the part that stands out. More than 3.5 billion NIGHT was claimed across over 170,000 addresses during Phase 1, which gave Midnight an unusually wide starting footprint before mainnet-era activity even began. To put it simply, Glacier Drop was the large, cross-ecosystem claim phase that seeded the initial community base.
What Scavenger Mine Was
Scavenger Mine was Phase 2 of the NIGHT distribution, and it widened participation far beyond the original eligibility model. Instead of being limited to pre-qualified self-custodied wallets, it opened participation much more broadly and turned the second phase into a larger community-access event.
Over 1 billion NIGHT was claimed across more than 8 million addresses, which gave Midnight a much wider participation base and pushed the overall distribution to an unusually large scale by industry standards. In practical terms, Scavenger Mine expanded distribution breadth, improved search visibility around the launch, and pushed NIGHT beyond a single-claim audience into a much larger public-facing event.
What Readers Need to Know Now
The part readers need to keep straight now is the follow-on mechanics. Redemption is the unlock and collection process tied to claimed allocations, while Lost-and-Found is the later phase for eligible participants who missed the earlier claim windows. Midnight has also said that exchange-facilitated distributions are part of this later flow, with names including Kraken, OKX, and Bitpanda appearing in official rollout communications.
So, the simple version is that Glacier Drop seeded the first wave, Scavenger Mine widened the second, and the collection path after that runs through Redemption, Lost-and-Found, and exchange-supported distribution where applicable. That is the structure worth remembering, because the headline numbers alone do not explain how the remaining NIGHT continues to reach users over time.
What Midnight Is Actually Good For
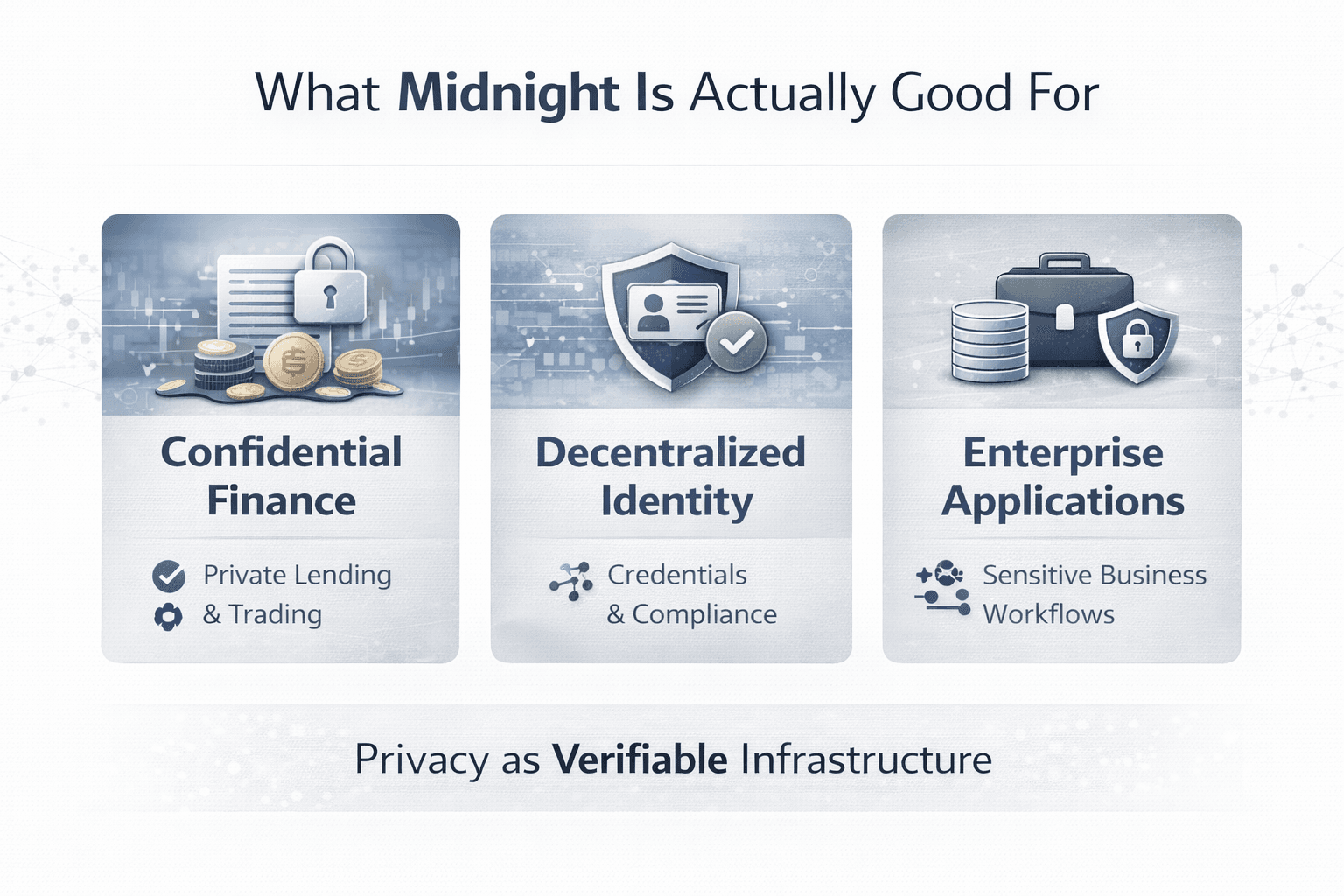
Midnight's strongest use cases sit in areas where public visibility creates friction, whether that means leaking financial positions, exposing user credentials, or forcing businesses to place sensitive operational data on a chain that was never designed for confidentiality.
 Use Cases Where Midnight’s Privacy Model Fits Best
Use Cases Where Midnight’s Privacy Model Fits BestConfidential Finance and DeFi
Midnight is a natural fit for confidential DeFi, especially in areas like private lending, confidential trading, and markets where concealed position sizes matter. On a normal public chain, collateral levels, transaction intent, and trading behavior are often visible before the market has finished reacting to them. That may be acceptable for fully open systems, but it is a poor fit for institutional finance, where visibility can distort behavior, invite unwanted scrutiny, or expose strategy.
That is where Midnight’s model becomes useful. If a lending or trading application can prove that rules were followed without disclosing the full underlying state, then the application becomes much more usable for participants who care about confidentiality as a functional requirement rather than a preference. In that setting, privacy is not cosmetic. It is part of the market structure.
Identity, Credentials, and Compliance Workflows
One of Midnight’s strongest real-world use cases sits in decentralized identity and compliance workflows. Many systems need to confirm facts like age, residency, accreditation, membership, or KYC and AML status, but they do not need unrestricted access to every document behind those claims.
Midnight’s architecture is well-suited to that kind of credentials layer because it supports proofs without full data exposure. A user could prove age verification without revealing a full birth record, show accreditation without exposing an entire financial profile, or satisfy an onboarding requirement without handing over a complete identity bundle. That is a much more workable model for compliance-heavy applications, because it narrows disclosure to what the counterparty actually needs.
Enterprise and Sensitive-Data Applications
Midnight also makes sense for enterprise blockchain use cases where transparency is helpful in theory but damaging in practice. That includes B2B payments, supply chain data sharing, and treasury operations where the parties involved may want shared verification without placing pricing, counterparties, or internal logic into open public view.
The same logic extends into healthcare data and legal documents, though those are best understood as adjacent examples rather than the entire thesis. The larger point is that many businesses rejected public-ledger models because data exposure came baked in. Midnight’s value is that it gives them another path: blockchain infrastructure that can preserve verification while handling sensitive information with more restraint.
Midnight vs Other Privacy Blockchains
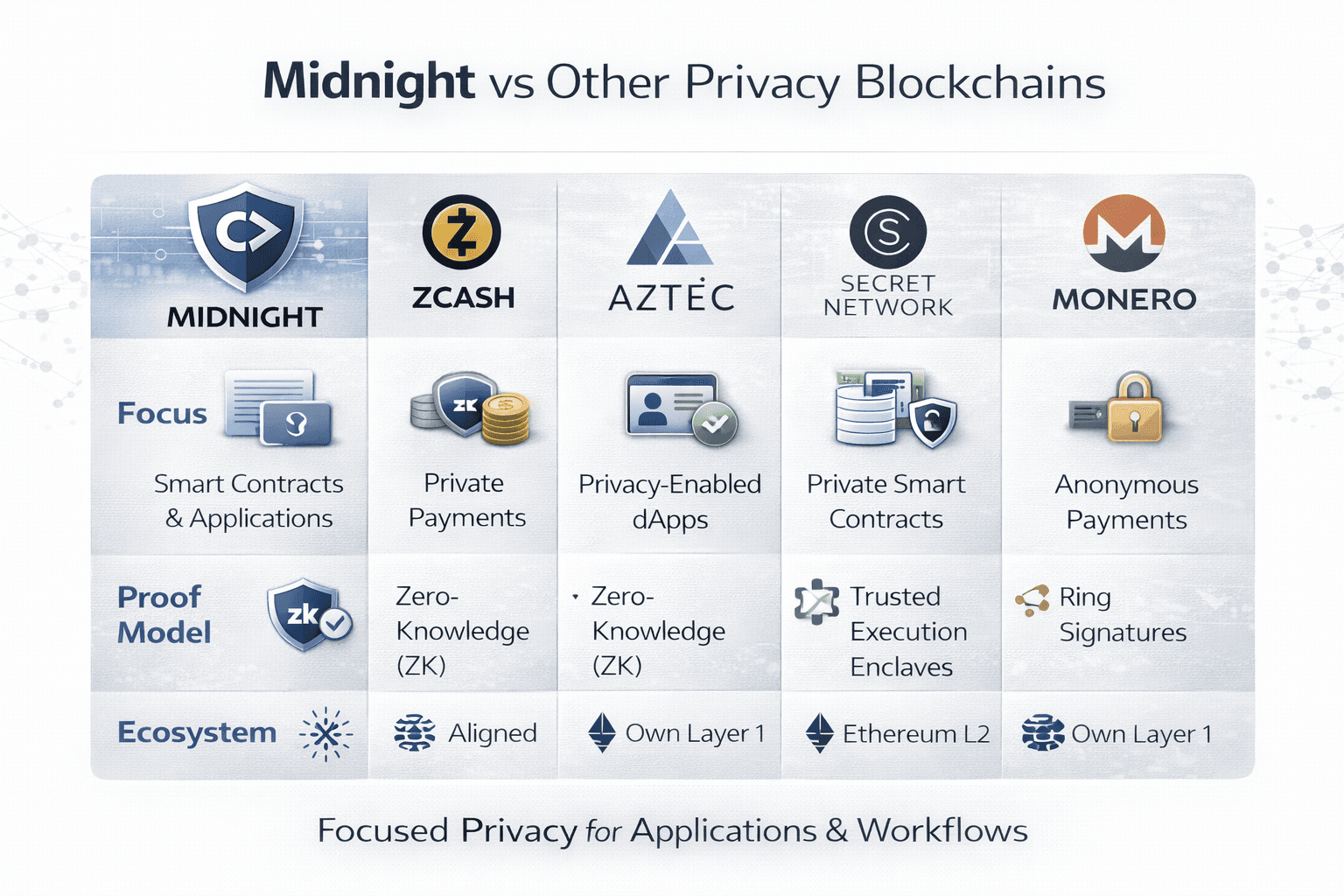
Midnight belongs in the privacy-blockchain conversation, but its position is narrower and more deliberate than many older projects in the category. The strongest comparison is not “which chain hides the most,” but what kind of privacy each system is built to deliver, where that privacy lives in the stack, and whether the design is aimed at transfers, applications, or compliance-heavy workflows.
 Where Midnight Sits In The Privacy Blockchain Market
Where Midnight Sits In The Privacy Blockchain MarketMidnight vs Zcash
Zcash is best known for shielded transactions and private payments. Its core strength is transaction privacy, where shielded addresses and encrypted transaction data protect balances, amounts, and transaction history from public view when users operate in the shielded model. That makes Zcash a strong reference point for private payments, but it is still a different category from Midnight’s programmable privacy approach.
Readers comparing privacy models may want to see our guide on how to buy Zcash in 10 minutes.
Midnight is aiming at privacy for applications, not only privacy for transfers. That means the comparison is less about which network offers stronger concealment for value transfer and more about what developers can build on top. Zcash’s center of gravity is shielded transactions, while Midnight’s pitch is that confidentiality should extend into smart contract behavior, private state, and selective disclosure inside application logic.
Midnight vs Aztec
Aztec is probably the closest comparison in ambition, because it is also trying to bring privacy to programmable applications instead of limiting privacy to payments. The difference is architectural and ecosystem-based. Aztec is framed as an Ethereum L2 zkRollup with private and public execution models connected to Ethereum, while Midnight is positioned as its own L1-style partner-chain network aligned with Cardano.
There is also a tooling difference worth naming clearly. Aztec’s developer stack centers on Noir, while Midnight’s centers on Compact. Both are trying to make privacy-aware development more practical, but they sit in different ecosystems and different execution models. Aztec extends Ethereum’s privacy frontier from an L2 angle, while Midnight is building a separate network identity around privacy-first infrastructure and its own economic system.
Midnight vs Secret and Monero
Secret Network takes a different route to confidentiality by leaning on a trusted execution environment, specifically Intel SGX in its current documentation, and more broadly on TEE-based confidential computing in SecretVM materials. Midnight, by contrast, is framed around a ZK-based model where cryptographic proofs carry more of the burden of verification without disclosure.
Monero sits in yet another lane. Its design is privacy-first in an anonymity sense, with privacy features such as stealth addresses built into the transaction model by default. Midnight is not aiming at that same anonymity-first posture. Its model is closer to selective disclosure, where privacy is preserved but disclosure can still happen in a controlled way when an application or regulated workflow requires it. That makes Midnight easier to describe as a compliance-oriented privacy infrastructure, while Monero remains the cleaner example of anonymity-centered digital cash.
Ecosystem, Partners, and Current Status
Midnight has moved out of the purely conceptual stage and into a more operational one. NIGHT has been live since December 2025, and the mainnet launched in March 2026, with the network moving through an early rollout model built around trusted operators before a later path toward deeper decentralization.
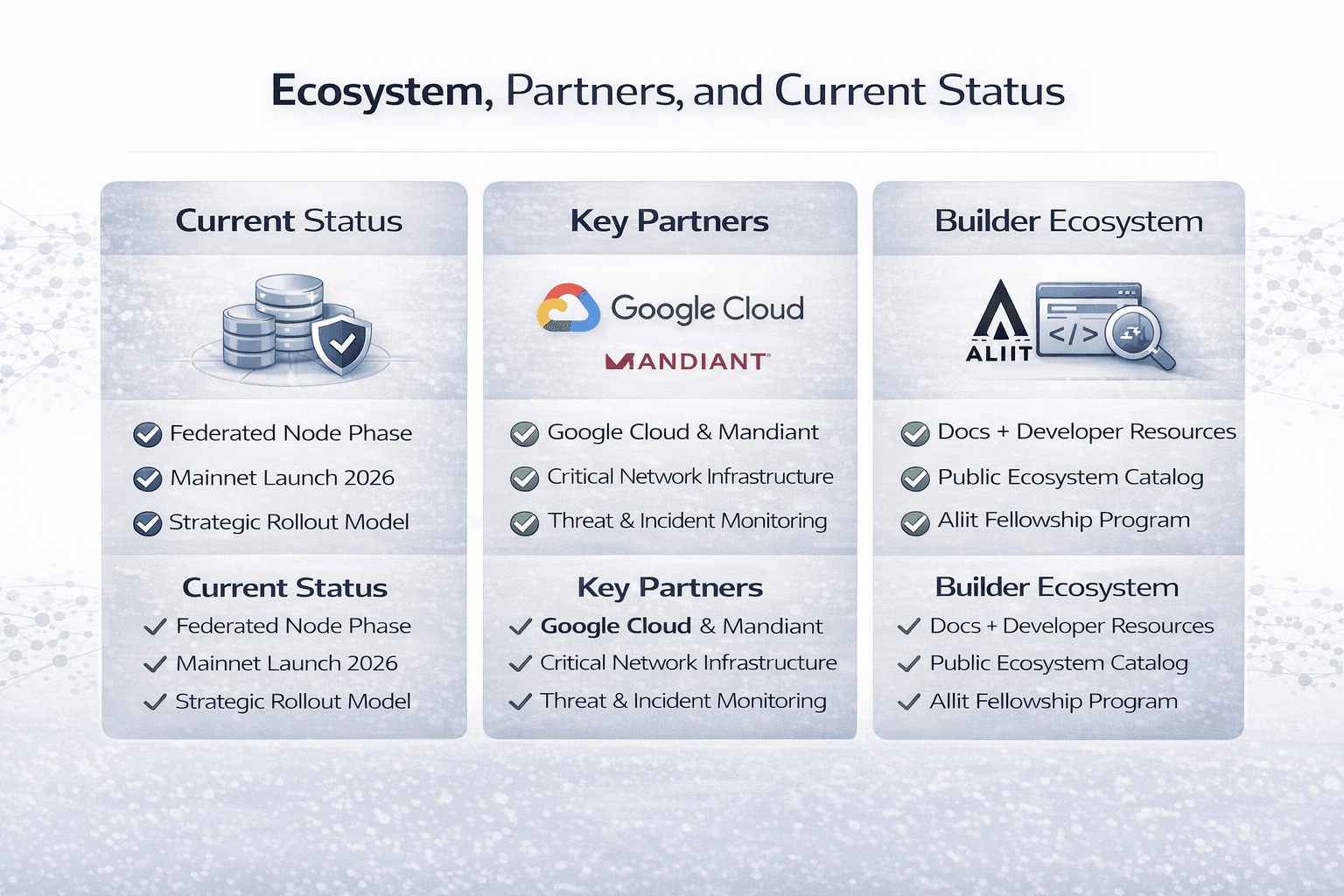 Midnight’s Rollout, Partners, And Builder Network Today
Midnight’s Rollout, Partners, And Builder Network TodayWhere Midnight Stands Now
Midnight is now live. At this stage, the focus shifts away from launch timing and toward actual network utility. Midnight’s messaging now centers on developer access, privacy-preserving applications, and real-world financial use cases such as confidential trading, private lending, institutional execution, tokenized assets, and programmable compliance.
Named Authority Signals
One of Midnight’s strongest credibility signals is its collaboration with Google Cloud. That relationship covers more than branding. Official Midnight material says Google Cloud will operate critical infrastructure for the network, including a federated node, while Mandiant contributes threat monitoring and incident response support. Midnight has also said its zero-knowledge stack will make use of Google Cloud Confidential Computing, which gives the partnership real infrastructure weight rather than surface-level ecosystem optics.
The other strong signal is the Midnight Summit. Midnight said the inaugural event brought together more than 450 builders, developers, and privacy advocates at the Old Royal Naval College in London. That matters because it shows the project is not operating as a closed research exercise. It has already started building a visible builder culture around its privacy-first positioning.
Builder Ecosystem
The builder side is now tangible enough to describe without hand-waving. Midnight has live docs, SDK-facing development resources, a public ecosystem catalog, and active GitHub pathways surfaced through its developer materials. That gives the project a more concrete builder story than many networks that speak in abstractions long before tools exist.
The Aliit Fellowship also matters here because it shows Midnight is investing in technical contributors, educators, and community builders rather than treating ecosystem growth as a vague future ambition. With Cohort 2 applications open as of March 2026, the builder ecosystem already has a visible support structure around learning, contribution, and practical onboarding.
Why Midnight Matters
Midnight matters because it tackles a real weakness in public blockchains. For a long time, most chains treated full transparency as the default. That works when open visibility helps trust. It stops working when businesses, institutions, and users need to protect sensitive data. Midnight is built around a different idea: privacy should be part of the system from the start, not something added later.
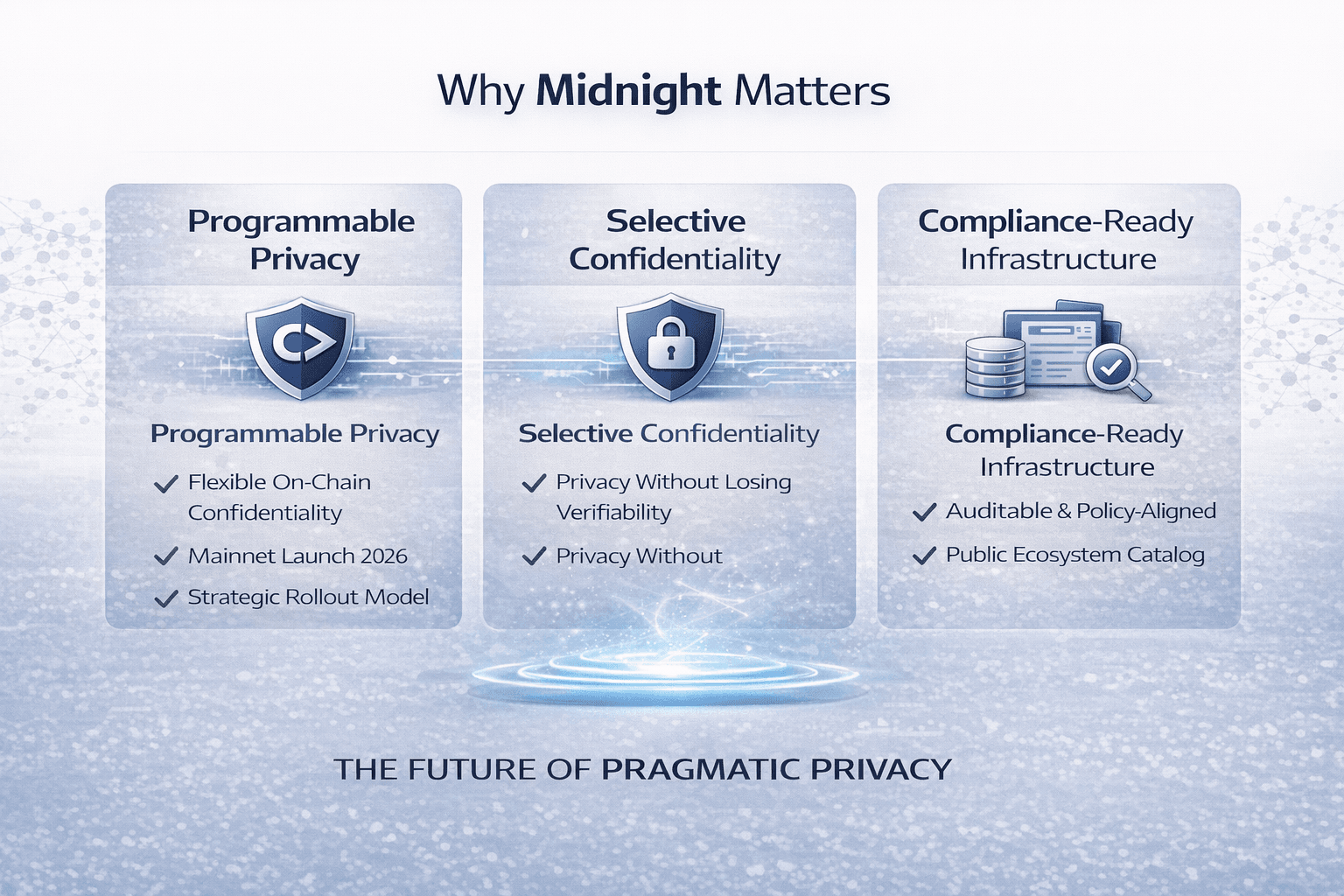 Why Privacy-Ready Infrastructure Gives Midnight Real Relevance
Why Privacy-Ready Infrastructure Gives Midnight Real RelevanceThe Bigger Design Shift
A lot of blockchain systems still assume that everything important should be visible on-chain. That made sense in the early days, but it also shut the door on many real-world use cases. Companies do not want to expose internal operations. Financial firms do not want to reveal their strategy in public. Identity systems cannot put personal data out in the open and call that progress.
This is why Midnight stands out. It points toward a version of blockchain that keeps verification, but gives applications more control over what gets revealed. That shift matters because many industries did not reject public ledgers. After all, they hated blockchain. They rejected them because the privacy trade-off was too costly.
Midnight’s Commercial Wedge
Midnight’s strongest edge is not that it is simply “more private” than another chain. Its stronger claim is that it makes privacy usable in compliance-heavy environments. That is a much more practical promise, because regulated industries do not need total secrecy. They need systems that protect data, allow controlled disclosure, and still support oversight when needed.
That is what gives Midnight a clearer commercial angle. It is trying to make compliance-ready privacy part of blockchain infrastructure itself. If that works, then sectors like finance, enterprise software, and identity systems start to look like a much better fit for public blockchain technology.
Our review of the top privacy coins helps frame where Midnight fits and where it differs.
Final Verdict
Midnight is one of the more thoughtful privacy projects in crypto because it is solving for a real business and infrastructure problem, not just chasing the idea of hidden transactions. The project understands that public blockchains become much harder to use once sensitive data enters the picture, and its answer is to make privacy something developers can build with, not something users have to bolt on later.
That said, the idea is stronger than the proof so far. Midnight has the design, the language, the token model, and the positioning. What it still needs, like every serious new network, is real application traction. The long-term case will depend on whether developers actually build useful products on it, whether enterprises trust the model, and whether the network can make privacy feel practical at scale.
Right now, Midnight looks less like a niche privacy chain and more like an attempt to make blockchain usable in places where transparency has always been a problem. If it delivers on that, it could matter far beyond the privacy category.





